
With data breaches becoming more sophisticated, the standards that protect our sensitive information must evolve. For anyone working with government agencies or in highly regulated industries, the term FIPS is likely familiar. It represents the gold standard for validating the effectiveness of cryptographic hardware and software. Recently, we've seen a major shift from a standard that served us for nearly two decades to a new, more robust framework.
This transition from FIPS 140-2 to FIPS 140-3 marks a significant compliance update for cybersecurity. It’s not just an incremental change; it modernizes the requirements to address today's threat landscape. Understanding this shift is crucial for ensuring the tools and processes we use for document encryption meet the highest federal security standards.
Table of Contents
What Exactly is FIPS 140-3?
FIPS, which stands for Federal Information Processing Standard, is a series of U.S. government standards that specify requirements for cryptography modules. FIPS 140-3 is the latest iteration, officially replacing its predecessor, FIPS 140-2. At its core, this standard is designed to ensure that the hardware, software, and firmware components that handle encryption do so in a verifiably secure manner.
Think of it as a rigorous certification process. A product claiming FIPS 140-3 validation has undergone extensive testing by an accredited third-party lab to prove its cryptographic algorithms are implemented correctly and that the module itself is tamper-resistant. This isn't just about using strong encryption like AES-256; it's about the entire module's lifecycle, from key generation and management to its operational integrity.
From FIPS 140-2 to 140-3: Key Changes
The transition to FIPS 140-3 was driven by the need to align with international standards and address modern security challenges. One of the most significant changes is its direct reference to two ISO/IEC standards: 19790:2012 and 24759:2017. This alignment helps streamline validation for vendors operating globally.
Other key changes include more stringent requirements for authentication mechanisms and stricter rules around non-invasive physical security. For software modules, there are now more explicit requirements for integrity testing during operation. These updates collectively raise the bar for what is considered secure, forcing vendors to re-evaluate and often re-engineer their cryptographic solutions.
Why FIPS 140-3 Matters for Your Documents

When you encrypt a sensitive document, you're placing trust in the underlying cryptographic module. Whether it's a PDF with financial data or a Word document containing intellectual property, the encryption's strength is paramount. Using a FIPS-validated module provides a high degree of assurance that the encryption won't be easily broken due to a flawed implementation.
For organizations handling government data, using FIPS-validated cryptography is often a contractual and legal requirement. This applies to everything from cloud storage providers to the software used for government file encryption on local workstations. The move to FIPS 140-3 means that over time, all these systems will need to adopt modules validated against this newer, tougher standard to remain compliant.
The Role of Cryptographic Module Validation
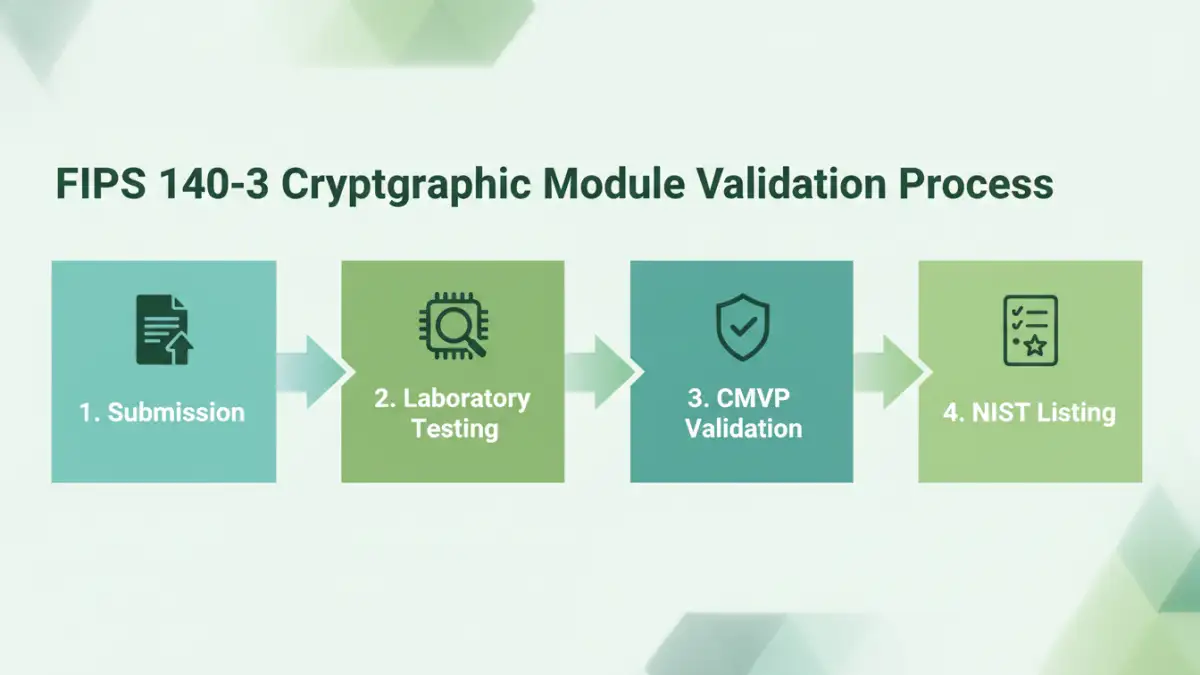
