
Public sector agencies handle a staggering volume of sensitive information, from citizen data to classified national security documents. Unlike in the private sector, the rules for managing these records are often dictated by strict legal mandates for transparency and long-term preservation. This creates a unique set of challenges that off-the-shelf storage solutions simply can't address.
The core issue isn't just about storing files; it's about creating a system that guarantees authenticity, integrity, and accessibility for decades, or even permanently, while defending against constant cyber threats. It requires a fundamental shift from simple file storage to a robust, compliant, and auditable archival system.
Table of Contents
The Unique Challenges of Public Sector Archiving
Working with government clients on data systems, I've seen firsthand that their requirements are fundamentally different. The concept of 'deleting' data is often replaced with complex retention schedules mandated by law. This environment is defined by compliance, scale, and the extreme sensitivity of the information involved.
Navigating Compliance and Retention Schedules
Public records management is governed by a web of regulations. In the U.S., this includes the Freedom of Information Act (FOIA), which mandates public access to certain records, and standards set by the National Archives and Records Administration (NARA). Each document type can have a different retention period, ranging from a few years to permanent preservation.
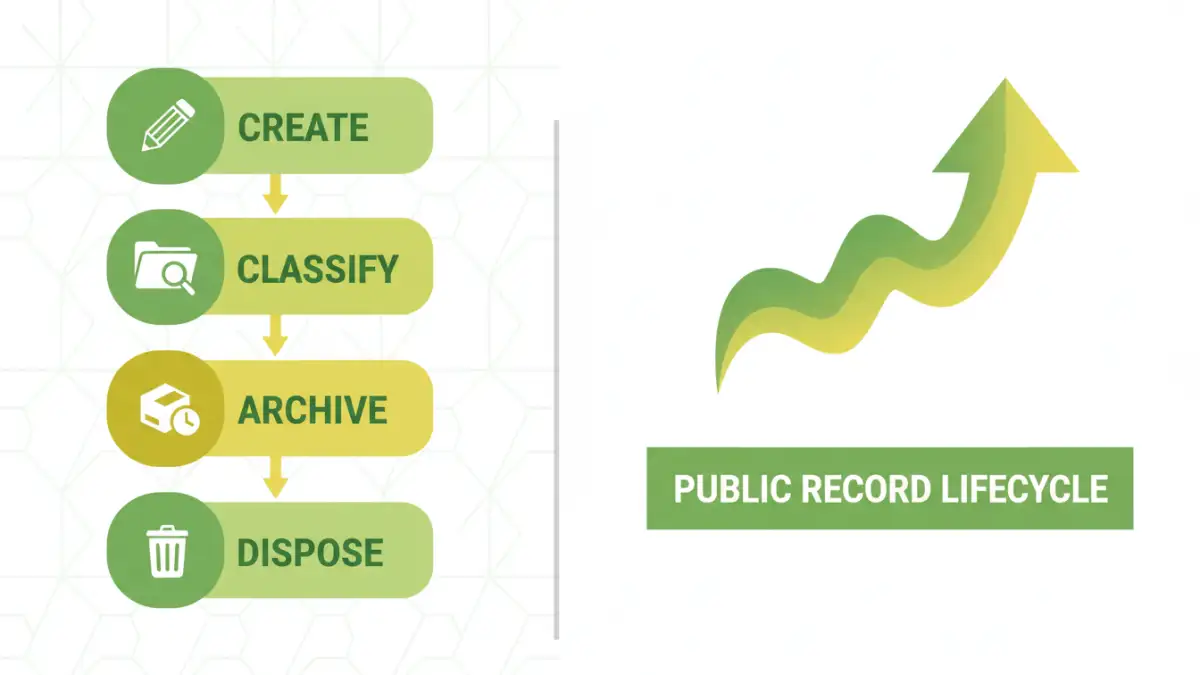
A failure to produce a specific record upon request can have serious legal consequences. Therefore, an archiving system must not only store the data but also manage its entire lifecycle according to these complex, non-negotiable schedules. This involves tracking, classifying, and applying retention rules automatically to prevent accidental deletion or unauthorized modification.
The Scale and Sensitivity Problem
Government agencies generate immense quantities of data daily. This includes everything from mundane administrative paperwork to highly sensitive personal identifiable information (PII), healthcare records (PHI), and classified intelligence. The sheer volume makes manual management impossible and introduces significant risk.
