
When dealing with a collection of sensitive documents, the question of how to protect them becomes paramount. Whether it's legal contracts, financial reports, personal records, or proprietary business information, ensuring that only authorized individuals can access these files is crucial. This is where robust encryption comes into play, transforming readable data into an unreadable format that requires a specific key or password to decipher.
My experience has shown that the 'one-size-fits-all' approach rarely works for document security. Different types of documents, varying levels of sensitivity, and diverse access needs all contribute to the complexity of making the right document portfolio encryption choice. Understanding the landscape of available encryption methods and tools is the first step toward building a secure digital fortress for your valuable information.
Table of Contents
Understanding Encryption Basics
At its core, encryption is a process of encoding information so that only authorized parties can access it. It involves using algorithms to scramble data, making it unintelligible to anyone without the correct decryption key. This protects your documents from unauthorized viewing, modification, or theft, especially when they are stored, transmitted, or shared.
Why Encrypt Document Portfolios?
A document portfolio often contains a series of related files that, when viewed together, can reveal a significant amount of sensitive information. Encrypting the entire portfolio, or individual critical documents within it, ensures that a breach of one file doesn't necessarily compromise the entire collection. This layered security is vital for maintaining confidentiality and integrity.
Key Encryption Methods Explained

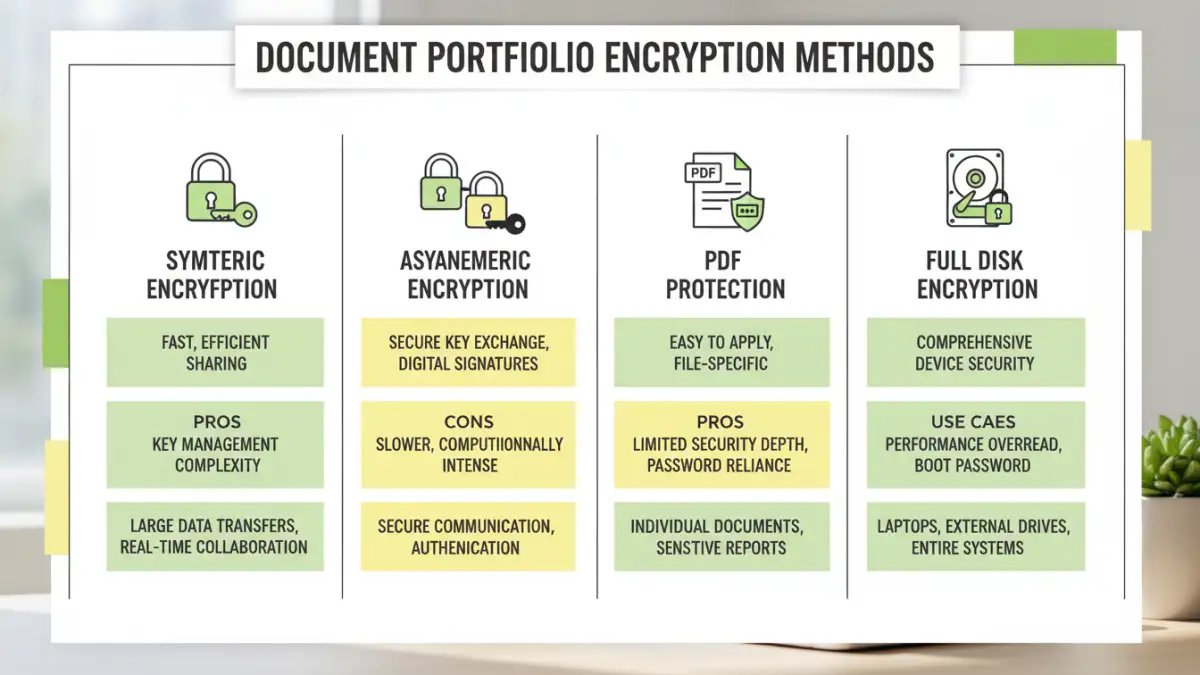
Several encryption methods are commonly used, each with its strengths and weaknesses. The choice often depends on the type of data, the desired security level, and compatibility requirements.
Symmetric Encryption
This method uses a single, secret key for both encryption and decryption. It's generally faster than asymmetric encryption, making it ideal for large volumes of data. AES (Advanced Encryption Standard) is a widely adopted and highly secure symmetric encryption algorithm.
Asymmetric Encryption
Also known as public-key cryptography, this method uses a pair of keys: a public key for encryption and a private key for decryption. While slower, it's crucial for secure communication and digital signatures, as it allows data to be encrypted by anyone with the public key but only decrypted by the intended recipient with their private key.
Selecting the Right Software
The implementation of encryption often relies on specialized software. From built-in operating system features to dedicated third-party applications, the options are diverse. The right pdf encryption software can simplify the process and offer additional features.
Built-in OS Features
Many operating systems offer basic encryption capabilities. For example, FileVault on macOS and BitLocker on Windows can encrypt entire drives, providing a foundational layer of security for all files stored on them. These are convenient for full-disk protection.
Third-Party Encryption Tools
Dedicated encryption software often provides more granular control, allowing you to encrypt specific files or folders. Tools like VeraCrypt offer robust file and volume encryption, while others focus on specific file types, like password-protecting PDFs with varying levels of access control.
Best Practices for Document Portfolios
Beyond choosing an encryption method, several practices ensure your document portfolios remain secure. Strong, unique passwords or passphrases are the first line of defense. Avoid easily guessable combinations and consider using a password manager to generate and store complex credentials securely.
Regularly update your encryption software to benefit from the latest security patches and algorithm improvements. Furthermore, consider the context of sharing: if you need to share encrypted documents, ensure the recipient has the necessary software and the correct decryption key. Securely managing and distributing these keys is as important as the encryption itself.
Assessing Data Security Levels
Understanding different data security levels is crucial when making your document portfolio encryption choice. Not all encryption is created equal. AES-256, for instance, is considered a very strong standard, offering a high degree of protection against brute-force attacks.
Consider the sensitivity of the information. Highly confidential data might warrant the strongest available encryption, even if it introduces some performance overhead. For less sensitive but still important documents, a balance between security and usability might be more appropriate. Always review the encryption standards supported by any software you choose.
Comparison Table
| Encryption Method | Primary Use Case | Security Strength | Complexity | Key Management |
|---|---|---|---|---|
| Symmetric (e.g., AES) | Encrypting large files/volumes | Very High | Moderate | Single shared secret key |
| Asymmetric (e.g., RSA) | Secure communication, digital signatures | High | High | Public/Private key pair |
| Password Protection (e.g., PDF) | Securing individual documents | Variable (depends on password strength & algorithm) | Low to Moderate | Password |
| Full Disk Encryption (e.g., BitLocker, FileVault) | Protecting all data on a drive | High | Low (once set up) | System login credentials/recovery key |