
A few years ago, a client in the financial sector called me in a panic. They were facing a potential GDPR audit and realized their method for storing client reports was essentially a shared drive with loose permissions. The potential fines were staggering, and the immediate challenge was clear: how to secure years of sensitive data, fast, while demonstrating compliance. This situation perfectly illustrates a critical intersection of technology and regulation that many businesses now face.
The General Data Protection Regulation (GDPR) doesn't just suggest data security; it mandates it through principles like 'integrity and confidentiality'. For any organization handling the personal data of EU citizens, this isn't optional. It's a legal obligation with serious consequences.
Table of Contents
Why GDPR Makes Encryption a Core Requirement
While GDPR doesn't explicitly use the word "must" for encryption in every scenario, it comes incredibly close. Article 32 mandates that organizations implement "appropriate technical and organisational measures" to ensure data security. It then lists encryption of personal data as a prime example of such a measure. In the event of a data breach, having unencrypted personal data exposed is a fast track to maximum penalties.
From a practical engineering standpoint, encryption acts as a powerful safeguard. If a server is compromised or a laptop is stolen, encrypted data remains unreadable and useless to unauthorized parties. This single control can be the difference between a minor incident report and a multi-million-euro fine. It effectively renders breached data inert, protecting both the individuals whose data it is and the organization that stores it.
Core Principles for GDPR-Compliant Storage

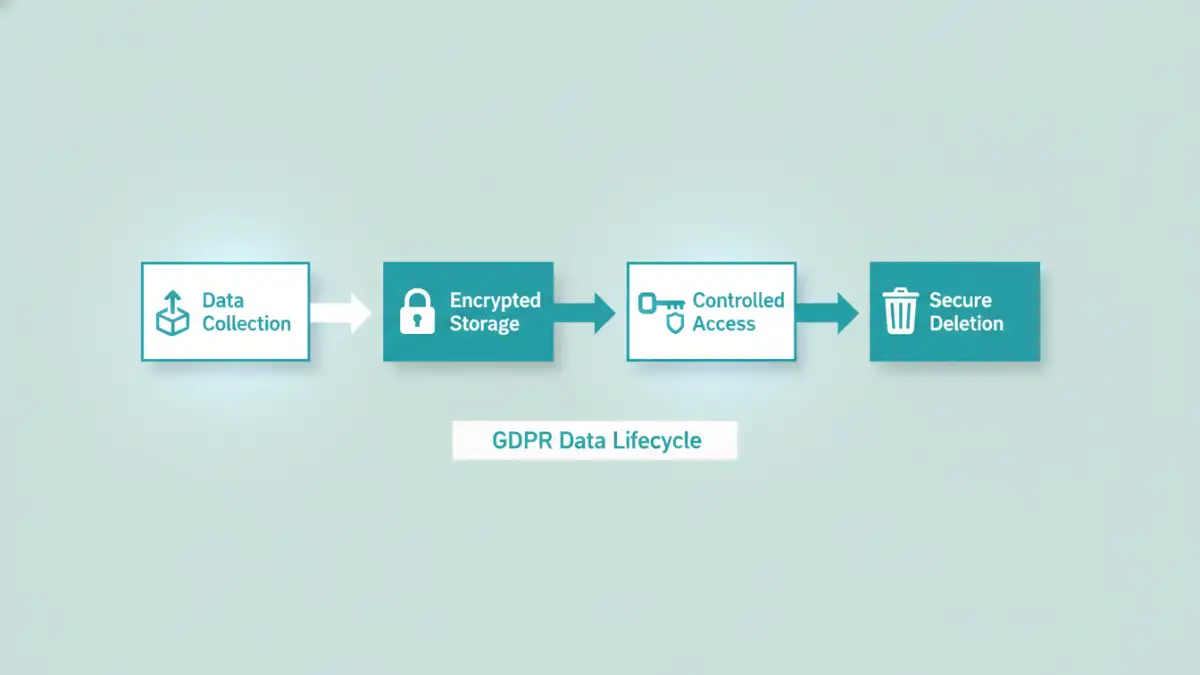
Implementing encryption for compliance isn't just about flipping a switch. It requires a thoughtful approach that covers the entire data lifecycle. For GDPR, two states of data are critically important: data at rest and data in transit. A robust system must address both.
Encryption at Rest
Data 'at rest' refers to information that is not actively moving between devices or networks. This includes files stored on a server's hard drive, in a cloud storage bucket, or on a database. Encrypting data at rest protects it from being accessed if the physical storage medium is compromised. This is fundamental for any system that holds sensitive files, such as financial reports or employee records.
Encryption in Transit
Data 'in transit' is data actively moving from one point to another, such as being sent over the internet or a local network. This is where protocols like TLS (Transport Layer Security) come into play, securing the connection between a user's browser and a web server. For any secure data room or client portal, ensuring all communication is encrypted in transit is non-negotiable to prevent eavesdropping or man-in-the-middle attacks.
A GDPR Business Case Study: Securing Client Data
Let's return to my client in the financial services industry. Their primary concern was ensuring top-tier client report security. They handled highly sensitive documents detailing investment portfolios and personal financial data, making them a prime target for both cybercriminals and regulatory scrutiny. Their existing system offered no audit trails and weak access controls.
Our solution was to implement a system built around the concept of encrypted document storage. We deployed a platform that enforced encryption at rest for every single file uploaded. We chose AES-256, a widely recognized and trusted encryption standard. This immediately addressed the risk of a server-level breach.
Next, we tackled access. We implemented a role-based access control (RBAC) system where each client could only see their own documents. Every download, view, or modification was logged in an immutable audit trail. This satisfied GDPR's principles of data minimization and accountability. This project became a successful GDPR business case study for them, demonstrating proactive compliance and building trust with their high-net-worth clientele. The result was more than just compliance; it was a competitive advantage.
Building a Compliant Secure Data Room
Creating a secure data room that aligns with GDPR principles involves several key technical steps. It’s not just about buying a piece of software; it’s about architecting a secure environment. First, choose a provider or build a system that offers end-to-end encryption, meaning data is encrypted on the client's device before being uploaded and only decrypted when accessed by an authorized user.
Second, robust key management is essential. Who holds the encryption keys? For maximum security, the service provider should not have access to the keys that decrypt customer data (a model often called zero-knowledge). This ensures that even company employees cannot access sensitive client files, strictly adhering to the principle of least privilege.
Finally, integrate strong authentication mechanisms like multi-factor authentication (MFA). This adds a critical layer of security to prevent unauthorized access even if user credentials are stolen. Combining strong encryption, strict key management, and MFA creates a formidable defense that stands up to regulatory inspection and real-world threats.
Encryption Strategies for GDPR Compliance
| Strategy | How it Works | GDPR Relevance | Best For |
|---|---|---|---|
| Encryption at Rest (File-Level) | Each individual file is encrypted with its own key. | Highly granular control. Protects data even if the storage system is compromised. | Secure data rooms, client report security systems. |
| Encryption at Rest (Full-Disk) | The entire storage volume (hard drive, SSD) is encrypted. | Protects against physical theft of hardware. A foundational security layer. | Laptops, servers, and mobile devices. |
| Encryption in Transit (TLS/SSL) | Creates a secure, encrypted channel between a client and a server. | Prevents eavesdropping on data as it travels across networks. | All web applications, APIs, and file transfer protocols. |
| Application-Level Encryption | Data is encrypted by the application before it is sent to the database or filesystem. | Provides zero-knowledge security, where the service provider cannot access the data. | High-security applications handling financial or health data. |