
A few years ago, a junior engineer on my team accidentally shared a document with sensitive API keys in a public channel. The tool we used had access controls, but a simple human error bypassed them. The fallout was immediate and stressful. It wasn't a failure of technology; it was a gap in our shared understanding of security. That incident taught me that the best firewalls and encryption tools are only as strong as the people using them.
Simply handing out security software and policies isn't enough. True information protection comes from creating an environment where security is a collective responsibility, not just an IT problem. It's about building a culture where everyone instinctively thinks about security before they click 'share'.
Table of Contents
Why Technology Alone Isn't Enough
We often invest heavily in technological solutions like data loss prevention (DLP) systems, advanced encryption, and access management platforms. While these tools are essential, they form just one layer of defense. Relying solely on them creates a false sense of security, ignoring the most unpredictable variable: human behavior.
The Human Element in Security
People are the gatekeepers of data. An employee who doesn't understand the 'why' behind a security policy is more likely to find a workaround for the sake of convenience. I've seen it happen when a cumbersome file-sharing process leads people to use personal, unsecured cloud accounts. The goal isn't to create rigid barriers but to foster a strong data security mindset where employees become active participants in protecting information.
From Compliance to Commitment
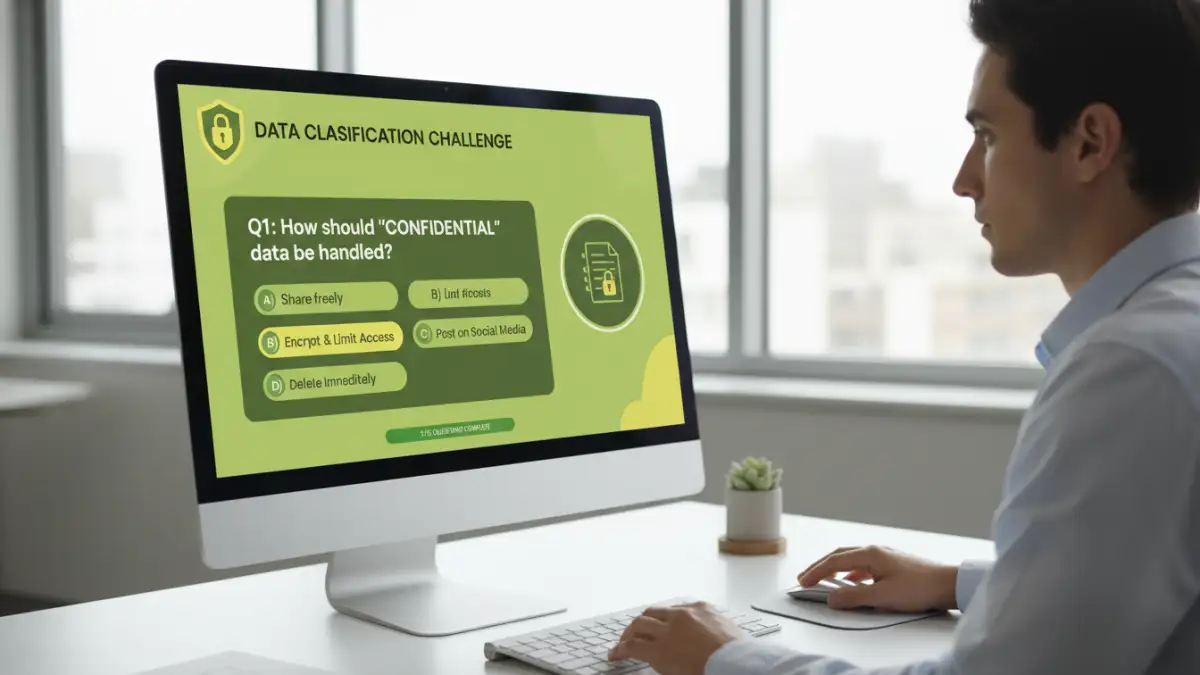
Many organizations treat security as a compliance checklist. Annual training is completed, policies are signed, and the box is ticked. This approach breeds apathy. A genuine document protection culture transforms this obligation into a shared commitment. It's the difference between begrudgingly following a rule and understanding its importance in protecting the company, its customers, and your colleagues.
Building Blocks of a Security-First Mindset
Creating this culture doesn't happen overnight. It requires a deliberate, multi-faceted approach that starts from the top and permeates every level of the organization. It's about making security intuitive, accessible, and a core part of the daily workflow.
Leadership Buy-In and Modeling
The most critical first step is getting leadership on board. When executives champion security, prioritize it in communications, and model secure behaviors themselves, it sends a powerful message. If a manager sends sensitive data over an unencrypted channel, it undermines any policy you try to enforce. Leaders must not only fund security initiatives but also actively participate in them.
Clear, Simple, and Accessible Policies
Overly technical, jargon-filled security policies are often ignored. I've had much more success with documents that are concise, written in plain language, and provide clear examples. Instead of a 50-page manual, create one-page guides for specific tasks, like 'How to Securely Share Client Data' or 'Identifying a Phishing Email'. Make these resources easily searchable on the company intranet.
