
A marketing agency I worked with recently faced a familiar but frustrating problem. They would spend weeks crafting the perfect proposal, attach it to an email, hit send, and then... silence. They had no idea if the client opened it, who read it, or if their confidential pricing was being forwarded to competitors. This lack of control and visibility was not just a logistical headache; it was actively eroding their confidence and their clients' trust.
This scenario is incredibly common. Sending sensitive files into the digital void creates unnecessary risk. We needed a solution that provided not just delivery confirmation, but true insight and control. This is where we shifted from simple attachments to a more robust strategy focused on building trust through transparency and security.
Table of Contents
The Challenge: The Black Box of Email Attachments
The core issue was the complete loss of control the moment an email was sent. The agency's primary concerns were split into two main areas: a lack of engagement data and significant security vulnerabilities.
Losing Control and Flying Blind
Without any feedback mechanism, the sales team was operating in the dark. They couldn't tailor their follow-up because they didn't know if the prospect had even glanced at the proposal. Did the client focus on the creative concepts or skip straight to the pricing page? This guesswork led to inefficient follow-ups and missed opportunities.
The High Cost of Poor Marketing Proposal Security
Even more concerning was the risk of a data leak. Their proposals contained competitive pricing, unique strategies, and proprietary market research. In the hands of a competitor, this information could be devastating. Using standard email attachments offered no protection against unauthorized forwarding or sharing, putting their intellectual property at constant risk.
The Solution: Implementing a Secure Sharing Platform

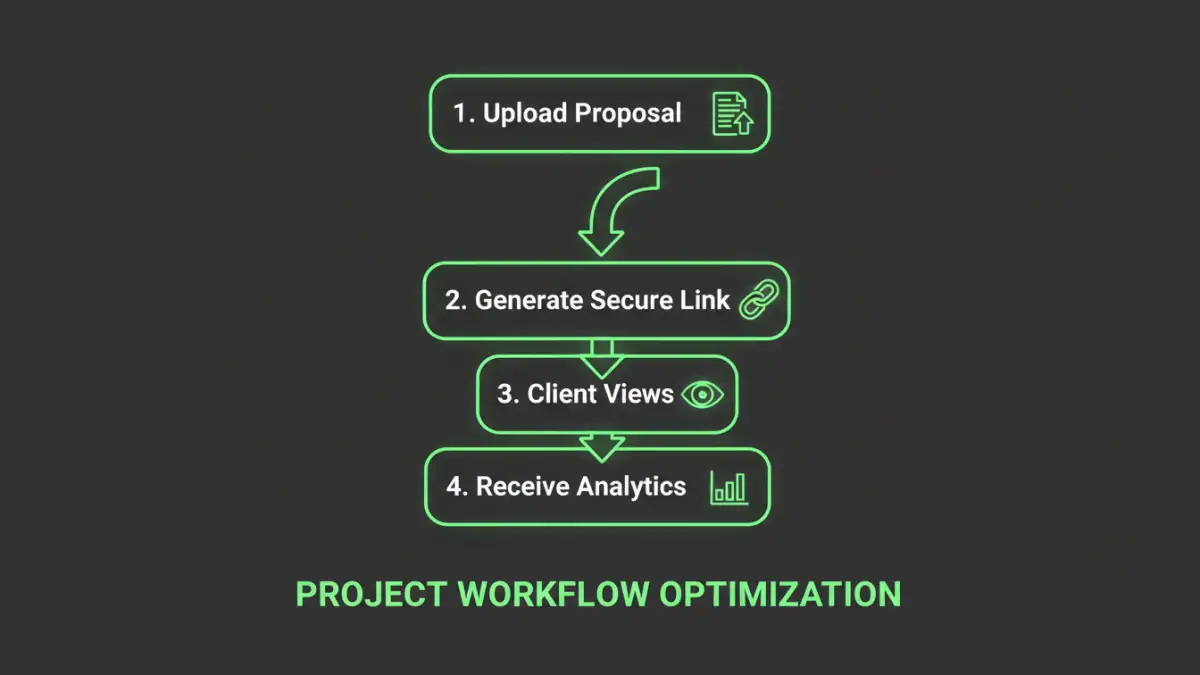
To address these challenges, we moved away from email attachments and implemented a dedicated platform for secure document sharing. Instead of sending the actual file, the agency began sending a unique, trackable link to a cloud-hosted version of their proposal.
Prioritizing Essential Features
We selected a tool that offered a specific set of features crucial for their workflow. This included password protection, restricting downloads, and setting link expiration dates. These simple controls immediately enhanced their marketing proposal security by ensuring only the intended recipient could access the information within a specific timeframe.
Integrating Confidential File Analytics
The game-changer was the analytics component. The platform provided real-time notifications the moment a document was opened. More importantly, it offered detailed, page-by-page analytics, showing how much time a recipient spent on each section. This data transformed their follow-up process from a shot in the dark to a strategically informed conversation.
The Results: From Uncertainty to Actionable Insight
The shift to a secure document tracking system yielded immediate and significant results. The impact was felt not only in their internal processes but also in their external client relationships.
Gaining a Competitive Edge with Data
The sales team could now see that a potential client spent ten minutes reviewing the project timeline but only thirty seconds on the budget page. This allowed them to proactively address potential scheduling concerns in their next call, demonstrating attentiveness and expertise. This level of insight helped them close deals faster by focusing on what truly mattered to the client.
Building a Foundation of Trust
Interestingly, clients noticed the enhanced security. Receiving a professional, branded, and password-protected link instead of a simple attachment conveyed a sense of professionalism and respect for their data. It sent a clear message: "We take the security of our shared information seriously." This small change became a powerful trust signal, strengthening relationships before a contract was even signed.
Key Lessons for Protecting Your Own Documents
This agency's success story offers valuable lessons for any business that shares sensitive information, whether it's proposals, financial reports, or legal documents. Effective client report protection is about more than just preventing leaks; it's about building confidence.
Start by evaluating your current process. If you're still relying on email attachments for critical documents, you're exposing your business to unnecessary risk and missing out on valuable data. Adopting a platform that provides control, security, and analytics is a strategic investment. It empowers your team with insights, protects your intellectual property, and, most importantly, shows your clients that you value and protect their partnership.
Document Sharing Method Comparison
| Method | Security Level | Analytics | Best For |
|---|---|---|---|
| Email Attachment | Very Low | None | Non-sensitive, casual communication |
| Standard Cloud Storage Link (e.g., Google Drive) | Low to Medium | Basic (views/downloads) | Internal collaboration, non-critical files |
| Encrypted Email | Medium | None | Sending a file securely with no tracking needed |
| Secure Document Tracking Platform | High | Advanced (page-level, time spent) | Sales proposals, financial reports, legal contracts |