
Working with sensitive information means that the method of sharing it is just as crucial as the information itself. I recently had a client, let's call her Sarah, who needed to transfer a set of confidential financial reports to a new auditor. She was understandably anxious about ensuring the files reached the right hands without any risk of interception or unauthorized access.
Sarah's concern was a common one, highlighting the ongoing need for robust security practices in our digital age. Over my years in software engineering, I've seen firsthand how a lapse in security can have significant consequences. This particular situation presented a perfect opportunity to guide Sarah through a secure and straightforward process, leading to a very positive outcome.
Table of Contents
Understanding the Need for Secure Sharing
In today's interconnected world, data breaches are a constant threat. Sharing documents, whether for business, legal, or personal reasons, requires a conscious effort to protect sensitive details. This involves not just the content of the files but also the integrity of the transfer process itself.
The risks of insecure sharing range from identity theft and financial fraud to reputational damage. Recognizing these dangers is the first step toward adopting safer practices. It's about building trust with clients and ensuring that confidentiality is maintained at every stage.
Sarah's Challenge and Goal
Sarah had accumulated several years of financial statements and tax documents that needed to be provided to a new auditor for an upcoming review. These files contained highly sensitive personal and business financial data. Her primary goal was to ensure that these documents were shared in a way that was both highly secure and easy for the auditor to access.
She was concerned about using standard email attachments due to the potential for interception. She also wanted to avoid overly complex systems that might cause delays or confusion for the auditor, who was not particularly tech-savvy. The ideal solution needed to balance strong security with user-friendliness.
Methods for Safe File Transfer
To address Sarah's needs, we explored several options tailored for secure document sharing. The key was to find a method that offered robust encryption and controlled access without being overly cumbersome. Based on her requirements, we focused on solutions that provided end-to-end encryption and clear audit trails.
Choosing the Right Tools
We evaluated a few primary approaches. The first was using a reputable cloud storage service with built-in encryption and secure sharing links. These services often allow for password protection and expiration dates on shared links, adding layers of security. Another option considered was dedicated secure file transfer platforms, which are specifically designed for this purpose and offer advanced features.
For Sarah, the cloud storage approach seemed most practical. It offered a good balance of security features and ease of use, aligning well with her auditor's technical comfort level. We selected a service known for its strong encryption standards and user-friendly interface.
The Implementation Process
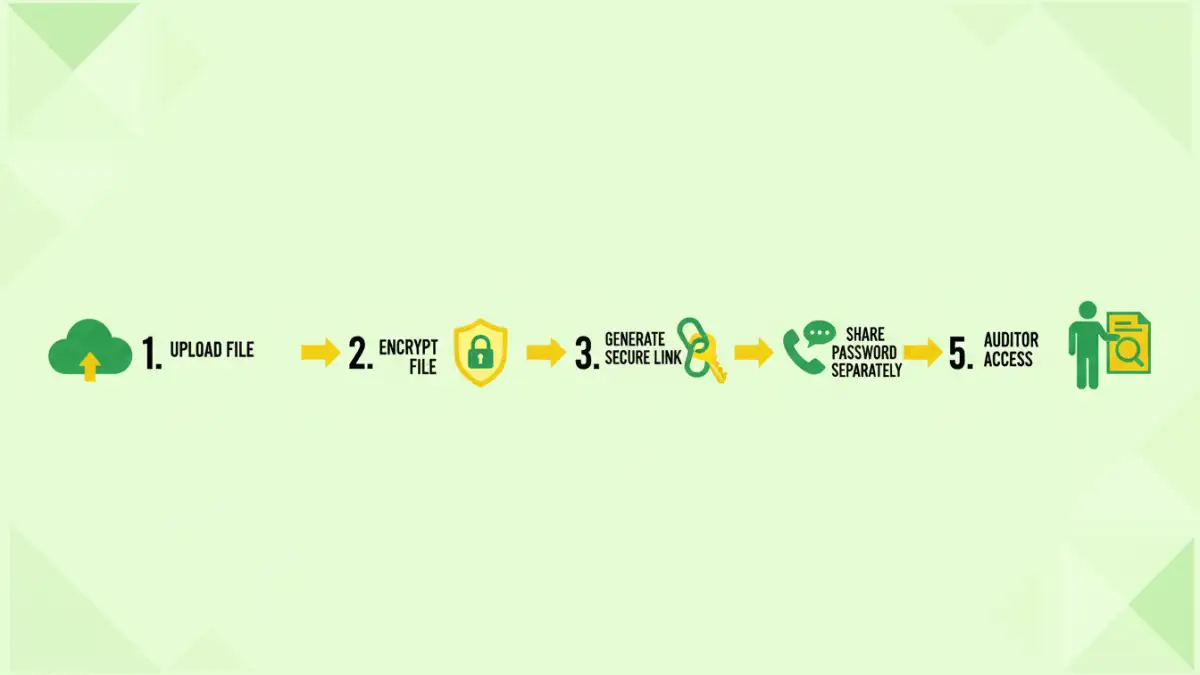
The process began with Sarah uploading the financial documents to her chosen secure cloud storage account. She ensured that the files were encrypted at rest by the service. Once uploaded, she generated a unique, encrypted sharing link for the auditor.
Crucially, Sarah added an extra layer of security by setting a password for the shared link, which she communicated to the auditor separately via a different channel (a phone call). She also configured the link to expire after 48 hours, limiting the window of opportunity for potential misuse. This multi-faceted approach ensured that even if the link were somehow compromised, the files would remain inaccessible without the password.
The Positive Outcome and Lessons Learned
The auditor was able to access the documents without any issues. They received the link, used the provided password, and successfully downloaded the financial reports. The entire process was smooth, and Sarah received confirmation that the auditor had all the necessary files securely. This client security story demonstrated the effectiveness of a well-planned approach to sharing documents safely.
Sarah was relieved and impressed by how straightforward the process was. She learned that implementing strong security doesn't have to be overly complicated. The experience reinforced the importance of understanding the tools available and configuring them correctly for optimal protection. This successful safe file transfer built confidence for future sensitive data exchanges.
Comparison of Secure Document Sharing Methods
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Secure Cloud Storage (e.g., Dropbox, Google Drive with encryption) | User-friendly, widely accessible, built-in encryption, link expiration, password protection | Potential privacy concerns depending on provider, requires account setup | General purpose file sharing, collaboration, medium to high security needs |
| Dedicated Secure File Transfer Platforms (e.g., FileCatalyst, Boxcryptor) | High-level encryption, advanced security features (e.g., audit logs, granular permissions), compliance certifications | Can be more expensive, steeper learning curve, may require software installation | Enterprise-level security, large file transfers, highly regulated industries |
| Encrypted Email Attachments (using PGP or built-in encryption) | Directly attached to email, can be end-to-end encrypted | Complex setup for sender/receiver (PGP), attachment size limits, less user-friendly | Small, highly sensitive documents for technically proficient users |
| Password Protected Archives (e.g., ZIP, RAR) | Simple to create, widely compatible, no third-party service needed | Encryption strength varies (AES-256 is best), password can be weak if not chosen carefully, requires software to open | Basic security for non-critical documents, quick sharing when password management is handled separately |