
The way we handle information has fundamentally shifted, with digital documents forming the backbone of nearly every operation. From sensitive client contracts to proprietary research, securing these files is no longer just good practice; it's a critical necessity. As cyber threats continue to evolve, staying ahead of the curve requires a keen understanding of current digital document security trends.
In my years of software engineering, I've seen firsthand how quickly security landscapes change. What was robust protection yesterday might be a vulnerability tomorrow. This pace necessitates a proactive approach, especially when it comes to safeguarding the digital assets that drive businesses and individuals alike. Understanding these shifts is key to maintaining trust and operational integrity.
Table of Contents
Emerging Threats and Challenges
The digital threat landscape is constantly expanding. We're seeing a rise in sophisticated phishing attacks specifically targeting document repositories and collaborative platforms. Ransomware continues to be a significant concern, with attackers increasingly focusing on encrypting critical business documents and demanding hefty sums for their release. Furthermore, insider threats, whether malicious or accidental, remain a persistent challenge in maintaining robust document management security.
Sophisticated Phishing and Social Engineering
Attackers are becoming more adept at crafting convincing lures that trick users into revealing credentials or downloading malicious files disguised as legitimate documents. These attacks often exploit trust within organizations, making them particularly difficult to detect. Vigilance and comprehensive user training are more important than ever.
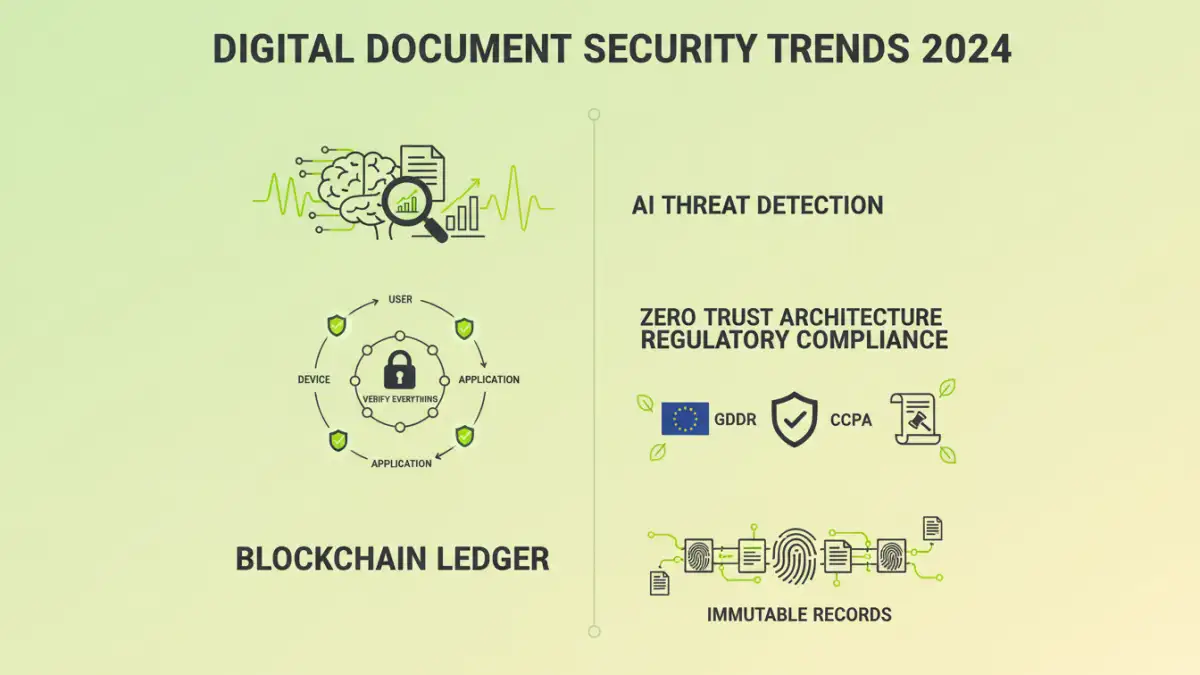
AI and Machine Learning in Security

Artificial intelligence (AI) and machine learning (ML) are no longer just buzzwords; they are becoming integral tools in the fight for electronic document protection. AI-powered security solutions can analyze vast amounts of data to detect anomalies and patterns indicative of a security breach much faster than human analysts.
Proactive Threat Detection
ML algorithms can learn normal user behavior and flag deviations, helping to identify compromised accounts or insider threats before significant damage occurs. This proactive approach significantly enhances the overall security posture, moving beyond reactive measures to predictive defense mechanisms.
The Rise of Zero Trust Architecture
The traditional perimeter-based security model is becoming obsolete. The concept of 'Zero Trust' assumes that no user or device, inside or outside the network, can be implicitly trusted. Every access request must be verified rigorously.
Micro-segmentation and Least Privilege
Implementing Zero Trust involves principles like micro-segmentation, breaking down networks into smaller, isolated zones, and enforcing the principle of least privilege, granting users only the access necessary for their roles. This dramatically reduces the attack surface and limits the lateral movement of threats if a breach does occur.
Enhanced Data Privacy Regulations
Governments worldwide are enacting stricter data privacy laws, such as GDPR and CCPA, which directly impact how organizations must handle and protect digital documents. Compliance is not optional, and the penalties for violations can be severe.
Consent Management and Data Minimization
Organizations are increasingly focused on transparent consent management for data collection and processing, alongside the principle of data minimization, collecting only what is absolutely necessary. This regulatory pressure is driving better practices in document lifecycle management and security.
Blockchain for Document Integrity
While not mainstream for everyday document security, blockchain technology is finding niche applications in ensuring document integrity. Its decentralized and immutable ledger system can be used to create tamper-proof records of document creation, modification, and access.
Verifiable Audit Trails
This provides an unalterable audit trail, which is invaluable for legal, financial, and regulatory compliance. It offers a high degree of assurance that a document has not been altered since its inception or last verified on the blockchain.
Future Outlook and Preparation
The trends in digital document security point towards a more integrated, intelligent, and privacy-focused future. Organizations must adapt by investing in advanced security tools, fostering a security-aware culture, and staying informed about emerging threats and best practices. Continuous assessment and adaptation are key to maintaining effective digital document security.
Comparison Table: Document Security Approaches
| Approach | Key Features | Pros | Cons | Ideal Use Case |
|---|---|---|---|---|
| Standard Encryption | AES-256, TLS/SSL | Widely adopted, strong protection | Requires key management, can impact performance | General data in transit and at rest |
| Access Control Policies | RBAC, ABAC | Granular permissions, limits unauthorized access | Complex to manage, relies on correct configuration | Collaborative environments, sensitive data |
| Data Loss Prevention (DLP) | Content inspection, monitoring | Prevents sensitive data exfiltration | Can be resource-intensive, false positives possible | Compliance-heavy industries, PII protection |
| Zero Trust Network Access (ZTNA) | Continuous verification, least privilege | Reduces attack surface, enhances remote security | Requires significant infrastructure changes | Modern, distributed workforces |
| Blockchain Verification | Immutable ledger, cryptographic hashing | Tamper-proof integrity, verifiable audit trails | Scalability issues, limited adoption for general documents | High-value documents, legal records |