Practical Steps to Cultivate a Security Awareness Culture
With the foundation in place, you can implement tangible initiatives that reinforce secure habits. The key is to make these activities engaging, continuous, and relevant to employees' day-to-day roles.
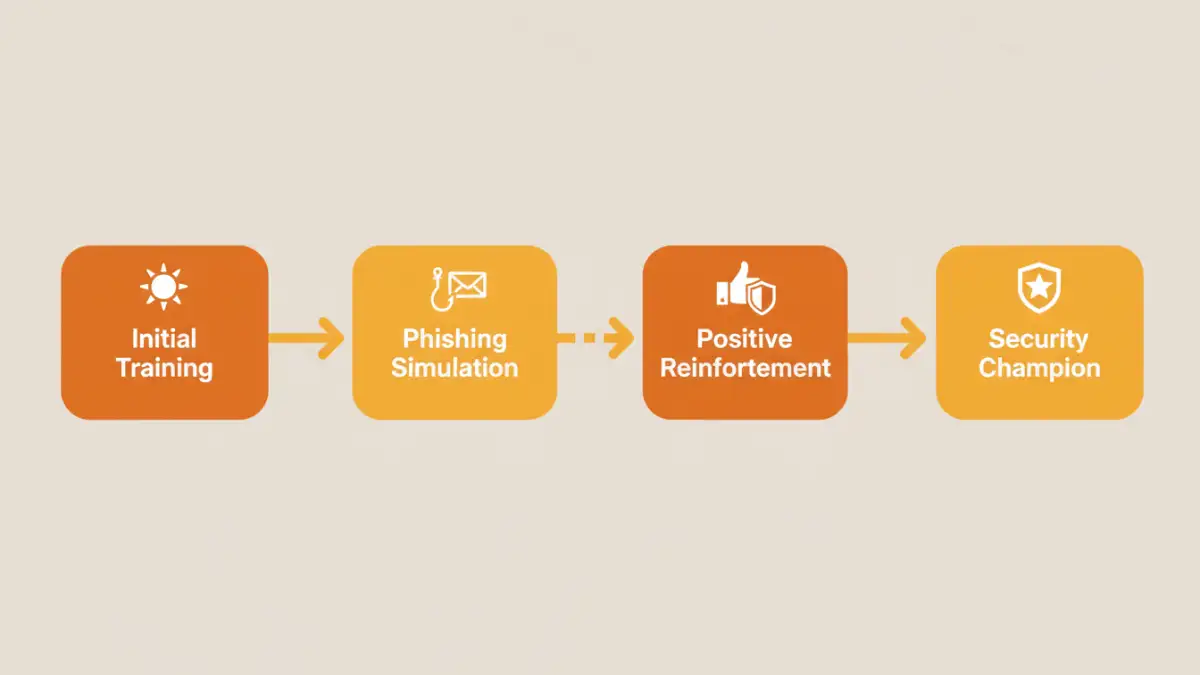
Continuous Training, Not Just Annual Check-ins
Forget the once-a-year, hour-long training video. Effective security education is an ongoing process. Use a mix of formats: short monthly security tip emails, interactive phishing simulations, and brief 'lunch and learn' sessions. For my team, we started a 'Security Tip of the Week' in our Slack channel, which sparked great discussions and kept information protection top of mind.
Empower Security Champions
Identify individuals within different departments who are passionate about security and empower them to be 'Security Champions'. These are not IT staff but rather peers who can answer basic questions, promote best practices, and act as a bridge between their team and the security department. This peer-to-peer model builds trust and makes security less intimidating.
Measuring Success and Sustaining Momentum
How do you know if your efforts are working? You need to track metrics that go beyond the number of security incidents. Look for positive indicators, such as the rate at which employees report phishing emails or the number of questions the Security Champions program fields.
Celebrate wins publicly. When a team successfully navigates a phishing simulation or an employee flags a potential threat, acknowledge their contribution. Positive reinforcement is far more effective than a culture of fear. By making security a shared achievement, you build the momentum needed to sustain a robust and resilient security posture for the long term.
Security Culture Initiative Comparison
| Initiative | Primary Goal | Implementation Effort | Best For |
|---|---|---|---|
| Phishing Simulations | Improve detection of malicious emails | Medium | Organizations of all sizes |
| Security Champions Program | Decentralize security knowledge | High | Growing or large organizations |
| Lunch & Learn Sessions | Educate on specific topics in an engaging way | Low to Medium | Reinforcing key concepts |
| Gamified Training Modules | Increase engagement with security content | Medium to High | Making compliance training less dry |
| Security Newsletters | Provide continuous, bite-sized updates | Low | Maintaining top-of-mind awareness |
| Public Recognition/Rewards | Encourage proactive security behavior | Low | Fostering positive reinforcement |