A legal team I was consulting for recently hit a wall. They had received a massive data dump as part of electronic discovery, but a significant portion of the crucial documents—spreadsheets, archives, and PDFs—were locked behind passwords. The opposing counsel claimed they didn't have the passwords, and the clock was ticking. This scenario isn't just a technical headache; it's a serious legal hurdle with major implications.
Handling encrypted files during the discovery process is where technology and law intersect, often with significant friction. It requires a clear strategy that is both technically sound and legally defensible. Failing to produce accessible data can lead to sanctions, so understanding the rules and the tools is non-negotiable.
Table of Contents
The Legal Framework for Encrypted ESI
The foundation for handling electronically stored information (ESI) in the US is the Federal Rules of Civil Procedure (FRCP). Specifically, Rule 34 governs the production of documents and ESI. The rule mandates that data must be produced in a "reasonably usable form." A password-protected file that cannot be opened is clearly not in a usable form.
When a party cannot access encrypted files, it triggers a discussion about burden and accessibility. The producing party has a duty to provide access. Simply handing over a locked file and saying "we don't have the key" is rarely an acceptable response in court. This is a critical aspect of managing password protected files litigation effectively.
Rule 26(b)(2)(B) and Inaccessible Data
This rule allows a party to argue that certain ESI is "not reasonably accessible because of undue burden or cost." A party might try to claim that finding passwords for old encrypted files falls under this exception. However, courts are often skeptical of this argument, especially if the party was responsible for creating the encryption in the first place.
The burden of proof falls on the producing party to show why the data is inaccessible. A court will then weigh whether the need for the information outweighs the burden of retrieving it. This often involves technical experts demonstrating the efforts required for forensic data recovery.
Technical Challenges and Solutions
From a technical standpoint, dealing with encrypted files involves several layers of complexity. The strength of the encryption, the type of file, and the availability of metadata all play a role in how you might approach decryption. The goal is to gain access without compromising the integrity of the original file.
Cooperative vs. Adversarial Approaches
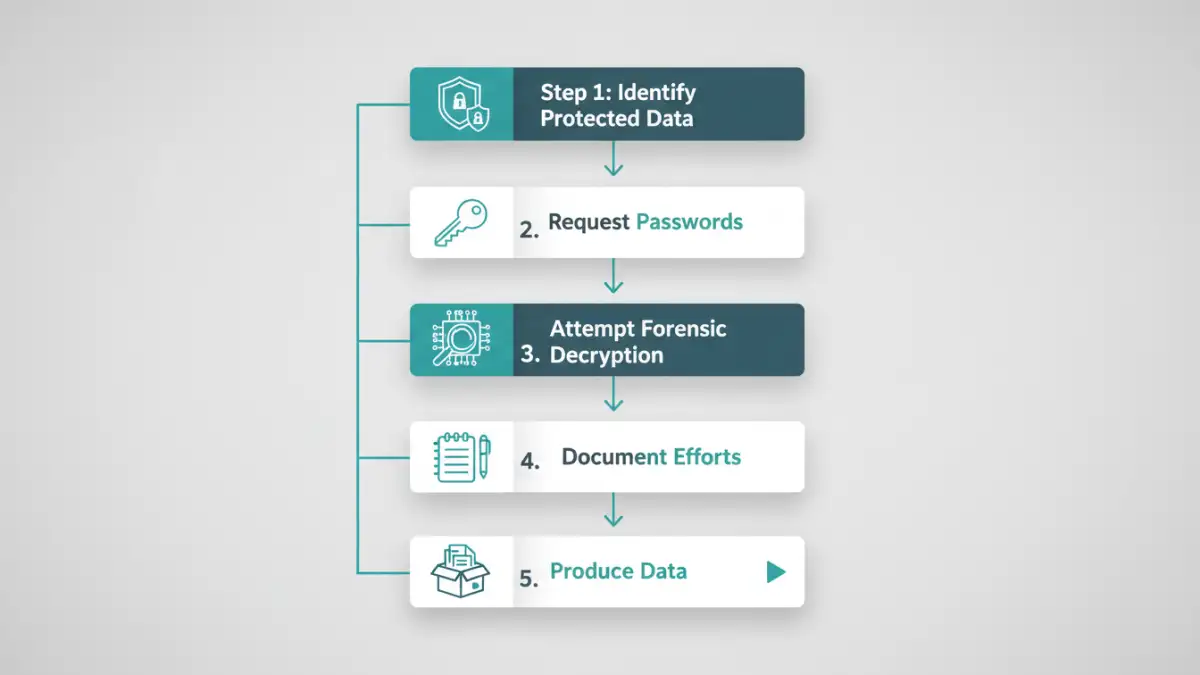
The simplest solution is cooperation. The requesting party asks for the passwords, and the producing party provides them. This is the most efficient and cost-effective method. However, in contentious cases, this cooperation may not be forthcoming. Passwords might be genuinely lost, or a party might be intentionally obstructive.
When cooperation fails, you move to more adversarial, technical solutions. This involves using specialized software and forensic techniques to recover or bypass the password. These methods must be carefully documented to prove to the court that you exhausted all reasonable efforts.
Building a Defensible Decryption Process
If you must resort to technical means for decrypting files for court, your process must be defensible. This means every action is logged, repeatable, and doesn't alter the source evidence. Haphazardly running a password cracker on a file can corrupt it or change metadata, leading to spoliation claims.
First, always work on a forensic copy of the data, never the original. This preserves the source evidence in its untouched state. Second, use reputable forensic tools that generate detailed logs of their processes. These logs become part of your evidence, showing the steps taken, the methods used (e.g., dictionary attack, brute-force), and the duration of the attempts.
Leveraging E-Discovery Platforms
Modern electronic discovery platforms are built to handle these challenges. Many have modules that can automatically identify encrypted files upon ingestion. They can then run password lists (provided by the client) against these files in a controlled environment. Some advanced platforms even integrate with forensic password recovery tools.
Using an integrated platform centralizes the effort. It provides a clear audit trail and ensures that any successfully decrypted files are immediately indexed and made available for review within the same system, maintaining the chain of custody. This structured approach is vital for legal compliance.
Proactive Strategies to Prevent Future Issues
The best way to handle encrypted files in litigation is to manage them properly before a lawsuit ever begins. Companies should have clear data governance policies that address the use of encryption. This includes maintaining a central repository or password vault for corporate-level passwords used to protect business records.
Policies should dictate when employees can and cannot apply passwords to company documents. For files that require encryption for security or regulatory reasons, the access credentials should be escrowed or managed by the IT department. This proactive management transforms a potential litigation crisis into a routine administrative task.
Comparison of Decryption Approaches in E-Discovery
| Method | Description | Legal Defensibility | Technical Complexity |
|---|---|---|---|
| Cooperative Request | Formally requesting passwords from the producing party. | High (Shows good faith effort) | Low |
| Forensic Password Recovery | Using specialized software (brute-force, dictionary attacks) to find the password. | High (If properly documented on a forensic copy) | High |
| E-Discovery Platform Processing | Using built-in platform features to decrypt files with known password lists. | Very High (Provides an audit trail) | Medium |
| Ignoring the Files | Producing locked files without attempting decryption. | Very Low (High risk of sanctions) | Low |
| Third-Party Vendor | Hiring a forensic data recovery specialist to handle decryption. | High (Relies on expert testimony and reports) | Low (for the legal team) |