
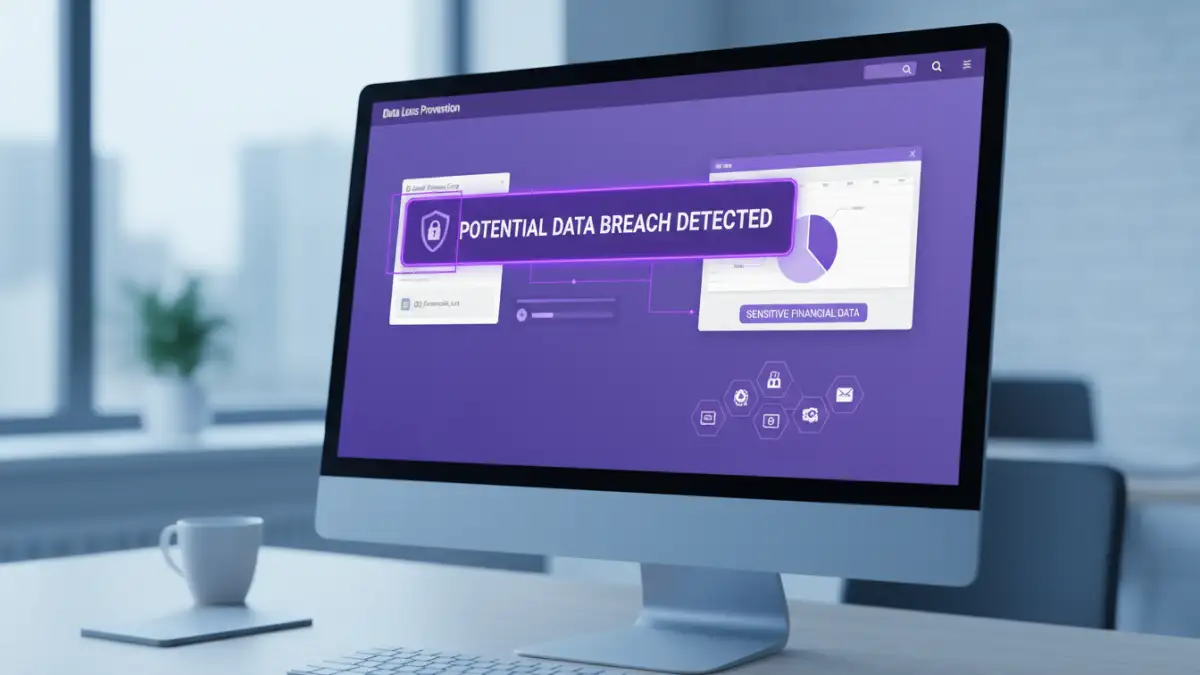
It's a scenario I see play out far too often in the industry: a company invests heavily in network firewalls and endpoint protection, only to be compromised by something as simple as a misconfigured shared folder. A recent survey confirms this quiet threat, revealing that unsecured documents are one of the leading causes of data breaches today. This isn't about sophisticated zero-day exploits; it's about the everyday files we create, share, and store.
The findings are a stark reminder that our digital perimeter is no longer just the network edge. It extends to every single file containing sensitive information, whether it's stored on a local drive, a cloud service, or a shared server. Understanding this vulnerability is the first step toward building a more resilient defense.
Table of Contents
The Alarming Reality: What the Latest Survey Reveals
The latest document data breach survey paints a clear picture: organizations are struggling with data sprawl. The report, which analyzed thousands of security incidents, found that nearly 40% of breaches involved internal files that were improperly secured. These weren't necessarily targeted by advanced persistent threats but were often exposed through simple negligence or a lack of awareness.
These file security statistics show a trend away from complex network intrusions toward opportunistic attacks targeting easily accessible data. Attackers know that finding an unprotected database backup, a publicly shared folder of contracts, or a collection of employee records is often easier than breaching a well-maintained firewall. The core issue is a fundamental gap in unsecured documents security practices that leaves sensitive information exposed.
Why Unsecured Documents Are Such Low-Hanging Fruit
The reasons behind this trend are rooted in both human behavior and technical oversight. In a fast-paced work environment, convenience often trumps security. This leads to common information leak causes that are surprisingly simple to exploit yet incredibly damaging.
Human Error and Misconfiguration
From my experience debugging cloud infrastructure, human error is the most persistent variable. An employee might share a sensitive file with a public link for a client, forgetting to revoke access later. I've seen entire development projects, including API keys and credentials, exposed because a developer set a cloud storage bucket to 'public' for a quick test and never changed it back. These small mistakes create massive, persistent vulnerabilities.
Lack of Encryption and Access Controls
Many documents are created and stored without any form of encryption or access control. A simple password on a ZIP archive or enabling built-in document encryption can be a powerful deterrent. However, many users either don't know these features exist or find them too cumbersome. This lack of basic security hygiene means that if an attacker gains access to a file server or cloud account, the data is freely available for the taking.
