
A few months ago, a partner at a mid-sized law firm reached out to me. They were facing a challenge that's become increasingly common: their methods for sharing sensitive client files were a patchwork of email attachments and consumer-grade cloud storage. They knew this was a significant risk, especially with growing concerns around client data protection and regulatory compliance. They needed a unified, defensible security strategy, and they needed it fast.
This case study outlines the journey we took together, from identifying critical vulnerabilities to implementing a comprehensive encryption framework. It's a practical look at how legal professionals can move from a position of risk to one of robust security, safeguarding their clients' most confidential information.
Table of Contents
The Challenge: Unsecured Digital Workflows
The firm's primary problem was a lack of standardized security protocols. Attorneys and paralegals were using various methods for confidential file sharing, from password-protected ZIP files sent via email to personal cloud accounts. This created multiple points of failure. An audit I helped conduct revealed several critical risks, including potential unauthorized access to discovery documents, contracts, and private client communications.
Their existing approach to law firm cybersecurity was reactive rather than proactive. They were relying on basic password protection, which is easily compromised, and had no way to track who accessed files or revoke access once a case was closed. The potential for a data breach was not just a technical problem; it was an existential threat to their reputation and client trust.
The Solution: A Multi-Layered Encryption Strategy
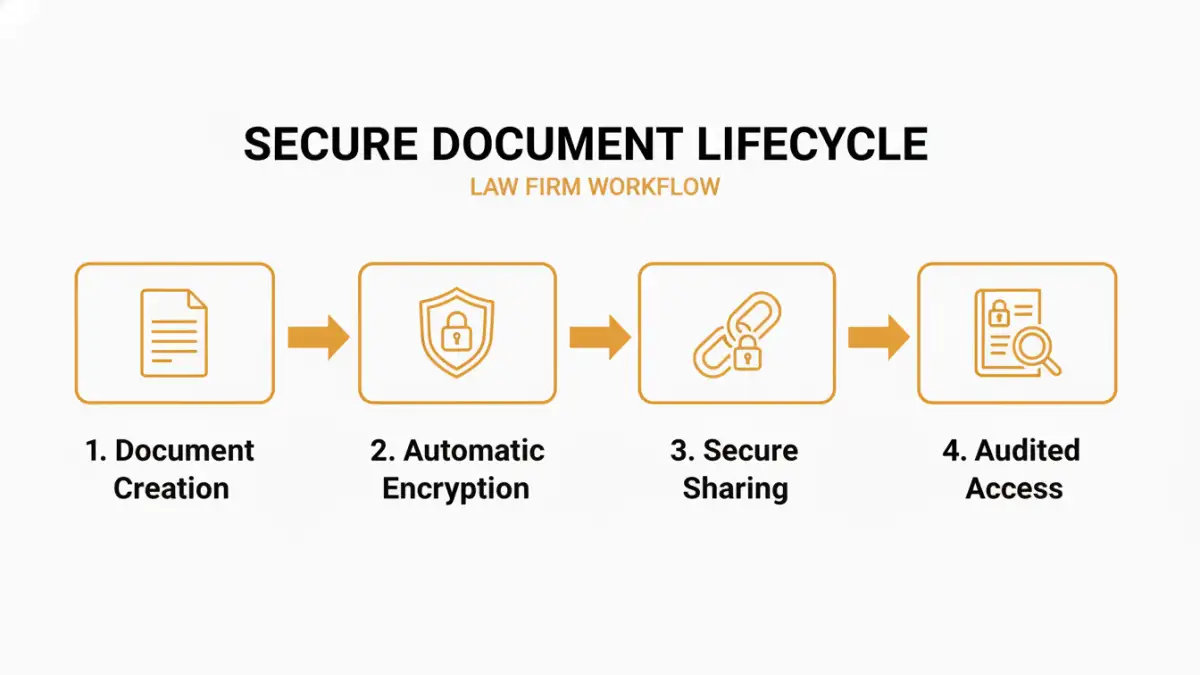
After evaluating their needs, we decided against a single-product solution. Instead, we designed a multi-layered strategy centered on end-to-end encryption for data both 'at rest' (stored on servers or hard drives) and 'in transit' (being sent over the internet). The goal was to make security seamless, so it wouldn't disrupt the fast-paced legal workflow.
Our plan had three core components: implementing a secure document management system (DMS) with built-in encryption, enforcing encryption on all company devices, and training staff on secure communication practices. This holistic approach ensured that from the moment a document was created to the moment it was archived, it was protected by strong cryptographic controls.
