
With the constant evolution of cyber threats, the standards that define 'secure' must also evolve. For anyone working in software development, especially within regulated industries, the publications from the National Institute of Standards and Technology (NIST) are not just suggestions—they are the benchmark for security. When NIST updates its guidance, it signals a shift in the entire security landscape that we all need to pay attention to.
Recently, there have been significant movements in these cryptographic standards, particularly concerning how we should approach document and data encryption. These aren't just academic exercises; they have real-world consequences for the systems we build and maintain. Failing to keep pace can leave sensitive data vulnerable and organizations non-compliant.
Table of Contents
What is NIST and Why Do Its Standards Matter?
NIST is a non-regulatory agency of the U.S. Department of Commerce that develops and promotes measurement standards and technology. In the world of cybersecurity, its Computer Security Resource Center (CSRC) publishes the Special Publications (SP) 800 series, which are essentially the gold standard for information security in the federal government.
While these government security standards are mandatory for federal agencies, their influence extends far beyond. Industries like finance, healthcare (HIPAA), and critical infrastructure widely adopt NIST frameworks to build robust security postures. When a client asks if our encryption is 'strong enough,' citing compliance with the latest NIST publications is often the most definitive answer we can give.
Key Updates in Recent NIST Publications

The cryptographic landscape is not static. Two major areas of focus in recent NIST activities have been preparing for the quantum computing threat and refining the use of existing algorithms like the Advanced Encryption Standard (AES).
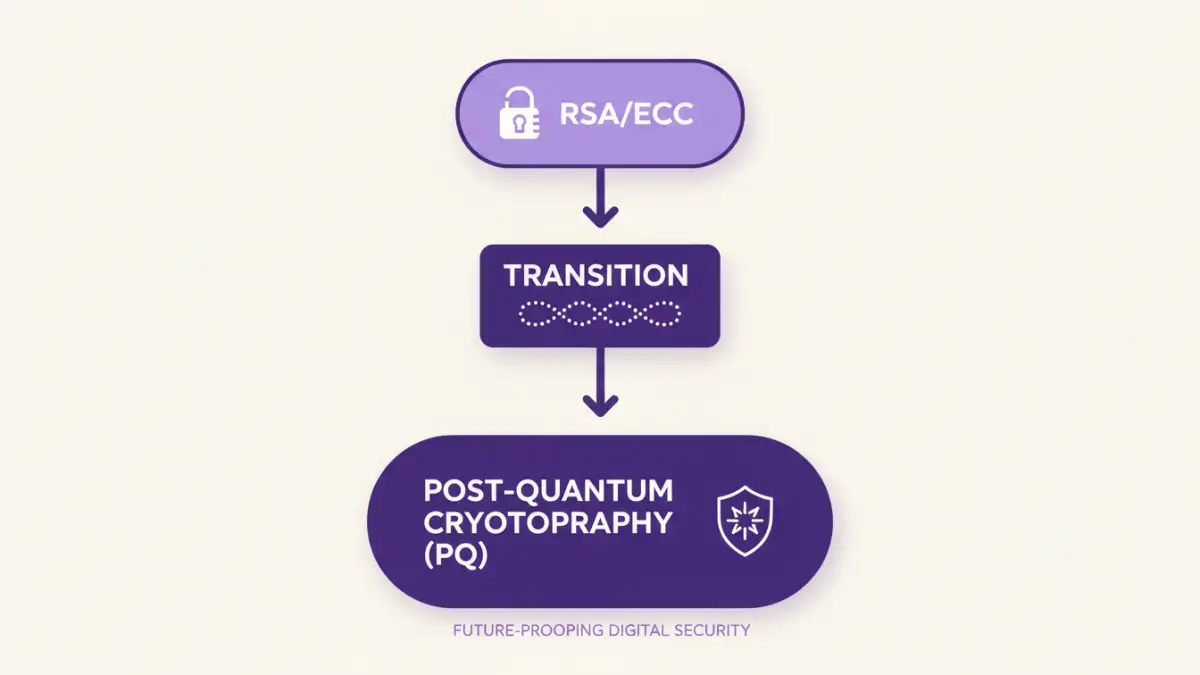
The Push Towards Post-Quantum Cryptography (PQC)
Perhaps the most significant development is NIST's project to standardize quantum-resistant cryptographic algorithms. The concern is that future quantum computers will be powerful enough to break currently used public-key algorithms like RSA and ECC. To counter this, NIST has selected a suite of PQC algorithms for standardization, such as CRYSTALS-Kyber for key establishment and CRYSTALS-Dilithium for digital signatures. While we are still in the early phases of adoption, developers should start becoming familiar with these new primitives and planning for a crypto-agile future.
Refinements in AES Modes and Key Management
The AES encryption update guidance from NIST continues to evolve. While AES itself remains secure, the focus has shifted to its modes of operation. NIST strongly recommends authenticated encryption modes like AES-GCM (Galois/Counter Mode) over older modes like CBC (Cipher Block Chaining). AES-GCM provides both confidentiality and integrity, preventing certain types of attacks that CBC can be vulnerable to if implemented incorrectly. Furthermore, publications like SP 800-57 provide critical guidance on cryptographic key management, covering the entire lifecycle from generation to destruction.
Practical Implications for Software Developers
These updates aren't just for cryptographers; they directly impact our day-to-day work. On a recent project dealing with sensitive financial documents, we had to perform a full audit of our cryptographic libraries. We discovered we were using a library that defaulted to an older, non-authenticated mode of encryption. Citing the latest NIST guidance was key to getting the resources to migrate to a modern, FIPS-validated cryptographic module that supported AES-GCM out of the box.
The takeaway is clear: always check that your tools and libraries are current and configured to use recommended algorithms and modes. Relying on default settings is a risk. For projects requiring federal compliance, using a FIPS 140-3 validated module is non-negotiable. This ensures the cryptographic implementation has been rigorously tested against NIST's standards.
Implementing Secure File Encryption with NIST Guidance
Applying these standards correctly is crucial for effective secure file encryption. It's more than just picking an algorithm; it's about building a secure system around it. A core principle I always follow is to never attempt to invent your own cryptographic protocols. The risk of subtle but catastrophic flaws is just too high.
Instead, leverage high-level, well-vetted libraries that handle the complexities for you. When encrypting a document, your process should follow NIST-recommended practices: use a cryptographically secure random number generator to create a strong encryption key, encrypt the data using AES-256-GCM, and then securely manage that key. Key management is often the weakest link, so follow NIST's lifecycle guidance: protect keys at rest, limit their usage, and have a plan for rotation and eventual destruction.
NIST Cryptographic Publications Overview
| Publication | Primary Focus | Key Takeaway for Developers |
|---|---|---|
| SP 800-53 | Security and Privacy Controls | Provides a catalog of controls needed for system security, including those for cryptography. |
| SP 800-57 | Key Management | Offers comprehensive guidance on the entire lifecycle of cryptographic keys. Essential reading. |
| SP 800-38 Series | Block Cipher Modes of Operation | Defines the approved modes for algorithms like AES. Confirms the recommendation for authenticated modes like GCM. |
| FIPS 140-3 | Cryptographic Module Validation | The standard for validating cryptographic modules. Use modules certified under this standard for high-security applications. |
| PQC Standardization | Quantum-Resistant Cryptography | Introduces the next generation of public-key algorithms. Start planning for future integration. |