
The old 'castle-and-moat' security model, where we trusted everyone inside the network firewall, just doesn't work anymore. With remote work, cloud services, and countless devices, the 'inside' of the network is everywhere. I've seen firsthand how a single compromised internal account can lead to a massive data breach because access controls were too permissive once a user was past the initial barrier.
This is where the concept of Zero Trust comes in, fundamentally changing our approach to security. It operates on a simple but powerful premise: never trust, always verify. Every single request for access must be authenticated and authorized, regardless of whether it originates from inside or outside the network perimeter. This shift is one of the most impactful secure document sharing trends we're seeing today.
Table of Contents
The Flaw in Traditional Document Security
For years, we relied on perimeter security. Think of it like a fortress with a strong wall and a single gate. Once you were inside, you were generally trusted and could move around with relative freedom. In the digital world, this meant using VPNs and firewalls. If a user connected via the VPN, they were 'in' and could often access wide swaths of the company's shared drives and resources.
This model is inherently flawed in a collaborative environment. It creates a large, soft interior that, if breached, gives an attacker extensive access. Sharing a document often meant granting access to an entire folder, creating unnecessary risk. The system was built on location-based trust, not on a continuous verification of identity and context.
Perimeter-Based Vulnerabilities
The primary weakness is implicit trust. Once credentials are stolen or an internal device is compromised, the attacker has the keys to the kingdom. We've seen this play out in countless breaches. The security model doesn't account for insider threats or attackers who have successfully bypassed the perimeter defenses. It's a binary, all-or-nothing approach to access that lacks nuance.
Understanding Zero Trust Architecture
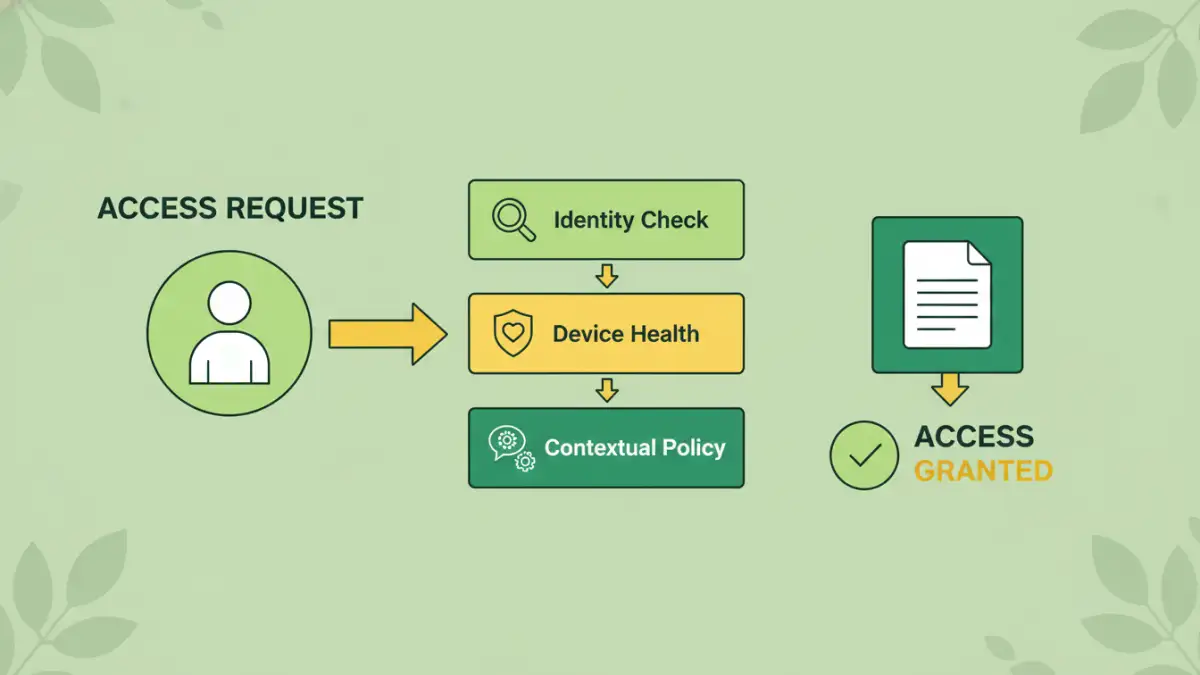
A Zero Trust architecture flips the traditional model on its head. It assumes that the network is always hostile and that a breach is inevitable or has likely already occurred. Therefore, no user or device is automatically trusted. Instead, trust is established on a per-session basis through rigorous verification.
The core tenets are simple: verify explicitly, use least privileged access, and assume breach. Every access request is treated as if it's from an untrusted network. It must be authenticated and authorized against a set of dynamic policies that consider user identity, device health, location, and the sensitivity of the data being requested. This continuous verification is the heart of the model.
