
A legal team hits a wall during discovery: a crucial set of documents is locked behind passwords no one seems to have. This isn't just a technical hiccup; it's a potential roadblock to justice that can lead to sanctions, increased costs, and critical delays. From my work building data processing pipelines, I've seen firsthand how a single encrypted file can halt a multi-terabyte production.
Successfully navigating this challenge requires a blend of technical skill, legal strategy, and clear communication. It's about more than just 'cracking' a password; it's about maintaining a defensible process from start to finish.
Table of Contents
The Challenge of Encrypted Data in eDiscovery
Password protection is a double-edged sword. While essential for data security in day-to-day business, it becomes a significant hurdle in litigation. The core problem is that standard eDiscovery processing tools often flag these files as exceptions, unable to extract text or metadata. This can lead to incomplete productions and potential claims of spoliation if not handled correctly.
These encrypted files can be anything from password-protected PDFs and Office documents to encrypted ZIP archives or even entire disk images. Without a systematic approach, legal teams are left scrambling, trying to guess passwords or hoping the producing party cooperates. This reactive approach is inefficient and risky.
Initial Triage and Identification Strategies

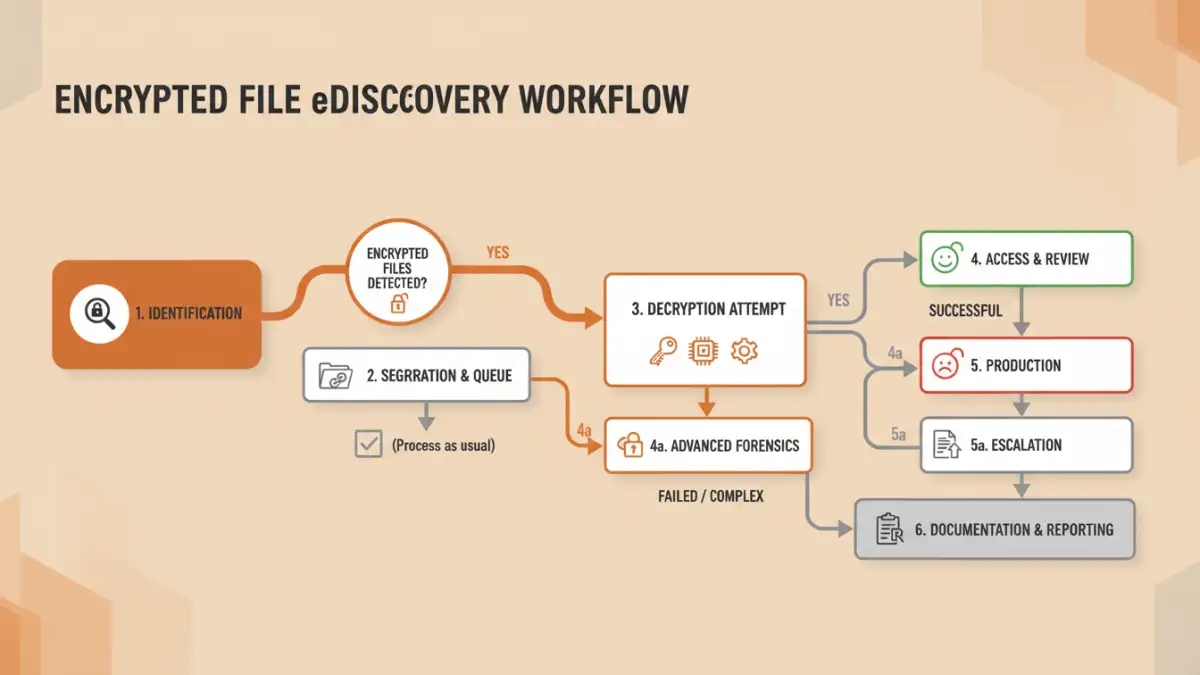
Before you can decrypt anything, you must first find and categorize all the protected files within a dataset. This is a critical step that informs your entire strategy. Throwing a massive dataset at a processing engine without preparation is a recipe for failure. A more methodical approach saves time and money.
