
A few months ago, I got a call from a small defense contractor. They were staring down the barrel of a CMMC Level 2 assessment and felt completely overwhelmed. Their main product was physical hardware, but the amount of digital paperwork—schematics, project plans, communications containing Controlled Unclassified Information (CUI)—was staggering. They knew they had to protect it for government contractor compliance, but didn't know where to start.
Instead of trying to boil the ocean, we developed a focused strategy that started with the data itself. By building a fortress around their documents first, they created a solid foundation that made the rest of the compliance journey manageable. This is their story.
Table of Contents
The CMMC Compliance Mountain: A Contractor's Dilemma
For many small and medium-sized businesses (SMBs) in the Defense Industrial Base (DIB), CMMC looks like an insurmountable peak. The 110 practices associated with Level 2 can feel abstract and disconnected from daily operations. This contractor was no different. They had a mix of on-premise servers and some cloud storage, with documents scattered across various shares and employee laptops.
Their primary challenge was the lack of visibility and control over their CUI. They couldn't confidently answer basic questions an assessor would ask: Where is all our CUI stored? Who has access to it? Is it encrypted at rest and in transit? This uncertainty created significant risk, not just for failing an audit but for a potential data breach that could jeopardize their contracts and reputation.
A Focused Strategy: Prioritizing Document Security

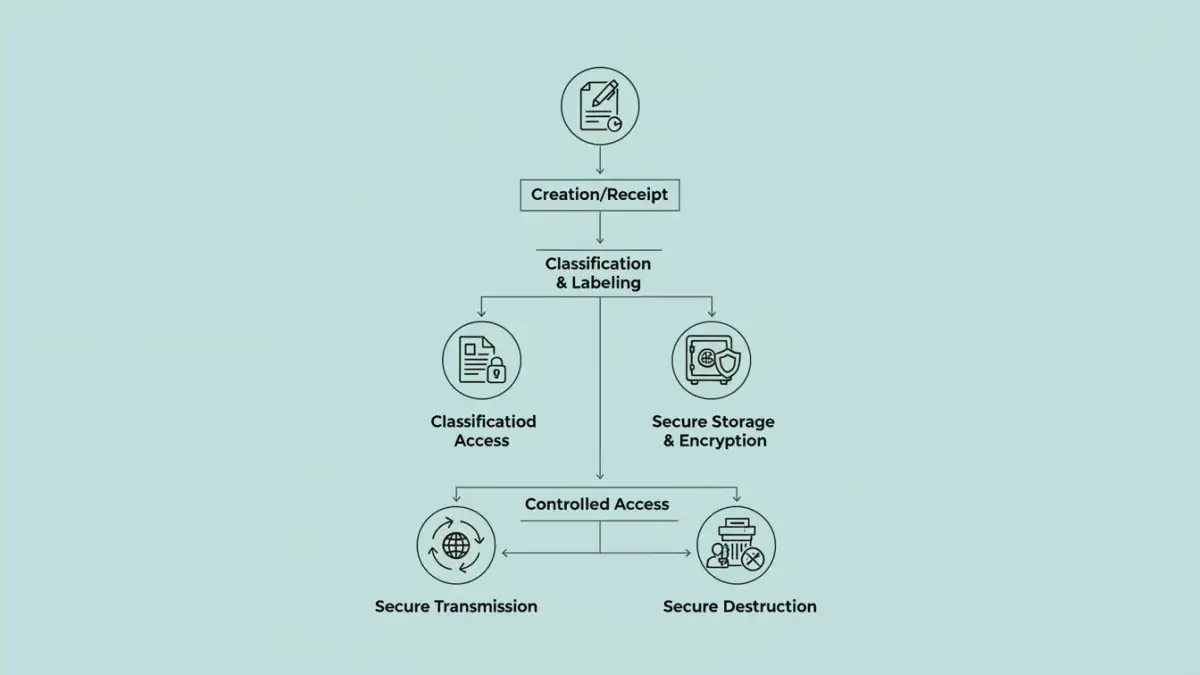
Our strategy was simple: start with the asset that matters most—the data. We decided to tackle CMMC by first establishing a comprehensive framework for defense document protection. By securing the documents, we could directly address a significant number of CMMC controls related to access control, identification, media protection, and system and communications protection.
This data-centric approach provided a clear, actionable path forward. Instead of worrying about every single network device or policy at once, we focused on the lifecycle of CUI. The goal was to ensure that from the moment a CUI document was created until it was securely archived or destroyed, it was protected, tracked, and controlled. This made the entire compliance effort more tangible and less intimidating.
Mapping Controls to Concrete Actions
We took the CMMC practices and translated them into specific document-related tasks. For example, control AC.L2-3.1.3, "Control CUI flow," became a project to implement a secure file sharing solution that prevents users from emailing CUI to unauthorized recipients. This practical mapping turned abstract requirements into a concrete project plan.
Implementing Robust Controls for CUI
With a clear strategy, we moved to implementation. This phase was about choosing the right tools and configuring them to enforce the policies we had defined. We broke the process down into manageable steps to ensure thoroughness and proper integration into their existing workflows.
The first step was data discovery and classification. We used a tool to scan their network and identify files likely to contain CUI based on keywords and patterns. Once identified, every file was tagged. This classification was crucial because you can't protect what you don't know you have. This process immediately improved their secure CUI handling capabilities.
End-to-End File Encryption in Practice
Next, we implemented a solution that provided persistent, end to end file encryption. This meant the file itself was encrypted, not just the hard drive it was stored on. If a file was accidentally copied to a USB drive or an insecure cloud service, it remained an unreadable, encrypted block of data without the proper credentials. We selected a FIPS 140-2 validated encryption module to meet DoD requirements, ensuring the cryptographic standards were up to par.
We also enforced multi-factor authentication (MFA) for accessing any system that stored or processed CUI. This added a critical layer of identity verification, making it much harder for an unauthorized user to gain access, even if they managed to steal a password. This combination of file-level encryption and strong authentication created a powerful security posture.
The Audit Outcome and Key Takeaways
When the CMMC assessment day arrived, the contractor was prepared. Because they had started with a strong cmmc document security foundation, they could confidently demonstrate control over their CUI. They provided the assessor with clear audit logs showing who accessed which files and when. They demonstrated how their encryption protected data at rest and in transit, and how their access policies were enforced by technology, not just trust.
They passed their Level 2 assessment. The key takeaway for them, and for any other contractor, is that CMMC compliance doesn't have to be an all-or-nothing scramble. By focusing on protecting your most critical asset—your CUI—you can build a compliant and secure environment from the inside out. This approach not only satisfies auditors but also provides genuine security that protects your business and our national security interests.
CMMC Document Security Control Comparison
| Control Area | Key Technology/Process | CMMC Practice Addressed | Implementation Effort |
|---|---|---|---|
| Access Control | Role-Based Access Control (RBAC) | AC.L2-3.1.5 | Medium |
| Encryption | AES-256 Encryption (FIPS 140-2) | SC.L2-3.13.11 | High |
| Auditing & Logging | SIEM / Log Management | AU.L2-3.3.1 | High |
| Data Labeling | CUI Marking / Watermarking | MP.L1-3.8.3 | Low |
| Media Protection | Encrypted USB Drives | MP.L2-3.8.1 | Medium |