
A company's early days of document security often look like organized chaos. An important contract gets a password in Word, a sensitive HR file is thrown into a password-protected ZIP archive, and that's about it. This works for a team of five, but it completely breaks down at fifty, let alone five thousand. I've seen projects stall because a key employee left and no one could access their encrypted files—a clear failure of process, not technology.
Moving from this ad-hoc approach to a cohesive strategy is one of the most critical steps a growing business can take. It’s about building a framework that protects information systematically, ensuring that security scales along with the company, rather than becoming a bottleneck.
Table of Contents
The Problem with Ad-Hoc Security at Scale
The manual, one-off approach to document encryption is brittle. It relies entirely on individual employees remembering to encrypt files, using strong passwords, and somehow securely sharing those passwords. As an organization grows, this method fails spectacularly. You end up with forgotten passwords, inconsistent security levels, and no way to audit who has access to what.
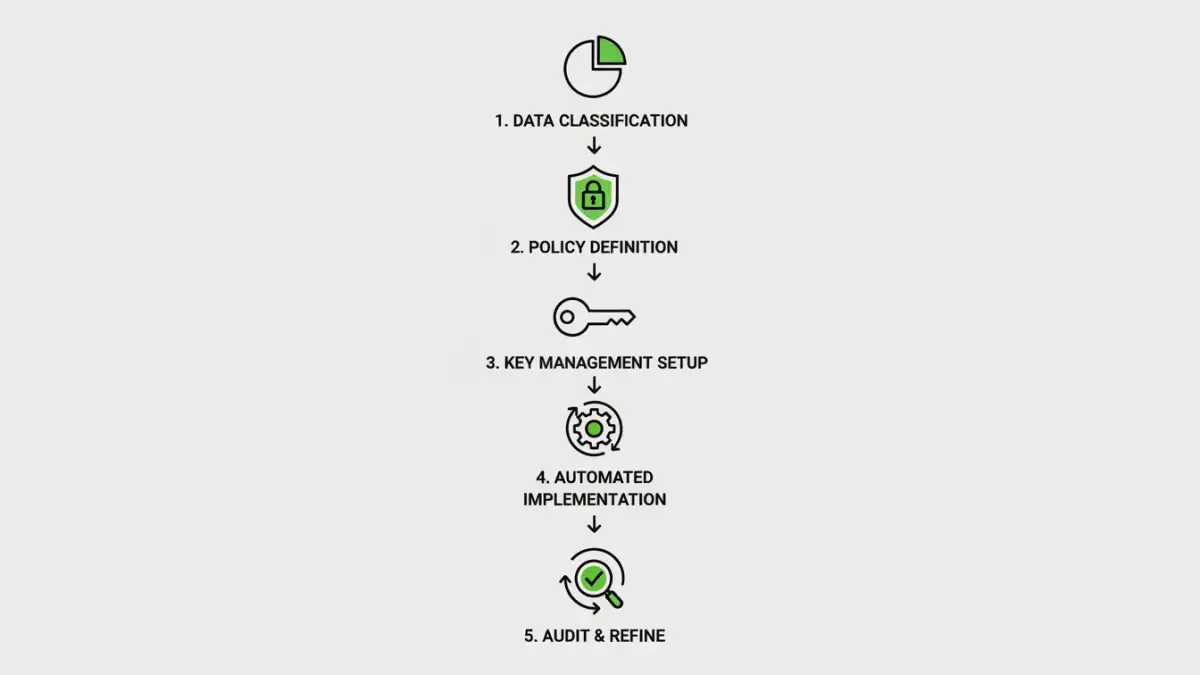
A structured approach is essential. It starts not with technology, but with a clear plan. This is where you establish a foundational corporate encryption policy that dictates what gets encrypted, how, and by whom. Without this blueprint, any technology you deploy is just a temporary fix.
Defining Your Corporate Encryption Policy
Your policy is the rulebook for data security. It should be straightforward and answer fundamental questions. What data is considered sensitive (e.g., PII, financial data, intellectual property)? What is the minimum encryption standard required (e.g., AES-256)? How will encryption keys be managed? Who is authorized to decrypt certain classes of data? Answering these questions creates the foundation for a truly effective enterprise document encryption strategy.
Pillars of Scalable Data Protection

To build a system that lasts, you need to focus on a few core principles. These pillars transform encryption from a manual task into an automated, manageable, and auditable process that supports the business instead of hindering it.
Centralized Key Management
If your data is a locked treasure chest, the encryption key is the only way to open it. Losing the key means losing the data forever. In an enterprise setting, relying on individuals to manage their own keys is a recipe for disaster. A centralized Key Management System (KMS) or a Hardware Security Module (HSM) is non-negotiable. These systems securely generate, store, and rotate encryption keys, providing strict access controls and an audit trail for every key operation.
Automation and System Integration
The only way to ensure consistent application of your policy is through automation. Manually encrypting thousands of documents is impossible. Instead, encryption should be integrated directly into your workflows. For example, you can use APIs to automatically encrypt files upon upload to cloud storage like S3 or SharePoint. This approach to scalable data protection ensures that security is applied by default, removing the burden from employees and eliminating human error.
Implementing Bulk File Encryption Across Repositories
One of the biggest hurdles is dealing with the massive volume of existing files stored on servers, in the cloud, or on employee devices. This is where a bulk file encryption strategy comes into play. It involves systematically discovering, classifying, and encrypting these legacy files according to your new policy.
This process must be carefully planned to avoid disrupting business operations. You might run discovery tools first to identify sensitive data, then schedule the encryption process during off-peak hours. The goal is to bring all historical data into compliance without causing downtime. This is also crucial for achieving multi format file security, as your tools must handle everything from PDFs and Office documents to images and proprietary file types.
Choosing the Right Tools and Platforms
The final piece of the puzzle is selecting the technology to enforce your policy and automate the work. You don't have to build everything from scratch. The market offers a range of solutions designed for this exact purpose.
Data Loss Prevention (DLP) systems are excellent for this. They can scan data in motion, at rest, and in use, automatically identifying sensitive information and applying encryption or other protective actions. Cloud Access Security Brokers (CASBs) offer similar capabilities specifically for cloud applications, sitting between your users and cloud services to enforce security policies. Evaluating these platforms based on their ability to support your specific corporate encryption policy is a critical step in operationalizing your security strategy.
Encryption Scaling Strategy Comparison
| Approach | Key Features | Complexity | Best For |
|---|---|---|---|
| Manual Per-File Encryption | User-driven, built-in to apps (e.g., Word, Adobe) | Low | Small teams or individual use cases with no central oversight. |
| Automated Scripting | Custom scripts (e.g., PowerShell, Python) to scan and encrypt files. | Medium | Organizations with strong technical teams to manage legacy data on file servers. |
| Data Loss Prevention (DLP) Platforms | Content-aware discovery, classification, and automatic encryption. | High | Mature organizations needing to protect data across endpoints, networks, and cloud. |
| Cloud-Native Services (e.g., AWS KMS) | Integrated key management and encryption for cloud storage. | Medium-High | Businesses heavily invested in a specific cloud ecosystem (AWS, Azure, GCP). |