The Principle of Least Privilege in Action
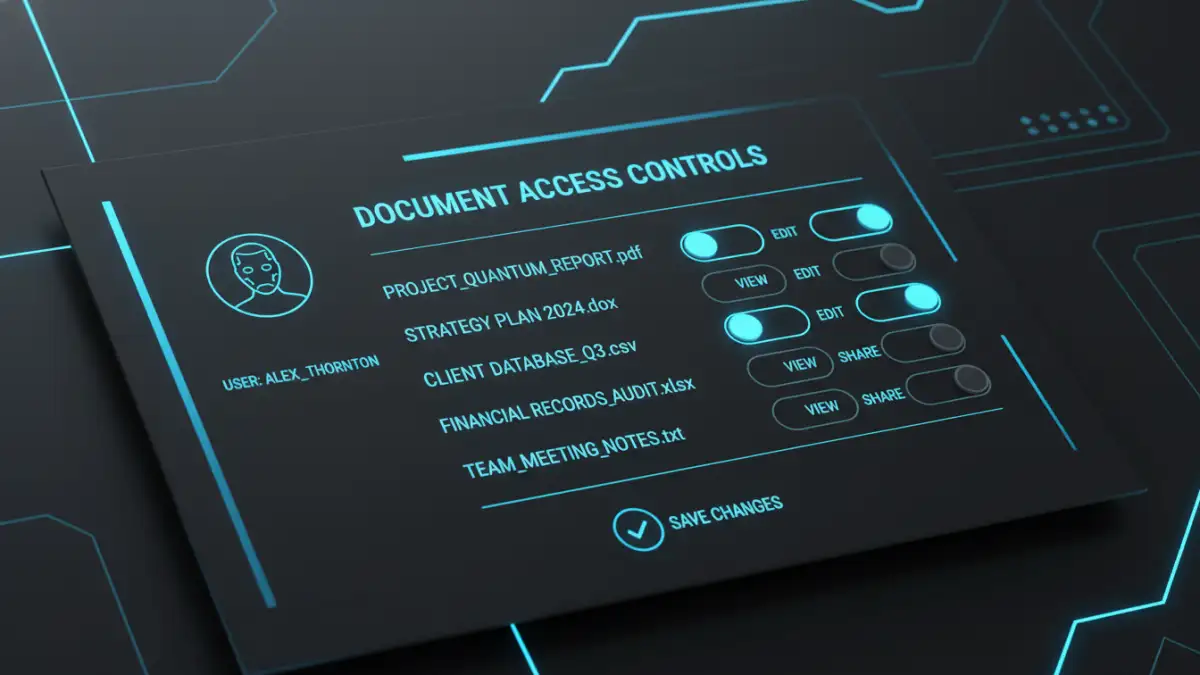
One of the most powerful components of Zero Trust is the principle of least privilege. This means giving a user the absolute minimum level of access required to perform their job, and nothing more. For document sharing, this is a game-changer. Instead of giving an accountant access to the entire 'Finance' folder, you grant them time-bound, view-only access to a specific Q3 report from a verified corporate device.
If that accountant's credentials were to be compromised, the attacker's access would be limited to that single document, for that specific time frame, dramatically reducing the potential damage. This granular document access control is something I've helped implement, and it effectively shrinks the potential attack surface around your most sensitive data.
How Zero Trust Transforms Document Sharing
Applying Zero Trust to document sharing moves security from the folder level down to the individual file level. Access is no longer a static permission but a dynamic decision made in real-time. This creates a much more resilient and intelligent system for secure file collaboration.
Imagine a user trying to open a sensitive M&A document. A Zero Trust system would check who they are (MFA), what device they're using (is it company-managed and patched?), where they are connecting from (is it a risky location?), and what they are trying to do (view, edit, or download). Access is only granted if all policy checks pass. If the user later tries to access the same file from a personal phone on public Wi-Fi, the request could be automatically blocked.
Dynamic and Context-Aware Policies
The real power lies in context. Policies are not static; they adapt. For example, a policy might allow an employee to edit a strategy document from their corporate laptop during business hours but switch to read-only access if they log in late at night from an unfamiliar IP address. This context-aware enforcement ensures security is maintained without completely blocking productivity.
Implementing Zero Trust for Collaboration
Adopting a Zero Trust model isn't about flipping a single switch; it's a strategic shift. It starts with identifying your most sensitive data and understanding who needs access to it and under what circumstances. From there, you can begin to implement the technologies that enable this model.
Key components include a strong Identity and Access Management (IAM) solution to act as the central authority for user identity. Multi-Factor Authentication (MFA) is non-negotiable, as it provides a critical layer of verification. Finally, technologies like micro-segmentation can be used to create secure zones around applications and data, further limiting lateral movement in the event of a breach.
Comparison: Traditional vs. Zero Trust Document Security
| Security Aspect | Traditional 'Castle-and-Moat' Model | Zero Trust Model |
|---|---|---|
| Trust Basis | Implicit trust once inside the network perimeter. | No implicit trust; every request is verified. |
| Access Control | Broad, network-level access (e.g., access to entire folders). | Granular, per-resource access (e.g., access to a single file). |
| Authentication | Typically a single authentication event at the perimeter (VPN login). | Continuous authentication and authorization for every session. |
| Threat Assumption | Assumes the internal network is 'safe'. | Assumes breach; the network is always considered hostile. |
| Policy Enforcement | Static policies based on user role and location. | Dynamic, context-aware policies (device health, time, location). |
| Vulnerability | High risk of lateral movement after a breach. | Lateral movement is significantly restricted. |