The heart of FIPS is the Cryptographic Module Validation Program (CMVP), a joint effort between the U.S. National Institute of Standards and Technology (NIST) and the Canadian Centre for Cyber Security. This program is what gives the standard its teeth. A vendor can't simply claim FIPS compliance; they must submit their module to a CMVP-accredited laboratory for rigorous testing.
This validation process examines everything from the physical casing of a hardware module to the source code of a software library. It ensures that cryptographic keys are protected, that the module behaves as expected in error states, and that it provides the security services it claims. For anyone concerned with fips 140 3 document security, choosing products that have successfully completed this validation is a critical step.
Practical Implications for Software and Systems
In my work, I've seen firsthand how these standards impact development cycles. Achieving FIPS validation is a lengthy and expensive process. Developers can't just drop in a standard encryption library; they must use a specific, validated version and ensure it's integrated according to strict guidelines. Any deviation can invalidate the certification.
For end-users and IT administrators, this means being diligent about software choices. When selecting a document management system, a secure email client, or even an operating system, it's important to check the vendor's FIPS status. Look for their CMVP certificate number and confirm it applies to the version of the software you are using. A feature might be labeled 'FIPS-compliant,' but true security comes from using a validated module.
Preparing for a FIPS 140-3 World
While FIPS 140-2 validations are no longer being issued, existing certificates remain active for five years. This creates a transition period where both standards will coexist. However, the direction is clear: all new cryptographic modules seeking validation must meet the FIPS 140-3 requirements. Organizations should start planning for this shift now.
This involves auditing current systems to identify which rely on FIPS 140-2 validated modules and creating a roadmap for upgrading them. Engage with your software vendors to understand their plans for FIPS 140-3 validation. By proactively managing this compliance update, you can ensure a seamless transition and maintain the highest level of security for your sensitive data without interruption.
FIPS 140-2 vs. FIPS 140-3 Comparison
| Area of Focus | FIPS 140-2 Requirement | FIPS 140-3 Requirement | Impact on Document Security |
|---|---|---|---|
| Core Standard | Based on NIST's custom requirements. | Aligns with international standards (ISO/IEC 19790 & 24759). | Promotes interoperability and a global security baseline. |
| Authentication | Allowed for some operator-based authentication. | Requires stronger, identity-based authentication for higher levels. | Reduces risk of unauthorized access to cryptographic functions. |
| Module Integrity | Startup self-tests were the primary focus. | Introduces requirements for conditional self-tests during operation. | Ensures the encryption module remains uncorrupted while in use. |
| Physical Security | Focused on tamper evidence and resistance. | Adds requirements for non-invasive attack mitigation. | Provides better protection against sophisticated physical attacks. |
| Validation Status | Submissions closed as of September 2021. | The current standard for all new cryptographic module validation. | Organizations must procure products validated under the new standard. |