The sensitivity of this data makes it a high-value target for cyberattacks. A breach can compromise citizen privacy, disrupt government operations, and erode public trust. Consequently, security cannot be an afterthought; it must be the foundational principle of any digital archiving solution.
Core Pillars of a Secure Archiving System

A truly effective system for secure document archiving is built on several non-negotiable pillars. These components work together to ensure data is protected from creation to its eventual, legally-sanctioned disposition.
Granular Access Control and Audit Trails
Not everyone in an agency should have access to every file. Role-Based Access Control (RBAC) is essential. It ensures that users can only view or modify records pertinent to their specific job functions. For instance, a clerk in the records department should not have access to sensitive law enforcement files.
Equally important is the audit trail. Every single action performed on a record—viewing, editing, exporting, deleting—must be logged immutably. This log should record who performed the action, what they did, and when. In the event of a data breach or a legal challenge, this audit trail is an indispensable forensic tool.
Encryption: At-Rest and In-Transit
Encryption is the bedrock of digital archiving security. Data must be protected at two key stages. Encryption 'in-transit' protects data as it moves across networks, such as when a file is being uploaded to the archive. This prevents eavesdropping or man-in-the-middle attacks.
Encryption 'at-rest' protects the data while it is stored on servers or other media. This ensures that even if an unauthorized party gains physical access to the storage hardware, the files themselves remain unreadable without the proper cryptographic keys. For public sector data, using strong, federally-approved encryption standards like AES-256 is a minimum requirement.
Implementing a Robust Archiving Strategy
Developing a strategy goes beyond buying software. It involves a holistic approach to how records are classified, stored, and managed throughout their lifecycle. Automation is key to reducing human error and ensuring consistent policy application.
Choosing the Right Storage Medium
The choice between cloud, on-premise, or a hybrid model for long term data storage has significant implications. On-premise solutions offer maximum control but come with high capital and maintenance costs. Cloud solutions, particularly those with government-specific environments (like AWS GovCloud or Azure Government), offer scalability and reduced overhead but require careful vetting to ensure compliance.
A hybrid approach often provides the best of both worlds, allowing agencies to keep highly sensitive data on-premise while leveraging the cloud for less critical records and disaster recovery. The decision should be based on a thorough risk assessment, budget, and specific compliance needs.
Automation in Classification and Retention
Manually classifying millions of documents is a recipe for failure. Modern systems use metadata and even AI-powered tools to automatically tag and classify records as they are created. For example, a document containing a social security number can be automatically flagged as PII and have stricter access and retention policies applied.
This automation extends to retention schedules. The system can automatically flag records for disposition once their retention period has expired, creating a review workflow for a records manager to provide final approval. This ensures compliance without creating an unmanageable manual workload.
Future-Proofing Your Government File Retention
Technology evolves, and so do threats. A system implemented today must be viable for decades to come. This means choosing technologies and establishing processes that are resilient and adaptable.
WORM Storage and Immutability
For records that must remain unaltered, Write-Once-Read-Many (WORM) storage is the gold standard. This technology, available in both physical and cloud-based forms, prevents a file from being changed or deleted for a specified period. It provides a technical guarantee of record integrity, which is crucial for legal evidence and historical preservation.
Immutability ensures that once a record is written to the archive, it cannot be overwritten. This is a powerful defense against ransomware, which relies on encrypting and overwriting original files. If the original record is immutable, it can be easily restored.
Archival Storage Solutions Comparison
| Storage Model | Security Control | Scalability | Compliance Management | Best For |
|---|---|---|---|---|
| On-Premise | Highest direct control over hardware and network. | Limited by physical infrastructure and budget. | Can be tailored, but responsibility is 100% internal. | Agencies with highly classified data and existing data center resources. |
| Government Cloud | Strong, but relies on a shared responsibility model with the provider. | Virtually unlimited, pay-as-you-go model. | Providers offer compliance certifications (e.g., FedRAMP), simplifying audits. | Agencies needing flexibility, scalability, and built-in disaster recovery. |
| Hybrid | A balanced approach, keeping sensitive data on-premise. | Good; combines on-premise stability with cloud elasticity. | Complex; requires managing policies across two different environments. | Organizations transitioning to the cloud or with diverse data sensitivity levels. |