
Have you ever noticed your company’s file sharing tools suddenly getting more complex, with new prompts about data location or access logging? It's not just developers adding features for fun. More often than not, these changes are a direct response to a powerful, unseen force: regulatory compliance. These legal frameworks are the primary architects of modern data security, dictating how we build and use encryption technologies.
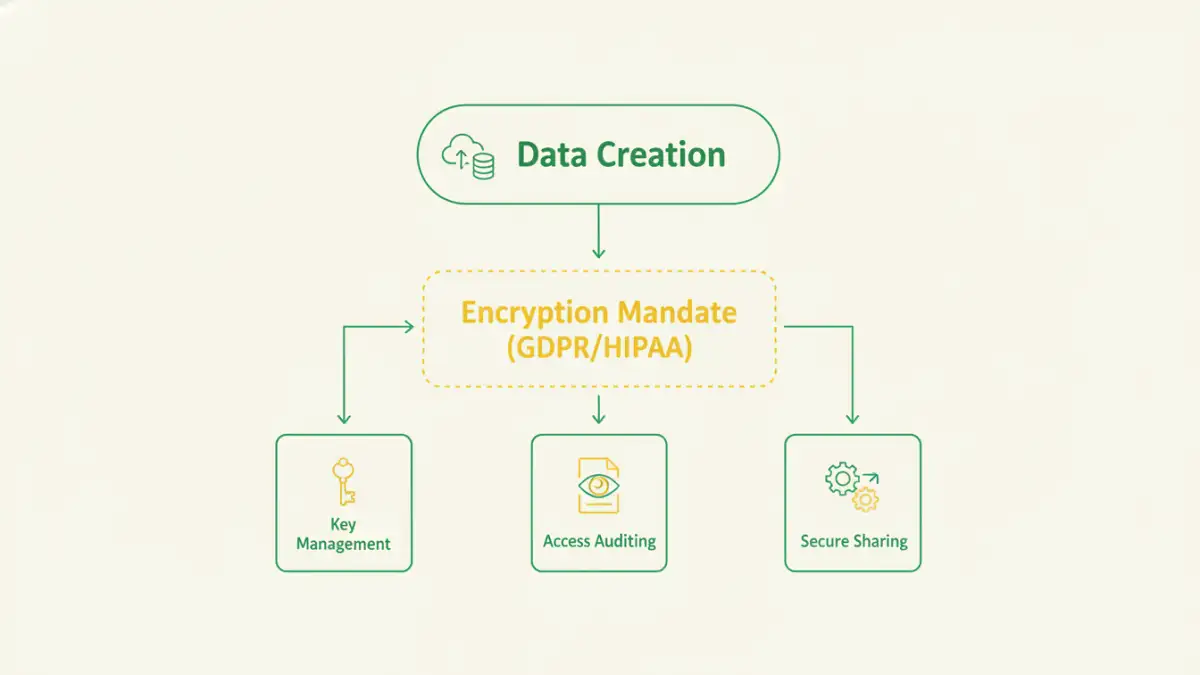
For engineers like me, compliance isn't just a checklist to satisfy a legal department; it's a set of design principles. Regulations like GDPR and HIPAA have fundamentally shifted the conversation from "Is this data encrypted?" to "Is the encryption auditable, manageable, and provably compliant?" This shift has created a feedback loop where laws shape technology, and in turn, technology enables better compliance.
Table of Contents
The Regulatory Landscape: More Than Just Acronyms
It's easy to get lost in the alphabet soup of data regulations, but each one carries specific technical demands that directly influence software development. They are the non-negotiable requirements that dictate architecture, feature sets, and even the choice of cryptographic algorithms. Ignoring them isn't just risky; it's a business-ending mistake.
GDPR and the Right to Control Data
The EU's General Data Protection Regulation (GDPR) was a watershed moment for data privacy. It solidified concepts like the "right to be forgotten" and data portability. For encryption, this means systems must not only protect data but also allow for its selective and permanent deletion. This has driven innovation in key management systems, where revoking an encryption key can render specific user data cryptographically inaccessible, effectively deleting it. This is a core component of modern gdpr document security.
