
A few years ago, helping a small defense contractor navigate their security requirements felt like deciphering an ancient text. The rules were complex, the costs were high, and the path to compliance was anything but clear. With the introduction of the Cybersecurity Maturity Model Certification (CMMC) 2.0, the Department of Defense (DoD) has streamlined the process, but the core mission remains: protecting sensitive government information.
This shift directly impacts how every organization in the Defense Industrial Base (DIB) handles its data. It's no longer just about firewalls and antivirus software; it's about the very policies that govern how you create, store, and share documents containing sensitive information. Getting this right is fundamental to achieving and maintaining compliance.
Table of Contents
What is CMMC and Why Did it Change?
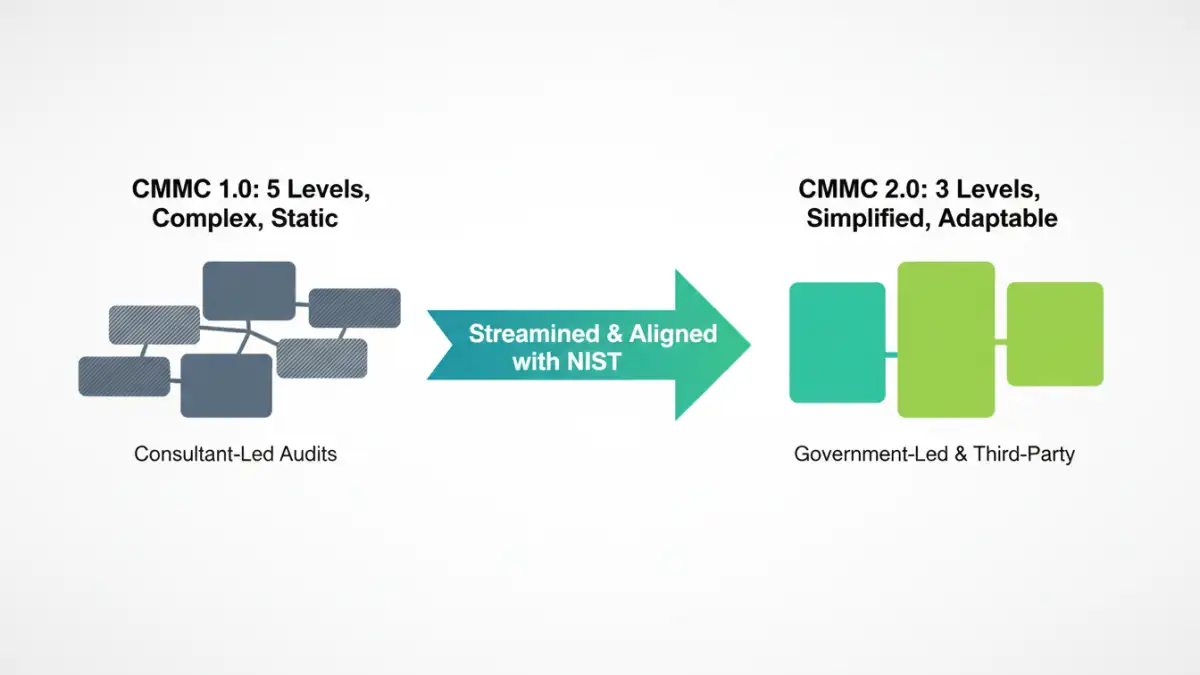
CMMC is a framework designed to protect Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) within the supply chain of the Department of Defense. The initial version, CMMC 1.0, was a five-level model that many found to be overly complex and expensive, especially for small businesses.
In response to industry feedback, the DoD introduced CMMC 2.0. This updated framework simplifies the model down to three levels, aligns more closely with existing NIST standards, and reduces the assessment burden for many contractors. The goal is to make robust cybersecurity more achievable without compromising national security.
From CMMC 1.0 to 2.0: The Key Shifts
The transition from 1.0 to 2.0 eliminated two of the original five levels, making the progression more logical. It also removed CMMC-unique practices and maturity processes, instead grounding the requirements directly in well-established standards from the National Institute of Standards and Technology (NIST). This alignment makes it easier for companies already following NIST guidelines to adapt.
