
Working with password-protected documents can be frustrating, especially when you're the one who set the password and then promptly forgot it. This isn't just a theoretical problem; it's a practical hurdle many face. Losing access to important files due to a forgotten password can lead to significant delays and stress.
Recently, a colleague approached me in a state of mild panic. They had an encrypted Word document containing crucial project data, but they couldn't recall the password they had set weeks ago. The deadline was looming, and the information was inaccessible. This situation is a classic example of why understanding how to approach a password protected file recovery, even if it's your own, is essential.
Table of Contents
Understanding the Problem
The core issue was simple: a forgotten password for a Microsoft Word document. While Word offers built-in password protection, it's designed for security, not necessarily for easy recovery once the password is lost. This type of encryption relies on the password to decrypt the file's contents. Without it, the data remains scrambled and unreadable.
Types of Password Protection
It's important to distinguish between different levels of password protection. Some documents might have a password to 'open' the file, while others might have a password to 'modify' it. In my colleague's case, it was a password to open, meaning the entire file was inaccessible. This is generally the stronger form of protection, making recovery more challenging.
Initial Attempts and Frustrations
My colleague's first instinct was to try common passwords they often use. This included variations of their name, important dates, and common word combinations. Unfortunately, none of these yielded results. The frustration mounted as each failed attempt brought them closer to the deadline without any progress.
They then considered if there was a hidden recovery feature within Word. However, Microsoft's security model for document encryption doesn't typically include a 'forgot password' link or a backdoor for users. The responsibility for remembering the password lies entirely with the user.
Exploring Solutions
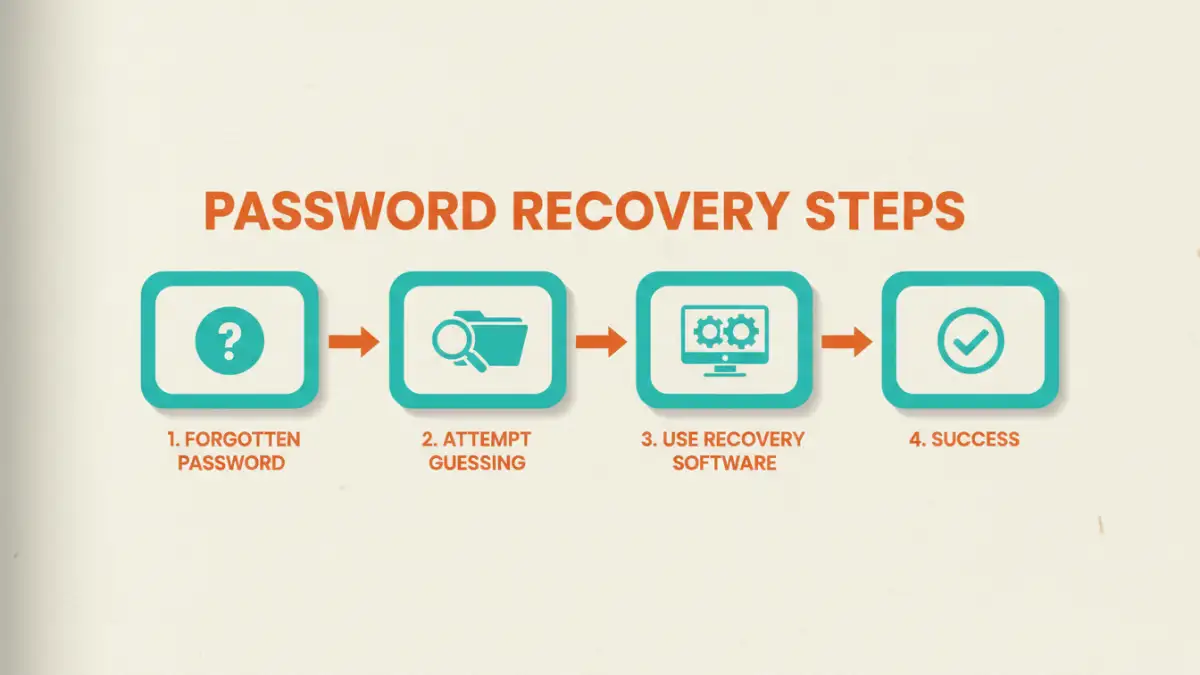
Given the direct methods failed, we had to look at external solutions. This is where the technical expertise comes into play. The goal is to find a way to bypass or crack the password protection without damaging the file's integrity. Several avenues could be explored:
Password Recovery Software
Specialized software exists for recovering lost passwords for various file types, including Microsoft Office documents. These tools typically employ brute-force attacks, dictionary attacks, or a combination of both to guess the password. The effectiveness and speed depend heavily on the complexity of the password and the software's capabilities.
Another option involves exploiting vulnerabilities in older encryption methods, though this is less common with modern document formats. For this specific password protected file scenario, we focused on robust recovery software.
The Recovery Process
We decided to try a reputable password recovery tool designed for Microsoft Office files. The process involved installing the software on a separate machine to avoid any potential interference with the original file. We then loaded the encrypted document into the software.
The software offered different attack methods. We started with a dictionary attack, using a list of common words and my colleague's known password patterns. This was quick but unsuccessful. Next, we moved to a brute-force attack, which systematically tries every possible combination of characters. This is time-consuming and can take hours, days, or even weeks depending on the password length and complexity.
After several hours of the brute-force attack running, the software finally identified the password. It was a complex combination that my colleague had indeed used but had completely forgotten. The relief was palpable when the document opened successfully, allowing them to meet their deadline.
Lessons Learned from the Case
This file recovery case highlighted several key takeaways. Firstly, strong password protection is effective, but it requires diligent password management. Forgetting a password can render important data useless.
Secondly, while recovery is possible, it's not guaranteed and can be time-consuming. Relying on brute-force attacks for complex passwords can be impractical. This underscores the importance of using password managers or secure, memorable password strategies.
Finally, understanding the security features of the tools you use, like Microsoft Office, is crucial. Knowing the limitations and recovery options (or lack thereof) can help prevent such stressful situations in the first place. This password protection story serves as a reminder to back up important data and maintain a secure, organized system for credentials.
Comparison Table: Password Recovery Approaches
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Brute-Force Attack (Software) | Can eventually find any password, regardless of complexity. | Extremely time-consuming, requires significant processing power. Can take days or weeks. | Complex, unknown passwords where other methods fail. |
| Dictionary Attack (Software) | Much faster than brute-force if the password is a common word or phrase. | Ineffective against strong, unique passwords. | Simple or common passwords. |
| Manual Guessing | Instant if successful. No software needed. | Highly unlikely to succeed for anything other than very simple or obvious passwords. High frustration factor. | Very short, simple, or personally significant (and remembered) passwords. |
| Seeking Professional Help | Can be effective if software fails; professionals may have advanced tools/techniques. | Can be expensive, requires trust in third parties, no guarantee of success. | Critical data where other methods have failed and cost is less of a concern. |