
A few years ago, I was on a team helping a fast-growing SaaS company expand into Europe. Everything was going smoothly until our legal team flagged a major issue: our cloud architecture, which stored all user data in US-based servers, was about to violate the GDPR. Suddenly, a technical decision made for performance and cost-efficiency became a massive legal and engineering roadblock. This experience was a crash course in the complex world where data encryption meets national laws.
It's a common scenario. We, as engineers, focus on building secure, encrypted systems, but we often overlook the physical location where that encrypted data resides. This is the core of data sovereignty, a concept that can make or break a global product launch.
Table of Contents
What Are Data Sovereignty and Data Localization?
At first glance, these terms might sound like they belong in a lawyer's office, not a developer's stand-up meeting. But understanding them is crucial for anyone building systems that handle user data. They directly influence architecture, cloud provider selection, and even the features you can offer.
Key Definitions
Data Sovereignty is the principle that data is subject to the laws and legal jurisdiction of the country in which it is collected or processed. If you collect data from a German citizen, German and EU law applies, regardless of where your servers are.
Data Localization, also known as data residency, is a more direct requirement. It's a law that mandates data about a country's citizens or residents be stored within the borders of that country. Russia's On Personal Data Law is a strict example of this.
Why These Laws Matter for Encryption
A common misconception I've encountered is that encryption is a get-out-of-jail-free card for data sovereignty. While strong cloud file encryption is essential for protecting data in transit and at rest, it doesn't make the data's location irrelevant. The encrypted data is still subject to the laws of the nation where the server is located. Authorities can still legally compel a provider to hand over encrypted data, leaving the owner to deal with decryption requests.
Major Global Data Regulations to Watch

The regulatory landscape is a patchwork of different rules, but a few key regulations set the tone for global data governance. Ignoring them isn't an option, as fines for non-compliance can be astronomical.
The GDPR in Europe
The General Data Protection Regulation (GDPR) is the most well-known. It doesn't strictly mandate data localization for all data, but it places severe restrictions on cross-border data transfer to countries without an 'adequacy decision' from the EU. This means you can't just move EU citizen data to any server in the world; you must prove the destination country offers equivalent data protection standards. This is a primary driver for companies setting up EU-specific data centers.
Beyond the GDPR: A Global Snapshot
Many countries have followed the EU's lead. Brazil has the LGPD, Canada has PIPEDA, and California has the CCPA/CPRA. Other nations, like China and Vietnam, have even stricter data localization laws. Each regulation has its own nuances, making a one-size-fits-all approach to global document security nearly impossible. You have to design systems with regulatory flexibility in mind from day one.
The Impact on Encrypted File Sharing Strategies