The Three Levels of CMMC 2.0 Explained

Understanding the new three-tiered model is the first step toward compliance. Each level corresponds to the type of information a contractor handles and requires a different set of security controls and assessment types.
Level 1: Foundational
This entry-level tier is for companies that only handle Federal Contract Information (FCI). It requires demonstrating basic cyber hygiene through 17 security practices outlined in FAR 52.204-21. For Level 1, organizations can perform an annual self-assessment, which significantly lowers the barrier to entry for smaller contractors.
Level 2: Advanced
Level 2 is the most significant tier, as it applies to any organization that stores, processes, or transmits Controlled Unclassified Information (CUI). The requirements here are fully aligned with NIST SP 800-171, which includes 110 security controls. Depending on the criticality of the CUI involved, companies will either need to conduct a self-assessment or undergo a formal third-party assessment every three years.
Level 3: Expert
Reserved for companies handling the most sensitive CUI, Level 3 builds upon the controls of Level 2. It incorporates a subset of controls from NIST SP 800-172 to protect against Advanced Persistent Threats (APTs). This level will require a triennial government-led assessment, signifying the highest level of scrutiny.
Direct Impacts on Your Document Security Policy
CMMC 2.0 isn't just an IT checklist; it forces a fundamental review of your internal processes. A robust **document security policy CMMC** alignment requires you to move beyond simply having policies and into actively implementing and enforcing them. Your policies must now explicitly define how your organization handles sensitive information at every stage of its lifecycle.
This means your document security policy must clearly address access control (who can view, edit, or share CUI?), data labeling (how is CUI identified?), encryption (is data encrypted at rest and in transit?), and incident response (what happens if CUI is compromised?). Vague policies are no longer sufficient; they must be detailed, actionable, and auditable.
The Central Role of CUI
The concept of Controlled Unclassified Information is central to CMMC. CUI is information that requires safeguarding but is not classified. Your policy must have a clear procedure for identifying and marking documents containing CUI. I've seen teams struggle with this; a common mistake is either over-classifying everything or, more dangerously, failing to identify CUI at all. Proper training and clear guidelines are essential.
Practical Steps for CMMC 2.0 Alignment
Aligning your policies with CMMC 2.0 can seem daunting, but it can be broken down into manageable steps. The focus should be on creating a sustainable security culture, not just passing an audit.
1. Identify and Classify Your Data
You can't protect what you don't know you have. The first step is to conduct a thorough data discovery audit to identify all FCI and CUI within your systems. This includes file servers, cloud storage, email, and even physical documents. Once identified, this data must be properly classified and labeled according to your policy.
2. Implement Access Controls and Encryption
Once you know where your CUI is, you must control who can access it. This involves implementing the principle of least privilege, ensuring employees only have access to the data necessary for their jobs. Strong multi-factor authentication (MFA) is a must. Furthermore, you must ensure appropriate **file encryption standards** are applied to CUI both when it's stored (at rest) and when it's being transmitted (in transit).
3. Document Everything and Train Your Team
Your policies, procedures, and system security plan (SSP) must be meticulously documented. This documentation is what assessors will review. More importantly, your team needs to be trained on these policies. A policy is useless if no one knows it exists or how to follow it. Regular security awareness training is a key requirement for achieving **CMMC compliance**.
CMMC 2.0 Level Requirements at a Glance
| Level | Focus | Required Practices | Assessment Type |
|---|---|---|---|
| Level 1 (Foundational) | Protecting Federal Contract Information (FCI) | 17 Practices (from NIST 800-171) | Annual Self-Assessment |
| Level 2 (Advanced) | Protecting Controlled Unclassified Information (CUI) | 110 Practices (aligned with NIST 800-171) | Triennial Third-Party or Self-Assessment |
| Level 3 (Expert) | Protecting CUI from Advanced Persistent Threats (APTs) | 110+ Practices (from NIST 800-171 & 800-172) | Triennial Government-Led Assessment |