The encryption that protects our most sensitive files, from financial records to intellectual property, is built on mathematical problems that are currently impossible for classical computers to solve in a reasonable timeframe. But a new class of machine—the quantum computer—is poised to break this foundation. This isn't science fiction; it's a security challenge my colleagues and I are actively planning for today.
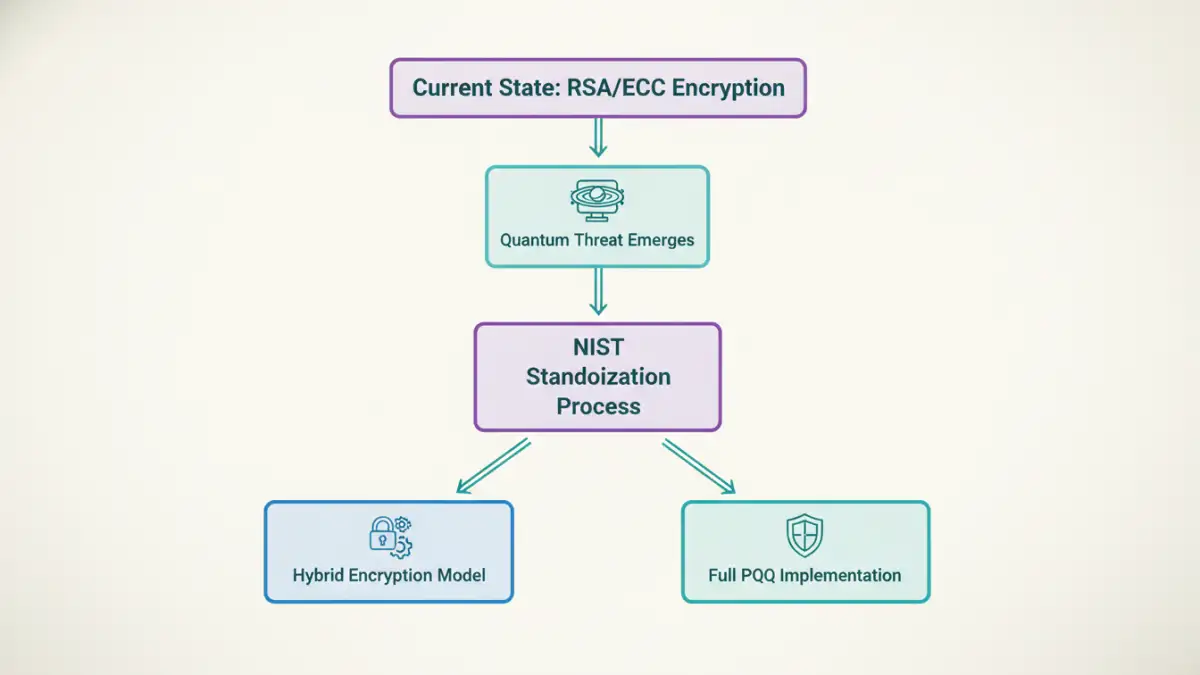
The threat is that a sufficiently powerful quantum computer could render our most trusted encryption algorithms, like RSA and ECC, obsolete. This necessitates a proactive shift toward new cryptographic methods that can withstand attacks from both classical and quantum computers. The transition won't be instant, but the preparation must start now.
Table of Contents
Understanding the Quantum Threat to Encryption
For decades, public-key cryptography has been the bedrock of digital security. It secures everything from our online banking to encrypted email. This system relies on the difficulty of certain mathematical tasks, like factoring large numbers. A classical computer would take billions of years to break a standard RSA key. A quantum computer, however, operates on entirely different principles.
Why Current Encryption is Vulnerable
Quantum computers can use algorithms like Shor's algorithm, which is specifically designed to solve the very problems our current encryption relies on. It can factor large numbers exponentially faster than any classical computer, meaning it could theoretically break a 2048-bit RSA key in a matter of hours or days. This capability effectively dismantles the security promises of our existing infrastructure.