These legal frameworks create significant technical challenges. Your strategy for secure, encrypted file sharing must be built on a foundation of compliance, which affects everything from your choice of cloud provider to your application logic.
Challenges in Cross-Border Data Transfer
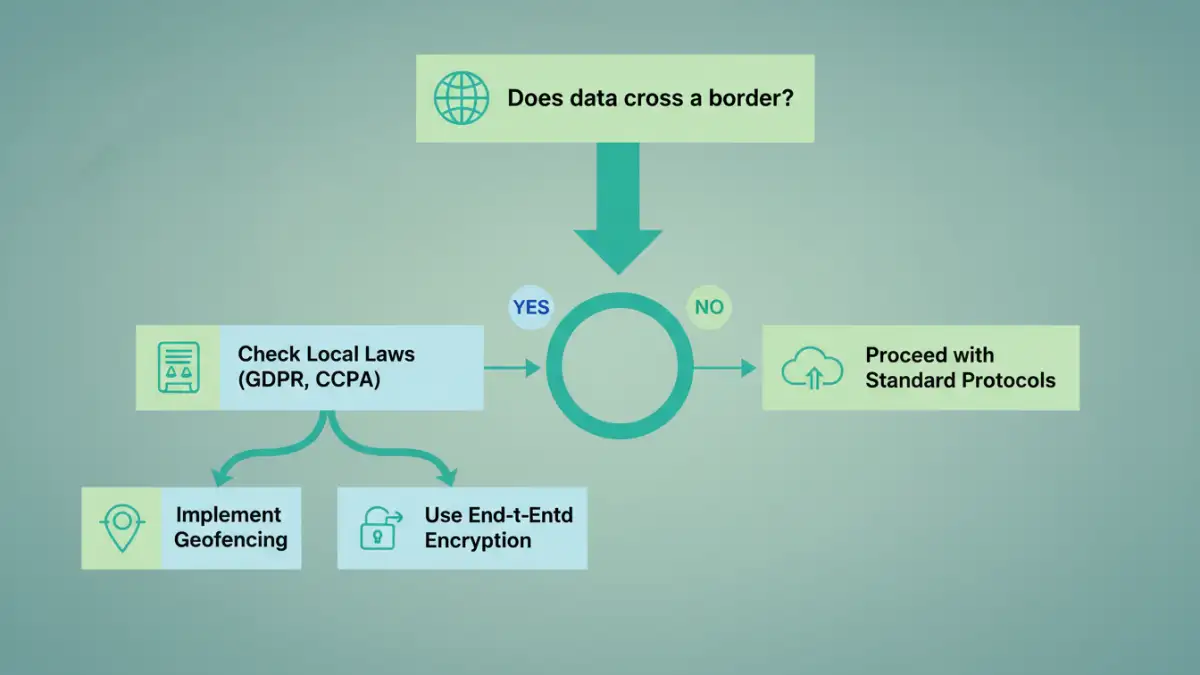
The primary challenge is managing a compliant cross-border data transfer. How do you allow a user in France to share an encrypted file with a colleague in the United States without violating GDPR? The answer often involves a multi-region cloud architecture. You might use geofencing to ensure the data of European users stays within EU data centers, or you might implement different data-handling policies based on the user's location. This adds complexity and cost to your infrastructure.
Choosing Compliant Cloud Services
When selecting a cloud provider like AWS, Azure, or Google Cloud, their global footprint becomes a critical feature. It's no longer just about latency. I now look for providers that offer specific data residency guarantees. Can I easily configure my storage buckets or databases to exist only within a specific legal jurisdiction (e.g., `eu-central-1` in Frankfurt)? Does the provider offer tools to manage data access policies on a geographical basis? These are no longer nice-to-haves; they are essential for compliance.
Best Practices for Compliant Global Document Security
Navigating the complex web of encrypted file sharing laws requires a proactive and strategic approach. It's about building compliance into your system's DNA, not bolting it on as an afterthought. Start by mapping where your users are and what data you collect. This data map will inform your entire strategy.
Implement a geo-routing or geo-sharding architecture. This means directing users to infrastructure located within their legal jurisdiction. This is the most robust way to comply with strict data localization laws. Also, maintain control over your encryption keys. Using a 'Bring Your Own Key' (BYOK) model with your cloud provider ensures that even if they are compelled to hand over data, they cannot decrypt it without your consent. Finally, document everything. Having a clear record of your data handling policies, transfer mechanisms, and security measures is your best defense during a compliance audit.
Comparison of Key Data Sovereignty Regulations
| Regulation | Geographic Scope | Key Requirement | Impact on File Sharing |
|---|---|---|---|
| GDPR | European Union | Restricts data transfer outside the EU unless 'adequacy' is proven. | Requires EU-based data storage or use of approved transfer mechanisms like SCCs. |
| CCPA/CPRA | California, USA | Focuses on consumer rights (access, deletion) rather than localization. | Less impact on data location, more on user data management and transparency. |
| LGPD | Brazil | Similar to GDPR, restricts international data transfers. | Requires explicit consent and a legal basis for transferring data out of Brazil. |
| PIPEDA | Canada | Data can be transferred but the originating company remains liable for its protection. | Organizations must ensure third-party processors abroad have comparable protection. |
| On Personal Data Law | Russia | Strict data localization; data of Russian citizens must be stored on servers in Russia. | Mandates a physical data center presence within Russia for serving Russian users. |