
The email landed in my inbox with a subject line in all caps: URGENT. It was from our head of sales. A junior team member, trying to be efficient, had accidentally sent the final proposal for our biggest client of the year—complete with sensitive financial models and strategic plans—to an all-company distribution list. The document wasn't encrypted. It wasn't password-protected. It was just... out there.
That single click triggered a fire drill that consumed our entire week. It was a stark, painful lesson in the fragility of digital information and the importance of a proactive security posture. This became our company's defining business document security story, a costly mistake that fundamentally changed how we operate.
Table of Contents
The Incident: How One Click Caused a Crisis
It was a classic case of a high-pressure environment meeting a lack of process. The team was rushing to get the proposal finalized. The file, named `Project_Titan_Final_v12.docx`, was attached to an email meant for a small group of senior stakeholders. Instead, a typo in the address field sent it to `all-staff@ourcompany.com`.
Within minutes, the sender realized their mistake, but it was too late. The document had been delivered to hundreds of inboxes, from interns to executives in unrelated departments. The sensitive data, which was our competitive edge in the deal, was now common internal knowledge. The potential for an external leak was terrifyingly high.
The Fallout: Containing a Self-Inflicted Wound

The first hour was chaotic. Our IT team initiated a company-wide email recall, but we knew that was a flimsy defense. People had already opened it, and some might have downloaded it. Our legal and HR departments immediately began drafting communications to manage the internal situation and assess our legal exposure.
The biggest fear was the client finding out through an accidental leak. We had to proactively inform them, which was an incredibly difficult conversation. We explained the situation, the immediate steps we were taking to contain it, and how we would ensure it never happened again. Their trust in us was shaken, and the deal, which had been a near certainty, was suddenly on thin ice.
Uncovering the Root Cause: Beyond Simple Human Error
It was easy to blame the junior employee, but that would have been a mistake. The post-mortem revealed that this was a systemic failure, not an individual one. The employee was just the trigger for a disaster waiting to happen.
A Culture Without a Security Mindset
We discovered there was no formal policy for handling sensitive documents. Terms like 'Confidential' or 'Internal Use Only' were used inconsistently. There was no clear guidance on when or how to protect business documents, leaving it up to individual discretion. This lack of a clear protocol created an environment where mistakes were inevitable.
Inadequate Tools and Training
Even if an employee wanted to secure a file, they wouldn't have known how. We had no standardized tools for corporate file encryption. Some teams used the built-in password protection in Microsoft Office, while others used free online tools with questionable privacy policies. There was no training on secure file sharing or the risks associated with mishandling data. We had failed to equip our team with the knowledge and resources they needed to succeed safely.
Building a New Security Framework
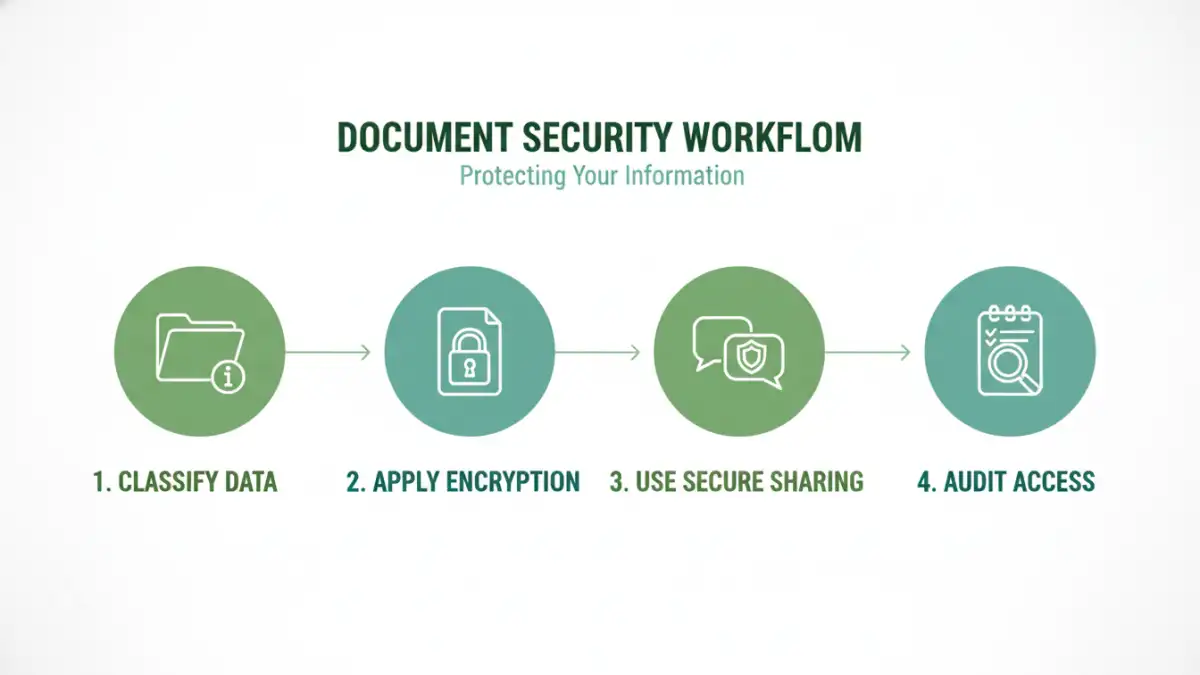
That incident was our wake-up call. We couldn't just create a few new rules; we had to build a comprehensive document security framework from the ground up to prevent data leaks for good.
Step 1: Data Classification Policy
Our first action was to create a simple, three-tiered data classification policy: Public, Internal, and Confidential. Every document created in the company now had to be classified. This simple step forced employees to think about the sensitivity of the information they were handling. 'Confidential' documents, like client proposals or financial data, were subject to the strictest controls.
Step 2: Implementing Secure Tools
We invested in a unified solution for secure file sharing and collaboration. This platform enforced our new policies automatically. Any document classified as 'Confidential' required strong encryption and could only be shared via a secure link with features like password protection, download prevention, and access expiration. This took the guesswork out of security for our employees.
Step 3: Comprehensive and Continuous Training
We rolled out a mandatory training program for all employees. It covered our new policies, how to use the new tools, and, most importantly, the 'why' behind it all. We used our own story as a powerful example of the real-world consequences of a data leak. This training is now a part of our onboarding process and is refreshed annually.
Key Lessons and Best Practices
Recovering from the incident was a long process, but we emerged a stronger, more secure company. The client, impressed by our transparency and the robust changes we made, eventually signed the deal. The experience taught us that document security isn't just an IT problem—it's a core business function.
Proactive prevention is infinitely cheaper than reactive damage control. By creating clear policies, providing the right tools, and fostering a culture of security, you empower your team to be your greatest defense, not your biggest vulnerability. Don't wait for your own crisis to take action.
Document Security Solutions Comparison
| Solution | Protection Level | Ease of Use | Best For |
|---|---|---|---|
| Basic Password Protection (e.g., Office) | Low | Easy | Protecting non-critical internal documents from casual viewing. |
| End-to-End Encrypted Messaging Apps | High (in transit) | Easy | Sharing sensitive information or files quickly with individuals. |
| Secure File Sharing Platforms | High | Moderate | Collaborating on and sharing confidential documents with external clients or partners. |
| Data Loss Prevention (DLP) Software | Very High | Complex | Large enterprises needing automated policy enforcement to prevent data exfiltration. |
| Full-Disk Encryption (e.g., BitLocker) | High (at rest) | Easy (once set up) | Protecting all data on a device if it is lost or stolen. |