
Working with sensitive documents, whether for personal projects, business dealings, or client work, requires a robust approach to security. My career has shown me that overlooking the protection of these assets can lead to significant risks, from data breaches to reputational damage. It's not just about locking a file; it's about establishing a comprehensive strategy that ensures only authorized individuals can access your information.
This involves understanding the various threats and implementing layered security measures. We'll explore practical steps you can take to enhance the security of your document portfolio, ensuring peace of mind and compliance with any necessary regulations.
Table of Contents
Understanding the Basics of Document Security
At its core, securing your portfolio means preventing unauthorized access, modification, or disclosure of your sensitive files. This encompasses a range of information, from financial records and personal identification to intellectual property and client data. Understanding the types of data you possess is the first step in determining the appropriate level of protection needed.
Types of Sensitive Data
Sensitive data can broadly be categorized into personal information (PII), financial information, intellectual property, and confidential business data. Each type may have specific legal or regulatory requirements for protection. For instance, PII often falls under data privacy laws like GDPR or CCPA, requiring stringent handling and security measures.
Practical Methods for Protection

Implementing effective security measures doesn't always require complex IT infrastructure. Many readily available tools and practices can significantly bolster your document protection. My experience highlights that a combination of methods often yields the best results, creating multiple layers of defense.
Encryption
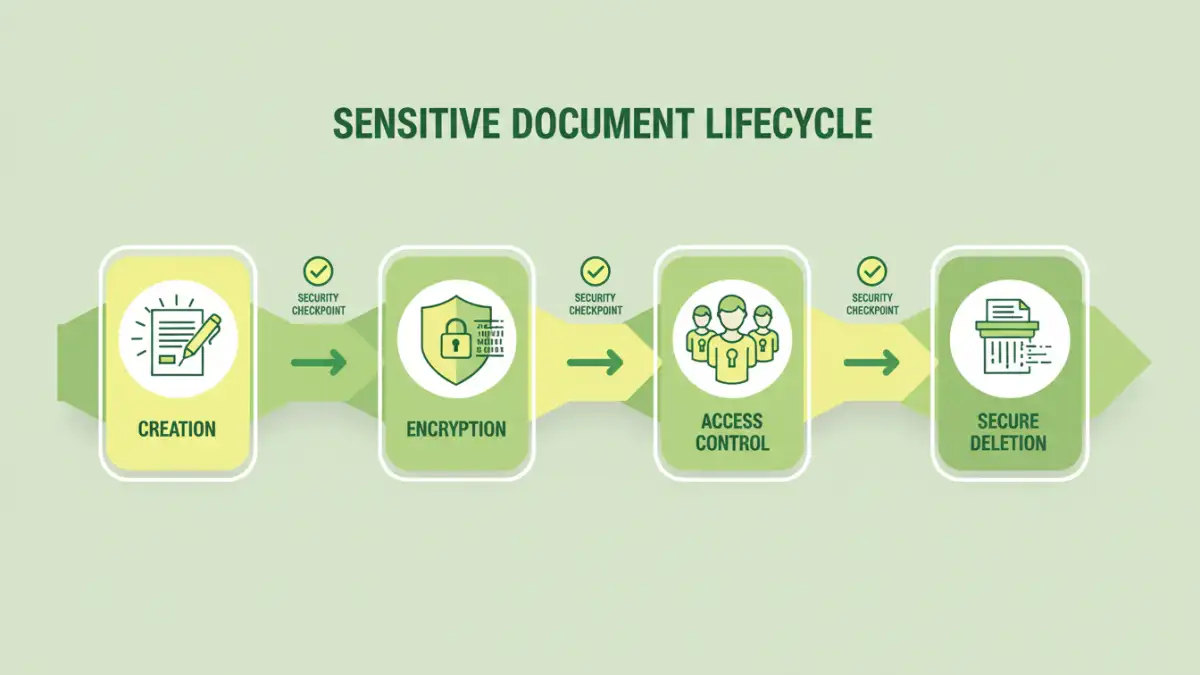
Encryption is a fundamental technique that scrambles data, making it unreadable without a specific decryption key or password. Most operating systems offer built-in encryption for entire drives or specific files. For documents, you can often encrypt them directly within applications like Microsoft Word or Adobe Acrobat, or use dedicated encryption software.
Password Protection
Applying strong, unique passwords to your documents is a straightforward yet effective barrier. Avoid simple or easily guessable passwords. For critical documents, consider using password managers to generate and store complex passwords securely. This is a cornerstone of robust confidential file management.
Advanced Security Techniques
Beyond basic password protection and encryption, several advanced techniques can further safeguard your portfolio. These methods often involve specialized software or configurations, providing more granular control over access and data integrity.
Access Control and Permissions
Implementing strict access controls ensures that only specific individuals or groups can view, edit, or delete documents. This is crucial in collaborative environments or when dealing with shared network drives. Properly configured permissions limit the attack surface and reduce the risk of accidental data exposure.
Secure Deletion
Simply deleting a file doesn't remove it from your storage device; it only marks the space as available. For highly sensitive documents, using secure deletion tools that overwrite the data multiple times is essential to prevent recovery by forensic methods. This ensures that once a document is no longer needed, it's truly gone.
Developing a Document Security Policy
A formal document security policy provides a framework for managing and protecting your sensitive documents. It outlines the rules, responsibilities, and procedures for handling confidential information throughout its lifecycle, from creation to disposal. This policy should be communicated to all relevant parties and reviewed periodically.
Key Policy Components
A comprehensive policy should cover data classification, access control procedures, encryption standards, password management guidelines, data backup and recovery plans, incident response protocols, and employee training requirements. Clearly defining these elements helps to standardize security practices and minimize human error.
Ongoing Risk Mitigation
Security is not a one-time setup; it's an ongoing process of vigilance and adaptation. Regularly reviewing your security measures, staying informed about emerging threats, and conducting periodic risk assessments are vital for effective sensitive document portfolio protection.
Regular Audits and Updates
Periodically audit your access logs, review user permissions, and test your backup and recovery systems. Ensure that all software, including operating systems and security applications, is up-to-date with the latest patches. This proactive approach helps to identify and address vulnerabilities before they can be exploited.
Comparison Table: Document Security Methods
| Method | Description | Pros | Cons | Best For |
|---|---|---|---|---|
| Password Protection | Applying passwords to individual files or archives. | Easy to implement, widely supported. | Weak passwords can be easily cracked; doesn't protect against physical access. | Basic protection for individual files. |
| File Encryption (e.g., AES-256) | Scrambling data using complex algorithms. | Very strong security; renders data unreadable without key. | Requires management of encryption keys/passwords; can impact performance. | Protecting highly sensitive data at rest. |
| Access Control Lists (ACLs) | Defining permissions for users/groups on files/folders. | Granular control over who can access what; good for collaboration. | Complex to manage in large environments; relies on proper user authentication. | Multi-user environments and shared resources. |
| Secure Deletion Tools | Overwriting file data to prevent recovery. | Ensures data is irrecoverable after deletion. | Can take time; not always necessary for all data. | Disposing of sensitive data from storage media. |