
The regulatory landscape for cybersecurity is constantly shifting, and the latest updates from the SEC are a significant development for any public company. These aren't just minor tweaks; they represent a fundamental change in how organizations must approach and report on their security posture, especially concerning sensitive financial data.
Table of Contents
What Are the New SEC Cybersecurity Rules?
The U.S. Securities and Exchange Commission (SEC) recently adopted new rules that create a more standardized and aggressive framework for cybersecurity disclosures. At their core, these regulations are built on two main pillars: rapid incident reporting and transparent governance. The goal is to provide investors with more timely and consistent information about a company's cyber risks and incidents.
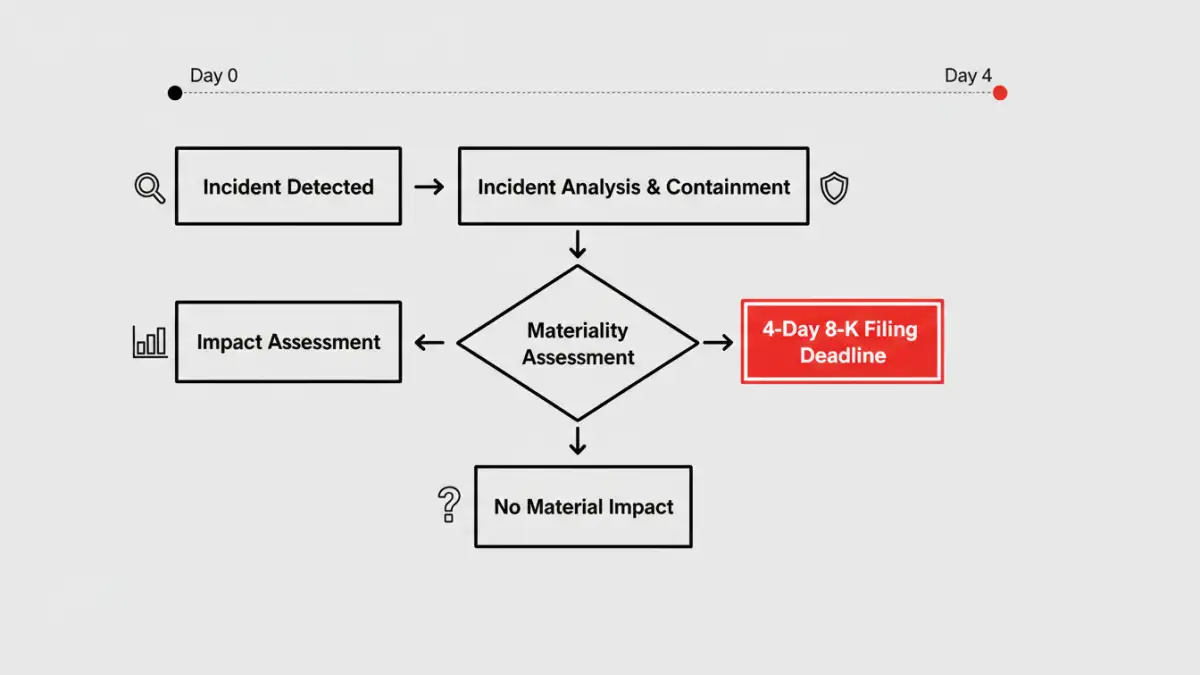
First, companies are now required to disclose any cybersecurity incident they deem “material” within four business days of that determination. This is a very tight deadline that puts immense pressure on internal security and legal teams. Second, the rules mandate detailed annual disclosures about a company's cybersecurity risk management, strategy, and governance, which must be included in their annual Form 10-K reports. This includes describing the board's oversight of cyber risks and management's role in assessing and managing them.
How These Rules Impact Financial Document Management

These new regulations directly affect how organizations handle their most sensitive information. It's no longer enough to just have security measures in place; you must be able to detect, assess, and report on breaches with incredible speed. This puts a spotlight on the entire lifecycle of financial document security.
The Four-Day Reporting Clock
The four-day reporting mandate is a game-changer. Imagine a breach occurs that compromises client investment files. Your incident response team not only has to contain the threat but also determine its materiality—a process involving legal, financial, and technical analysis—almost immediately. This requires having robust logging, monitoring, and data classification systems that can quickly identify which documents were accessed and what information they contained. Without this, meeting the deadline is nearly impossible.
Proving Due Diligence Annually
The annual disclosure requirement forces companies to formalize and document their approach to `financial data protection`. You can't just claim to have a secure system; you must be able to describe the processes, controls, and governance structures that protect that data. This means having clear, enforceable policies for everything from access control to data retention and destruction, especially for documents containing non-public information.
Core Pillars for Compliance and Protection
To navigate these new requirements, focusing on a few core security pillars is essential. These are not just best practices anymore; they are foundational elements for compliance. Strong controls are a key component of the updated `financial document security rules` and demonstrate a commitment to protecting investor information.
Strengthening Access Controls
The principle of least privilege has never been more critical. I've seen firsthand on development teams how overly permissive access policies can turn a minor incident into a major breach. Restricting access to sensitive investment files and financial reports to only those who absolutely need it is a non-negotiable first step. This should be enforced through role-based access control (RBAC) and reviewed regularly to remove stale permissions.
Implementing Robust Investment File Encryption
Encryption is your last line of defense. If an attacker bypasses your perimeter defenses, strong encryption can render the stolen data useless. All sensitive financial documents should be encrypted both at rest (while stored on servers or drives) and in transit (while moving across the network). This is a standard expectation not just for `sec cybersecurity` but also for frameworks like `FINRA compliance`.
A Software Engineer's Take on Implementation
From a technical standpoint, compliance requires a shift towards proactive and automated security. As engineers, we need to build systems that support this new reality. This means instrumenting our applications with detailed, structured logging that can be fed into a Security Information and Event Management (SIEM) system. These systems can then use automated rules to alert the security team to suspicious activity in real-time.
Another key area is data classification. We should build tools that automatically tag documents with sensitivity levels based on their content. This allows security systems to prioritize alerts and helps the incident response team quickly assess the scope of a breach. Integrating security checks directly into the software development lifecycle (DevSecOps) also ensures that new applications handling financial data are designed with these compliance requirements in mind from day one.
Key Compliance Areas for the New SEC Rules
| Requirement | Impact on Document Security | Recommended Action |
|---|---|---|
| Material Incident Reporting (4 Days) | Requires rapid identification of compromised documents and data. | Implement automated data breach detection and classification tools. |
| Annual Risk Management Disclosure | Demands documented policies for data handling and protection. | Develop and enforce a formal data governance and investment file encryption policy. |
| Board Oversight Disclosure | Proves that security is a top-level strategic concern. | Create regular security briefings and dashboards for executive leadership. |
| Management's Role Disclosure | Requires clear lines of responsibility for cybersecurity. | Establish a formal cybersecurity steering committee with defined roles. |