The 'Harvest Now, Decrypt Later' Problem
One of the most immediate dangers is the "harvest now, decrypt later" attack. Adversaries can capture and store encrypted data today, even if they can't decrypt it. They are betting that in the future, once they have access to a powerful quantum computer, they can decrypt this trove of stolen information. For files with long-term sensitivity, like government secrets, trade secrets, or personal health records, this is a critical and present risk.
NIST's Role in a Quantum-Resistant Future

Recognizing this impending threat, the U.S. National Institute of Standards and Technology (NIST) initiated a process to solicit, evaluate, and standardize one or more quantum-resistant public-key cryptographic algorithms. After a multi-year competition involving cryptographers from around the world, NIST announced its first set of standardized algorithms in 2022, with formal standards published in 2024.
This NIST PQC update is a landmark event. It provides a vetted, standardized set of tools that organizations can start integrating into their systems. The initial standards focus on general encryption and digital signatures, with algorithms like CRYSTALS-Kyber for key-encapsulation and CRYSTALS-Dilithium for signatures leading the way. These new standards are based on different mathematical foundations, such as lattice-based cryptography, that are believed to be resistant to quantum attacks.
Strategies for Transitioning to PQC
Migrating an entire cryptographic infrastructure is a massive undertaking. I've been part of large-scale system migrations, and they are never as simple as flipping a switch. The key to a successful transition to quantum resistant security is a thoughtful, phased approach centered on crypto-agility.
Crypto-Agility: The Foundation of Modern Security
Crypto-agility is the ability of a security system to switch between cryptographic algorithms without requiring a complete system overhaul. In projects I've worked on, building in this flexibility from the start saved us enormous headaches down the line. Instead of hardcoding a specific algorithm (e.g., RSA-2048), the system is designed to negotiate and use different cryptographic primitives. This is essential for a smooth PQC transition, allowing systems to be updated as new standards emerge or vulnerabilities are found.
Hybrid Encryption Models
During the transition period, a hybrid approach is the most prudent strategy. This involves using both a traditional, well-understood algorithm (like RSA) and a new PQC algorithm simultaneously. For example, when encrypting a file, you would use both methods and combine the results. An attacker would then need to break both the classical and the quantum-resistant algorithm to access the data. This provides security against both current and future threats, offering a safe bridge to a fully quantum-resistant ecosystem.
Practical Steps for Future-Proofing File Security
Organizations can't afford to wait until quantum computers are a reality. The time to prepare for post quantum file encryption is now. The process starts with understanding your current cryptographic landscape and creating a strategic roadmap.
Inventory and Assess Your Crypto Usage
The first step is to create a comprehensive inventory of all cryptographic systems in use. Where are you using RSA or ECC? Which applications, systems, and files rely on them? What is the expected secure lifespan of the data being protected? Answering these questions helps prioritize which assets need to be migrated first. Assets protecting data that must remain secure for more than a decade are prime candidates for early adoption of PQC.
Develop a Migration Roadmap
Once you understand your crypto-inventory, you can develop a phased migration plan. This roadmap should identify which systems will be updated, the timeline for these updates, and the specific PQC algorithms to be implemented. Start with less critical systems to pilot the new algorithms and build expertise. Engage with software vendors to understand their PQC roadmaps and ensure your technology partners are also preparing for this shift. This proactive planning ensures a secure and orderly transition, safeguarding data for the future.
PQC Algorithm Candidate Comparison
| Algorithm Family | Primary Use Case | Key Strengths | Potential Trade-offs |
|---|---|---|---|
| Lattice-Based (e.g., Kyber, Dilithium) | General Encryption & Signatures | Strong security proofs, good performance | Larger key and signature sizes than traditional crypto |
| Code-Based (e.g., Classic McEliece) | Key Encapsulation | Long history, resistant to quantum algorithms | Very large public key sizes |
| Hash-Based (e.g., SPHINCS+) | Digital Signatures | Well-understood security (based on hash functions) | Stateful versions are complex; large signature sizes |
| Isogeny-Based (e.g., SIKE - now broken) | Key Exchange | Small key sizes | Security concerns; broken by classical attacks |