HIPAA and Protected Health Information (PHI)
In the healthcare sector, the Health Insurance Portability and Accountability Act (HIPAA) has been shaping security for decades. I once worked on a telehealth platform where every single line of code handling patient data was scrutinized for compliance. HIPAA demands stringent access controls and end-to-end encryption for all PHI, both at rest (on a server) and in transit (over a network). This has made hipaa compliant file sharing a specialized field, with solutions offering detailed audit trails to prove who accessed what data, and when.
How Compliance Mandates Shape Encryption Features
Compliance requirements translate directly into the software features we use every day. What might seem like a simple user interface element often has a complex regulatory reason for its existence. The pressure to prove compliance has pushed the market beyond basic AES-256 encryption into a more holistic approach to data governance.
Advanced Key Management
It’s no longer enough to just encrypt a file. Regulations demand control over the keys. Who holds them? Can they be rotated? Can access be revoked on a per-user basis? This has led to the rise of Key Management Systems (KMS) and Hardware Security Modules (HSMs). Companies now want solutions where they can maintain control of their own keys, even when their data is stored in a third-party cloud. This is a direct result of regulations requiring data controllers to remain in control.
Granular Auditing and Logging
If a data breach occurs, the first question regulators will ask is, "Show us your access logs." Proving you took reasonable steps to protect data is crucial. Consequently, file encryption platforms have evolved to include immutable, detailed audit logs that track every file access, modification, and sharing attempt. This feature isn't just for security; it's a legal defense mechanism mandated by the regulatory environment.
The Economic and Technical Impact on the Market
The constant pressure from regulators has created enormous economic momentum. The need for compliant solutions is a primary driver behind many data privacy market trends. Companies are not just buying encryption; they are investing in compliant ecosystems. This has turned data security from a cost center into a business-critical function.
This is where a detailed file encryption market analysis becomes so insightful. It shows that growth isn't just in raw encryption tools but in integrated platforms that offer encryption, access control, auditing, and policy enforcement in a single package. The market rewards solutions that solve the compliance problem, not just the encryption problem. Startups that build their products with a "compliance-first" mindset often find a clearer path to enterprise adoption.
Navigating the Future of Compliant Encryption
The intersection of technology and regulation is constantly evolving. As engineers, we have to build for the compliance landscape of tomorrow, not just today. Two major areas are already on the horizon: post-quantum cryptography and AI-driven compliance.
The Quantum Threat
Quantum computers pose a theoretical threat to our current encryption standards. The regulatory impact on security is already being felt, as standards bodies like NIST are working to standardize quantum-resistant algorithms. In the coming years, we can expect compliance frameworks to begin recommending or even mandating the adoption of Post-Quantum Cryptography (PQC) for long-term data protection.
AI in Compliance
Artificial intelligence is also set to play a huge role. AI can be used to automatically classify sensitive data, monitor for anomalous access patterns that might indicate a breach, and even generate compliance reports. This automates the painstaking manual work often associated with proving compliance, making robust security more accessible to smaller organizations.
Regulatory Impact on Encryption Requirements
| Regulation | Key Encryption Requirement | Primary Industries Affected | Typical Penalty for Non-Compliance |
|---|---|---|---|
| GDPR | Encryption or pseudonymization of personal data; data protection by design. | Any organization processing EU resident data. | Up to 4% of annual global turnover or €20 million. |
| HIPAA | End-to-end encryption for all Protected Health Information (PHI) at rest and in transit. | Healthcare, Health Insurance, and their business associates. | Fines up to $1.5 million per year, per violation. |
| CCPA/CPRA | 'Reasonable security' to protect personal information. Encryption is a key measure. | Businesses operating in California that meet revenue or data processing thresholds. | Fines up to $7,500 per intentional violation. |
| PCI DSS | Strong encryption for cardholder data in transit and at rest. | Retail, E-commerce, Financial Services. | Fines, suspension of credit card processing privileges. |
| SOX | Secure storage and access controls for financial records to ensure data integrity. | Publicly traded companies. | Large fines and potential criminal charges for executives. |