
The shift from the California Consumer Privacy Act (CCPA) to the California Privacy Rights Act (CPRA) wasn't just a minor update; it fundamentally changed the conversation around data security. For engineering teams, it moved the goalposts from simply managing data access requests to proactively architecting systems with privacy at their core. We're no longer just gatekeepers; we're now required to be security architects from day one.
This change means re-evaluating everything from how we store customer files to the access controls we put in place. It's about building systems that are not only functional but also resilient and compliant by design. The focus has sharpened intensely on what constitutes "reasonable security," a term that now carries significant legal and financial weight.
Table of Contents
From CCPA to CPRA: What's Changed for Data Security?
While CCPA laid the groundwork for consumer privacy rights in California, the CPRA update introduced more stringent requirements and created the California Privacy Protection Agency (CPPA) to enforce them. This isn't just more bureaucracy; it's a clear signal that compliance will be actively monitored and enforced. The focus has expanded beyond just data breaches to the entire lifecycle of customer data.
One of the biggest changes I've seen impact our development cycles is the introduction of concepts like "sensitive personal information" (SPI). This new category includes data like geolocation, race, and health information, which demands a higher level of protection. We now have to segregate this data and apply stricter access controls, which often means refactoring databases and APIs that were built under the more general CCPA framework.
The Rise of 'Reasonable Security'
CPRA explicitly requires businesses to implement and maintain reasonable security procedures and practices. While CCPA implied this, CPRA makes it a direct mandate. What's 'reasonable' depends on the nature of the data you hold. For a system holding millions of SPI records, 'reasonable' might mean multi-factor authentication, end-to-end encryption, and regular penetration testing. For a small marketing site, it might be simpler, but the principle remains the same: security must match the risk.
Key CPRA Requirements for Secure File Management

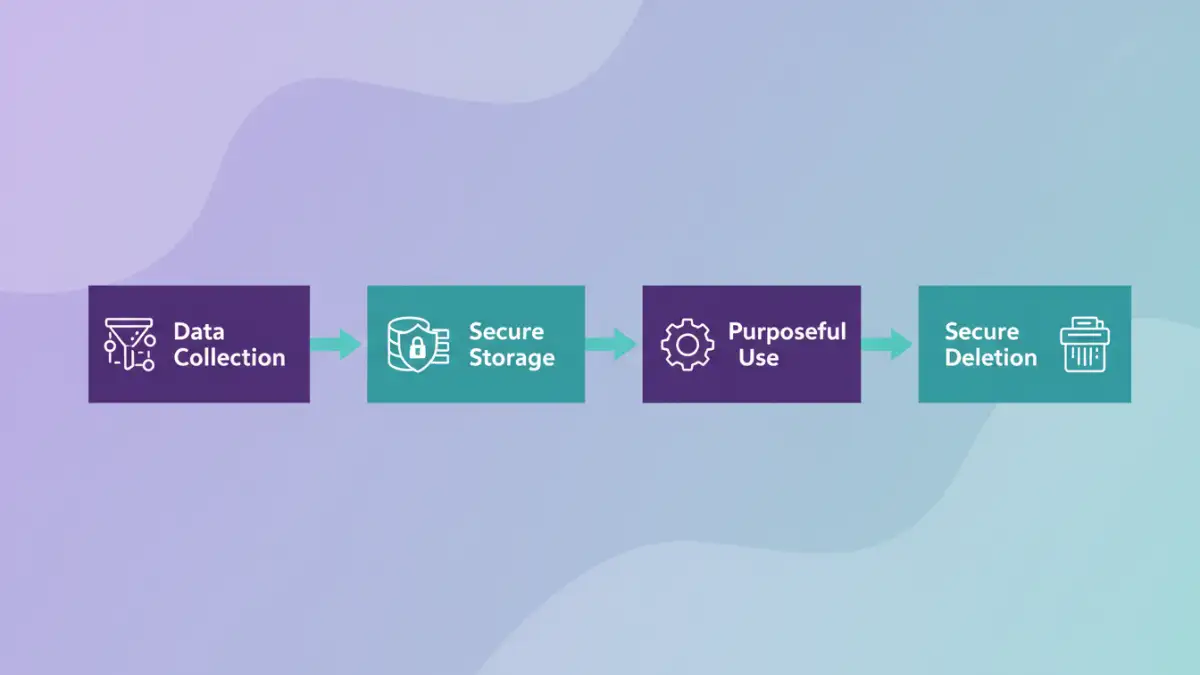
To comply with CPRA, you can't just bolt on security features at the end. You need to embed privacy principles directly into your file management and data storage architecture. This involves several core tenets that guide how we build and maintain systems.
Data Minimization and Purpose Limitation
A core principle of CPRA is data minimization—collecting only the personal information that is reasonably necessary for the disclosed purpose. As engineers, this forces us to ask critical questions before adding a new field to a database: Do we really need this data? For how long? This principle of purpose limitation means we can't repurpose data collected for one reason (like order fulfillment) for another (like marketing) without explicit consent. This has major implications for how we design data schemas and ETL pipelines.
For instance, I worked on a project where we had to build a separate, isolated data store for sensitive user documents. We implemented strict TTL (time-to-live) policies that automatically purged files after their business purpose was fulfilled, ensuring we didn't hold onto data longer than necessary. This automated approach is a key part of effective CPRA secure file management.
Implementing Technical Safeguards for CPRA Compliance
Translating legal requirements into code and infrastructure is where the real work begins. CPRA compliance is built on a foundation of strong technical controls that protect data at every stage.
Encryption and Access Control
Encryption is non-negotiable. CPRA considers the breach of unencrypted personal information a direct trigger for private right of action. This means data must be encrypted both at rest (in databases and file systems) and in transit (over networks using TLS). For our team, this meant enforcing AES-256 encryption for all S3 buckets and ensuring all internal API communication was over HTTPS.
Equally important is role-based access control (RBAC). Not everyone in the company needs access to raw customer data. We implement granular permissions, ensuring that a customer support agent can only see the data relevant to their job, while an engineer debugging a system has limited, temporary access that is logged and audited. This principle of least privilege is fundamental to customer data security.
Auditing and Maintaining Your Data Systems
CPRA isn't a one-time project; it's an ongoing commitment. Regular audits and risk assessments are now a mandatory part of the operational lifecycle. These audits help identify potential vulnerabilities in your file storage, access controls, and data deletion processes.
We've implemented automated logging for any access to sensitive data stores. Every time a file is accessed, modified, or deleted, a log is generated that includes who performed the action, when, and from where. These logs are fed into a security information and event management (SIEM) system that can alert us to suspicious activity in real-time. This continuous monitoring is crucial for demonstrating due diligence and quickly responding to potential incidents.
CPRA Security Requirements vs. Technical Implementations
| CPRA Requirement | Technical Implementation Example | Primary Goal |
|---|---|---|
| Reasonable Security Procedures | End-to-end encryption (at rest & in transit) | Prevent unauthorized data access during a breach. |
| Data Minimization | Automated data retention/deletion policies (TTL) | Reduce the attack surface by not storing unnecessary data. |
| Purpose Limitation | Strict API scopes and segregated databases | Ensure data is only used for its intended, disclosed purpose. |
| Access Control | Role-Based Access Control (RBAC) with least privilege | Limit internal exposure and prevent unauthorized data handling. |
| Risk Assessments | Regular vulnerability scanning and penetration testing | Proactively identify and remediate security weaknesses. |
| Data Breach Response | Immutable audit logs and SIEM integration | Enable rapid detection, investigation, and reporting of incidents. |