Metadata Analysis
Modern eDiscovery platforms are quite good at identifying files that are likely encrypted, even if they can't open them. They do this by analyzing file headers and metadata. During the initial processing stage, these tools can generate an exception report that lists every file they failed to process. This report is your starting point—a map of all the locked doors in your data set.
Automated Scanning Tools
For more complex cases, specialized forensic tools can perform deeper scans. These tools go beyond simple exception reporting. They can identify the specific type of encryption used (e.g., AES-256 in a PDF vs. legacy Office encryption), which is crucial information for choosing the right decryption method. I've used scripts to automate this process, creating inventories that classify files by encryption type and owner, if known.
Methods for Unlocking Protected Files
Once you have an inventory of encrypted files, the next step is to attempt decryption. There isn't a single magic bullet; the right method depends on the encryption strength, the context of the case, and the resources available. This is where the intersection of legal tech for encrypted data and practical engineering comes into play.
Cooperative Decryption
The simplest and most defensible method is to ask for the password. This is typically done through a meet-and-confer process where parties agree on protocols for handling encrypted data. The producing party should be compelled to provide all known passwords for relevant files. Documenting these requests and responses is vital to show you've made a good-faith effort.
Forensic Decryption Techniques
When cooperation fails or passwords are unknown, forensic methods are the next step. This is where specialized software comes in. These tools can employ several techniques:
- Dictionary Attacks: Using a list of common words, phrases, and known passwords associated with the custodian.
- Brute-Force Attacks: Systematically trying every possible combination of characters. This is computationally expensive and can take days, weeks, or even years for strong passwords.
- Hybrid Attacks: A combination of dictionary and brute-force methods, such as adding numbers or symbols to dictionary words.
These processes require powerful hardware and expertise. It's not something you run on a standard laptop. We're talking about dedicated servers or cloud computing resources to accelerate the process of unlocking files for discovery.
Legal and Technical Considerations
Attempting to decrypt files isn't just a technical exercise; it's fraught with legal implications. Every action must be logged and defensible in court. The chain of custody is paramount. You must be able to prove that the file you decrypted is identical to the original, with its metadata intact.
This is why using established forensic data recovery tools is so important. They are designed to work on copies of evidence and maintain detailed logs of every action taken. Simply running a random password-cracking tool from the internet is not a defensible process and could compromise the integrity of your evidence.
Best Practices for Modern Legal Teams
The best way to handle the problem of ediscovery password protected files is to anticipate it. Proactive planning can save enormous headaches down the road.
- Update ESI Protocols: Your Electronically Stored Information (ESI) protocols should explicitly address how encrypted and password-protected files will be handled. Specify that the producing party must decrypt files or provide the necessary passwords.
- Collaborate with IT/Forensics Early: Don't wait until you have a problem. Involve your IT department or a forensics expert at the beginning of the discovery process. They can help you identify potential issues and build a sound technical workflow.
- Document Everything: Keep a detailed log of every encrypted file identified, the methods used to attempt decryption, communications with the opposing party, and the final outcome. This documentation is your proof of diligence.
Decryption Method Comparison
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Cooperative Request | Legally defensible, low cost, fastest method. | Relies on cooperation from the opposing party. | The first step in all cases. |
| Dictionary Attack | Faster than brute-force if password is simple. | Ineffective against complex, non-dictionary passwords. | Cases where custodian password habits are known. |
| Brute-Force Attack | Guaranteed to find the password eventually. | Extremely time-consuming and computationally expensive. | Short passwords or when all other methods fail. |
| Forensic Software Suites | Defensible process, detailed logging, multiple attack vectors. | Requires specialized software and expertise; can be costly. | Most corporate and legal eDiscovery workflows. |