Vulnerabilities Across Common Document Types
The risk isn't limited to one type of file. From spreadsheets containing financial projections to presentations with strategic plans, every document can be a liability if not properly secured. Even seemingly benign files can contain hidden metadata that reveals sensitive information about your organization's infrastructure or personnel.
A recent PDF vulnerability report highlighted how even this common format can be exploited. While PDFs support robust encryption, many are left completely unprotected. Furthermore, vulnerabilities in PDF reader software can be used to execute malicious code, making an unsecured document a potential entry point for a wider attack on a system.
Building a Practical Defense Strategy for Your Files
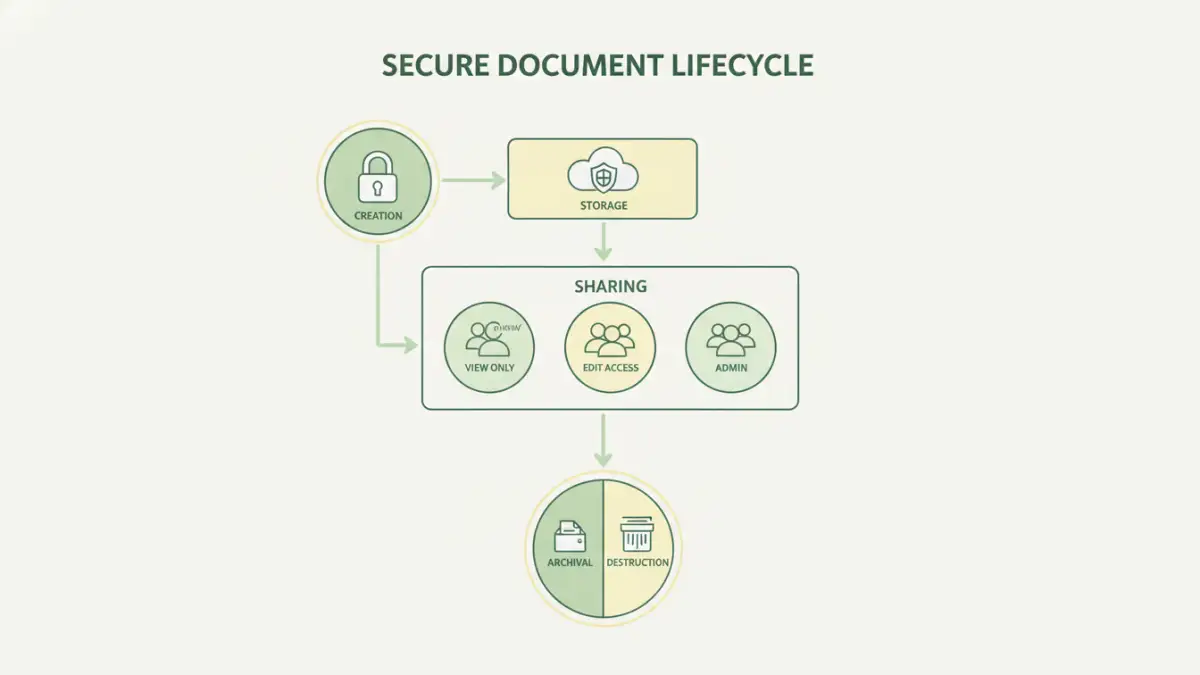
Addressing the challenge of unsecured documents requires a multi-layered approach that combines policy, technology, and user education. It's about shifting from a reactive mindset to a proactive one where data is protected by default throughout its entire lifecycle.
Implementing a 'Secure by Default' Policy
Organizations should establish clear policies for data handling. This means classifying data based on sensitivity and defining minimum security requirements for each class. For example, any document containing Personally Identifiable Information (PII) must be encrypted at rest and in transit. This removes the guesswork for employees and makes security a standard part of the workflow, not an afterthought.
Leveraging Encryption and Access Management
Modern tools make file-level security easier than ever. Utilize the built-in encryption features in Microsoft Office and Google Workspace. For more robust control, implement Data Loss Prevention (DLP) solutions that can automatically scan for and encrypt sensitive information in documents. Furthermore, enforcing the principle of least privilege ensures that users only have access to the files they absolutely need to perform their jobs, drastically reducing the attack surface.
Document Security Measures Comparison
| Security Measure | Primary Function | Pros | Cons |
|---|---|---|---|
| File-Level Encryption | Makes file content unreadable without a key. | Protects data even if stolen; granular control. | Can lead to key management complexity; may impact performance. |
| Access Control Lists (ACLs) | Defines who can read, write, or execute a file. | Simple to implement on file systems; effective for internal threats. | Doesn't protect data if the file is moved or copied off the system. |
| Data Loss Prevention (DLP) | Monitors and blocks unauthorized data exfiltration. | Automates policy enforcement; provides visibility into data flows. | Can be expensive; may generate false positives. |
| Digital Rights Management (DRM) | Controls usage rights (e.g., printing, copying). | Persistent protection that travels with the document. | Can be restrictive for legitimate users; requires specific software. |