
I recently worked with a university research department facing a critical challenge: their groundbreaking work was vulnerable. While collaborating on a multi-year project, sensitive data was being shared through a patchwork of personal cloud accounts and unencrypted emails. This not only risked accidental leaks but also exposed valuable intellectual property to potential theft, jeopardizing years of work and millions in funding.
This scenario is incredibly common in academia, where the need for open collaboration often clashes with the necessity for stringent security. The solution isn't to lock everything down but to implement smart, manageable security layers. This case study explores how we addressed their vulnerabilities head-on.
Table of Contents
The Challenge: Unsecured Intellectual Property in Academia
Academic institutions are treasure troves of innovation. From medical breakthroughs to new engineering patents, the intellectual property generated is immensely valuable. However, the very nature of academic work—collaboration, peer review, and the constant exchange of ideas—creates significant security risks.
The department I assisted was relying on standard file-sharing services with minimal oversight. Researchers, focused on their work, often chose convenience over security, creating a decentralized and porous data environment. This lack of centralized control made it impossible to track who had access to what, a nightmare for compliance and intellectual property protection.
Common Vulnerabilities in Research Workflows
We identified several key weak points. Preliminary findings were emailed as simple attachments, draft manuscripts were stored on personal laptops without encryption, and external partners were given broad access to shared folders. Each of these practices represented a potential point of failure for their research data security, leaving them exposed to both accidental data loss and malicious attacks.
Implementing a Layered Security Strategy

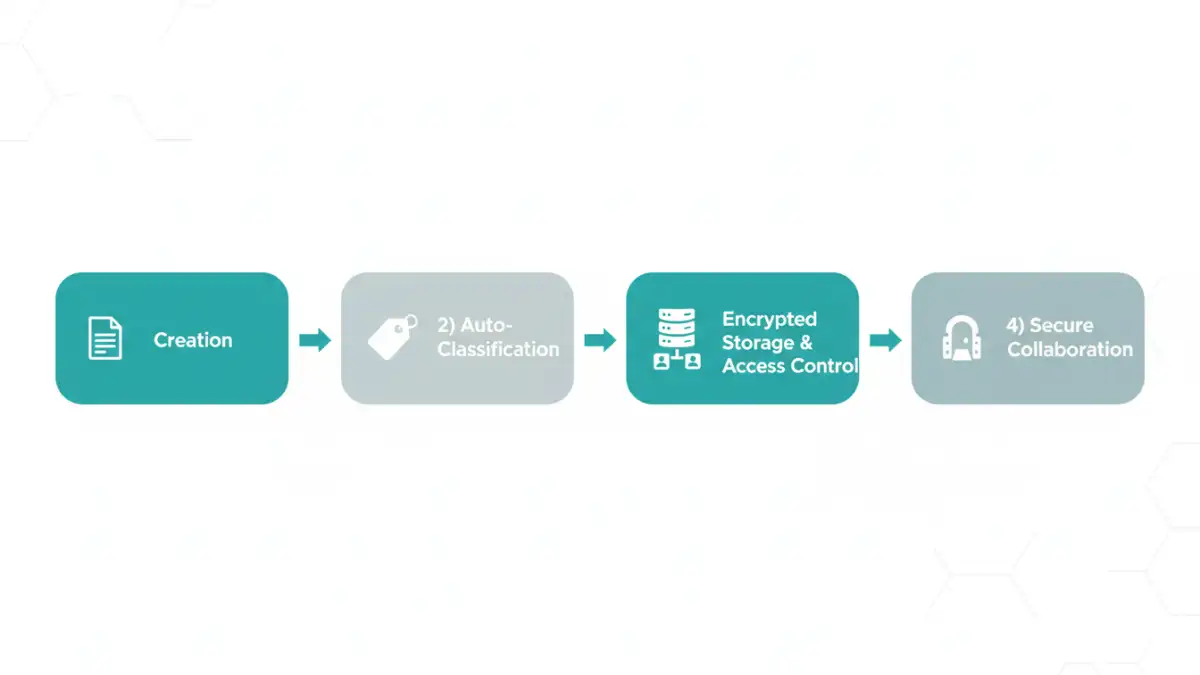
Our approach wasn't about finding a single piece of software to solve all problems. Instead, we developed a comprehensive strategy built on a foundation of clear policy and supported by technology. The goal was to make security an integrated part of the research workflow, not a cumbersome obstacle.
Establishing Centralized Encryption Policies
The first step was to create a data classification policy. We categorized data into tiers: Public, Internal, Confidential, and Highly Restricted. Each tier had a corresponding set of mandatory security requirements. For example, any data classified as 'Confidential' or higher required end-to-end encryption both at rest (on a server or hard drive) and in transit (when sent over a network). This policy became the backbone for all subsequent technical implementations.
Key File Encryption Controls for Research Data
With a clear policy in place, we implemented a suite of technical measures. These file encryption controls were designed to be as seamless as possible, ensuring researchers could continue their work with minimal disruption. The focus was on automation and centralized management to reduce the burden on individual users.
Granular Access Permissions and Auditing
We moved all sensitive project data to a secure, centralized repository. Here, we could enforce role-based access control (RBAC). A principal investigator might have full decrypt and edit permissions, while a graduate student researcher might only have read-access to specific data sets. Every access attempt, successful or not, was logged, creating a clear audit trail.
Automated Document Watermarking
To discourage unauthorized sharing of exported documents, we implemented an automated document watermarking system. Whenever a 'Confidential' document was downloaded or printed, a dynamic watermark was applied, including the user's name, email, and the date of access. This simple step acts as a powerful psychological deterrent against leaking sensitive information.
Secure Academic Collaboration Portals
Instead of emailing sensitive files, collaboration with external partners was moved to a secure portal. Partners were granted temporary, restricted access to specific files within the portal. This ensured the data never left the university's controlled environment, and access could be revoked instantly once the collaboration phase was complete. This drastically improved their secure academic collaboration capabilities.
The Impact: Measurable Improvements in Security
The results were transformative. Within six months, the university reported a complete halt to unauthorized data-sharing incidents within the pilot department. Researchers felt more confident sharing their work, knowing robust protections were in place. Furthermore, the clear audit trails made it simpler to demonstrate compliance with funding agency requirements and data protection regulations like GDPR.
By shifting from a reactive to a proactive security posture, the university not only protected its current research but also established a scalable framework to safeguard future innovations. It proved that strong research data security and productive collaboration can, and must, coexist.
Comparison of Implemented Security Controls
| Control Measure | Primary Function | Implementation Complexity | Best For |
|---|---|---|---|
| Granular Access Control (RBAC) | Limits data access based on user roles | Moderate | Protecting sensitive data within teams |
| Automated Document Watermarking | Deters unauthorized sharing and tracks origin | Low | Discouraging leaks of reports and manuscripts |
| Secure Collaboration Portals | Provides a controlled environment for external sharing | Moderate to High | Working with external partners and institutions |
| Data Classification Policy | Defines security requirements for different data types | Low (Policy), High (Enforcement) | Establishing a foundation for all security efforts |
| End-to-End Encryption | Protects data at rest and in transit | High | Securing highly restricted and confidential data |