
A misplaced USB drive or an email sent to the wrong 'John Smith' can have consequences far beyond a typical corporate data breach. In the government sector, the stakes are exponentially higher. Information isn't just proprietary; it can be vital to national security, public safety, and diplomatic relations. The responsibility for protecting this data is immense.
Handling classified information requires a fundamentally different mindset and toolset than what's used in the private sector. It's not just about preventing a data leak; it's about adhering to stringent federal regulations and ensuring every action is auditable and defensible. This is where robust government document security protocols become non-negotiable.
Table of Contents
The Unique Challenges of Government Data
Working on systems for public sector clients, I quickly learned that commercial-grade security is often just the starting point. Government agencies face unique threats from sophisticated state-sponsored actors, and the data they protect has a much longer sensitivity lifespan. This environment demands a security posture that is both proactive and deeply integrated.
Understanding Classification Levels
Not all government data is the same. Information is categorized into specific levels based on the potential damage its unauthorized disclosure could cause. While the specifics can be complex, the main tiers are generally recognized as Confidential, Secret, and Top Secret. Each level mandates increasingly stringent handling, storage, and transmission protocols. A system designed for sharing Confidential documents is wholly inadequate for Top Secret intelligence.
The Role of Compliance Frameworks
Compliance isn't just a suggestion; it's the law. Frameworks like the Federal Information Processing Standards (FIPS), particularly FIPS 140-2/3 for cryptographic modules, and the Federal Risk and Authorization Management Program (FedRAMP) for cloud services, are critical. These standards provide a baseline for security controls, ensuring that any technology used has been rigorously vetted and approved for government use. Any solution for secure document sharing government agencies use must meet these benchmarks.
Core Pillars of Secure Sharing

Effective government document security rests on several foundational principles. These aren't just features but essential components of any trustworthy system designed for classified file sharing.
End-to-End Encryption (E2EE)
This is the bedrock. E2EE ensures that a document is encrypted on the sender's device and can only be decrypted by the intended recipient. No one in between—not the service provider, not an ISP, and not a malicious actor who intercepts the data—can read its contents. For any sensitive communication, data must be encrypted both 'at rest' (when stored on a server or drive) and 'in transit' (while moving across a network).
Granular Access Control and Identity Management
You can't protect what you can't control. A core tenet is the Principle of Least Privilege (PoLP), meaning users should only have access to the specific information required to do their jobs. This is enforced through strong identity verification, often using multi-factor authentication (MFA) with a physical token or smart card (like a CAC or PIV card), and role-based access controls (RBAC) that define who can view, edit, or share a document.
Approved Methods for Classified File Sharing
Sending a classified file as a simple email attachment is out of the question. Agencies rely on specific, vetted technologies and platforms designed for high-stakes environments. This is a critical area for secure collaboration and information dissemination.
Secure Government Portals
Many agencies use dedicated, accredited web portals for sharing sensitive information. These platforms operate on secure government networks (like SIPRNet or JWICS) and integrate directly with agency identity systems. They provide a centralized, auditable environment where users log in with strong credentials to access, collaborate on, and download documents. Everything is logged, from who accessed a file to when they viewed it.
Encrypted Email with PKI
For certain levels of communication, email can be used, but only with robust Public Key Infrastructure (PKI). This involves using digital certificates (often stored on a smart card) to encrypt and digitally sign emails. The encryption ensures confidentiality, while the digital signature verifies the sender's identity and confirms the message hasn't been tampered with, providing both integrity and non-repudiation.
Auditing and Lifecycle Management
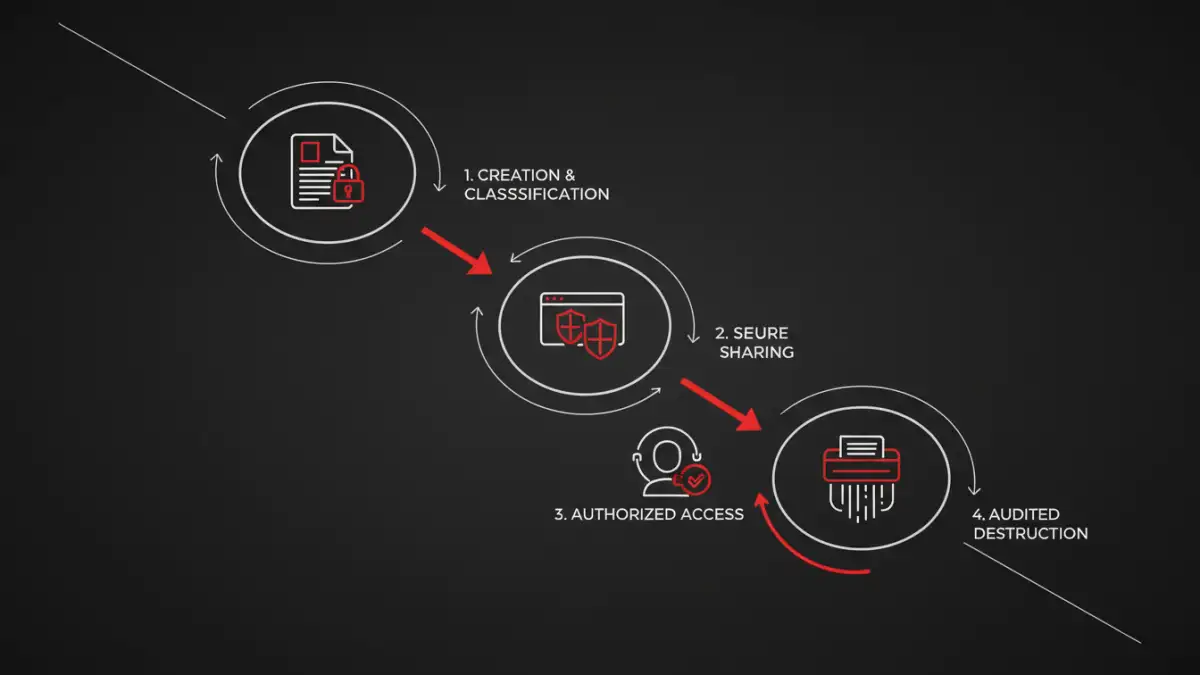
Sharing a document is just one part of its journey. True security involves managing its entire lifecycle, from creation to secure destruction. This is where many commercial tools fall short.
Every action related to a classified document must be logged in an immutable audit trail. This includes creation, access, modification, printing, downloading, and eventual deletion. These logs are crucial for security audits and for investigating potential incidents. Furthermore, documents must be managed according to strict data retention policies, ensuring they are securely and permanently destroyed when no longer needed, preventing data spillage or future unauthorized access.
Comparison of Secure Sharing Technologies
| Technology | Key Security Feature | Typical Use Case | Compliance Standard |
|---|---|---|---|
| Secure Portals (e.g., on SIPRNet) | Centralized access control, full audit trail | Inter-agency collaboration on Secret/Top Secret projects | Built to specific agency/IC standards |
| Encrypted Email (S/MIME) | End-to-end encryption, digital signatures | Sharing sensitive but unclassified (SBU) or Confidential information | PKI, FIPS 140-2 |
| FedRAMP Authorized Cloud | Vetted security controls, scalability | Storing and sharing Controlled Unclassified Information (CUI) | FedRAMP High/Moderate |
| Cross-Domain Solutions (CDS) | Securely transfers data between networks of different security levels | Moving data from a high-side network to a low-side network | NCDSMO Baseline |