
Navigating the digital landscape requires a robust approach to protecting sensitive information. Whether you're an individual handling personal documents or a business managing proprietary data, understanding and implementing effective file security measures is paramount. In my years working with software systems, I've seen firsthand how critical a well-defined strategy for secure file handling can be, preventing costly breaches and maintaining trust.
This report delves into the core principles and practical applications of file security best practices, offering a comprehensive data security guide for various needs.
Table of Contents
Understanding the Fundamentals
At its core, file security is about preventing unauthorized access, modification, or deletion of digital files. This involves a layered approach, combining technical controls with user awareness and established protocols. Without a solid foundation, even the most advanced tools can fall short.
Key Concepts
Essential concepts include confidentiality (ensuring data is accessible only to authorized individuals), integrity (guaranteeing data hasn't been altered without authorization), and availability (making sure authorized users can access data when needed). These principles guide all decisions in developing a comprehensive data security guide.
Access Control and Permissions

One of the most immediate ways to secure files is by controlling who can access them. This involves setting granular permissions based on roles and responsibilities within an organization. Limiting access to only those who require it significantly reduces the attack surface.
Role-Based Access Control (RBAC)
RBAC is a common strategy where access rights are granted based on a user's role within a company. For instance, an HR manager might need access to employee files, while a marketing associate would not. Implementing RBAC requires careful planning of roles and their associated permissions.
Encryption Strategies
Encryption is a cornerstone of modern file security. It transforms readable data into an unreadable format, requiring a specific key to decrypt. This ensures that even if files are intercepted or stolen, they remain unintelligible to unauthorized parties.
At-Rest vs. In-Transit Encryption
Encryption can be applied to files stored on devices (at-rest) or those being transferred over networks (in-transit). Both are vital. For instance, encrypting a hard drive protects data if the physical device is lost, while encrypting data sent via email prevents eavesdropping.
Secure File Handling Procedures
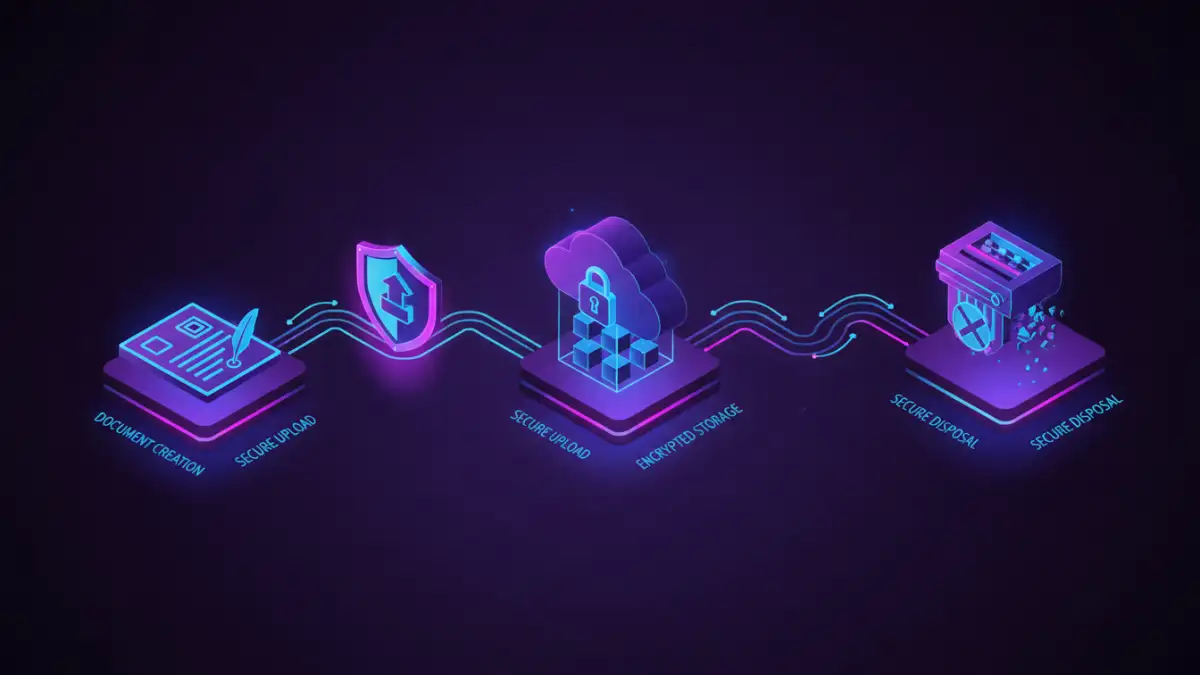
Beyond technical controls, establishing clear procedures for how files are created, stored, shared, and disposed of is critical. This forms the backbone of secure file handling in any environment.
Data Classification and Labeling
Not all files are created equal. Classifying data based on its sensitivity (e.g., public, internal, confidential, restricted) allows for the application of appropriate security measures. Labeling files clearly helps users understand the level of protection required.
Secure Sharing Practices
Sharing files externally or even internally needs careful consideration. Using secure, encrypted channels, setting expiration dates for shared links, and verifying recipient identities are crucial steps to prevent accidental exposure.
Monitoring and Auditing
Regularly monitoring file access and system activity is essential for detecting potential security incidents. Audit trails provide a record of who accessed what files, when, and from where, which is invaluable for investigations and compliance.
Activity Logging
Enabling comprehensive logging for file access, modifications, and permission changes is a fundamental aspect of security. These logs should be stored securely and reviewed periodically for anomalies or suspicious patterns.
Overall Best Practices
Consistently applying a set of proven methods ensures a strong security posture. These practices are not just about technology but also about human behavior and organizational policies.
Regular Backups
Having reliable, regularly updated backups stored in a separate, secure location is a critical safeguard against data loss due to hardware failure, cyberattacks, or accidental deletion. Testing these backups periodically confirms their integrity and recoverability.
Employee Training
Human error remains a significant vulnerability. Educating employees about phishing attempts, social engineering tactics, and the importance of adhering to security policies empowers them to be the first line of defense.
Comparison Table
| Security Measure | Description | Effectiveness | Implementation Effort |
|---|---|---|---|
| Password Protection | Securing files with unique passwords. | Moderate (weak passwords are a risk) | Low |
| File Encryption (At-Rest) | Scrambling data stored on devices. | High (with strong algorithms) | Moderate |
| Access Control Lists (ACLs) | Defining specific user permissions. | High (when properly configured) | Moderate to High |
| Secure File Transfer Protocol (SFTP) | Encrypted method for file transfer. | High | Moderate |
| Data Loss Prevention (DLP) Tools | Software to monitor and prevent data leaks. | High | High |
Extra tips before you try to file security best practices
First, confirm what kind of protection you are dealing with. Some PDFs require a password to open (user password), while others only restrict printing/copying/editing (owner password). The safest approach depends on which one you have.
For sensitive documents, prefer offline tools and avoid uploading confidential files to unknown websites. If you must use an online tool, read the privacy policy and delete uploaded files immediately after processing.
- Try a different PDF viewer (some apps cache old permissions)
- Re-download the file (corruption can cause false password errors)
- Check caps lock / keyboard layout for password entry
- Differentiate “permission password” vs “open password” prompts
- If it is not your file, request access from the owner