Choosing the Right Encryption Standard
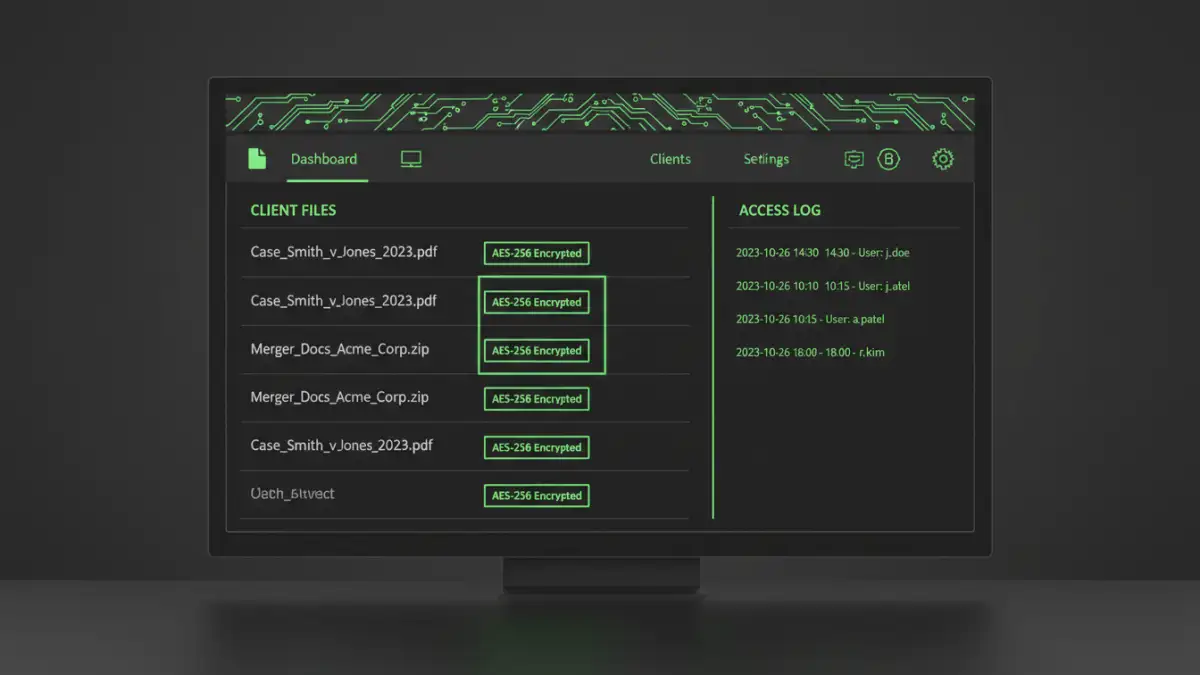
For legal document security, not all encryption is created equal. We opted for solutions that use AES-256, the same standard used by the U.S. government to protect classified information. This provided a high degree of confidence that the data would be computationally infeasible to crack. We also prioritized solutions that offered zero-knowledge encryption, meaning not even the service provider could access the firm's decrypted files.
Integrating with Existing Tools
A major factor for success was ensuring the new system worked with their existing software, primarily their case management platform and Microsoft Office suite. We chose a DMS that offered deep integration, allowing lawyers to save and encrypt documents directly from Word or Outlook. This minimized friction and encouraged adoption, which is often the biggest hurdle in any security rollout.
The Implementation Process
The rollout was phased over six weeks. Phase one involved encrypting all local and network drives using native tools like BitLocker for Windows and FileVault for macOS. This immediately protected data at rest. We established a clear policy requiring all firm-issued laptops and removable media to have full-disk encryption enabled.
Phase two was the deployment of the new DMS. We migrated their active case files first, working with a small pilot group of tech-savvy attorneys to iron out any workflow issues. Their feedback was invaluable for creating effective training materials. This pilot program helped build internal champions for the new system, which greatly smoothed the firm-wide transition. The firm's leadership made it clear that using the new system for confidential file sharing was mandatory.
The Results: Enhanced Security and Client Trust
The impact was immediate and significant. The firm now has a centralized, auditable system for managing client files. Every document is encrypted by default, and access is controlled through granular permissions. They can now confidently share discovery materials with opposing counsel or sensitive documents with clients through secure, expiring links instead of risky email attachments.
Beyond the technical improvements, the firm gained a powerful marketing and client-relations tool. They can now explicitly detail their robust client data protection measures in proposals and client meetings. This demonstrated commitment to security has become a key differentiator, helping them win business from clients who are increasingly security-conscious. Ultimately, implementing a strategy for **secure document encryption** wasn't just a defensive move; it became a competitive advantage.
Encryption Solution Comparison for Legal Firms
| Solution Type | Security Level | Ease of Use | Best For |
|---|---|---|---|
| Full-Disk Encryption (BitLocker/FileVault) | High (At Rest) | High (Set-and-forget) | Protecting lost or stolen devices. |
| Secure Document Management System (DMS) | Very High (At Rest & In Transit) | Moderate (Requires training) | Centralized, collaborative legal document security. |
| Encrypted Email Services | High (In Transit) | Moderate | Secure external communication with clients and counsel. |
| File-Level Encryption (e.g., 7-Zip) | Moderate | Low (Manual process) | Ad-hoc encryption of individual files for transfer. |