
There's a unique sense of relief that comes with an email that just says "Audit Passed." For our team, that message recently marked the culmination of a months-long effort to overhaul a client's data handling practices. The stakes were high, involving sensitive financial records, and the auditors were known for their meticulous approach. At the heart of our strategy was a comprehensive approach to document encryption.
This wasn't just about ticking a box on a compliance checklist. It was about building a system that was fundamentally secure, where data protection was an integral part of the architecture, not an afterthought. This is our compliance success story, and it highlights how a proactive encryption strategy can turn a stressful audit into a validation of your security posture.
Table of Contents
The Audit Challenge: High Stakes and Higher Expectations
The client operates in the financial sector, meaning every piece of data, from transaction logs to client PII (Personally Identifiable Information), is highly sensitive. The upcoming audit was a standard regulatory requirement, but the penalties for failure were anything but standard. We knew from the start that robust financial document security would be the primary focus.
The auditors' initial questionnaire was extensive, drilling down into our policies for data at rest and data in transit. They weren't just asking if we encrypted data; they wanted to know the specific algorithms, key management protocols, access control policies, and logging mechanisms we had in place. It was clear that a superficial solution wouldn't be enough for passing audits of this caliber.
Identifying the Gaps in Existing Security
Our initial assessment revealed several areas of concern. While some data was encrypted, the implementation was inconsistent. Some legacy systems stored sensitive reports in plaintext, access controls were not granular enough, and there was no centralized key management system. This patchwork approach created vulnerabilities that a skilled auditor would easily identify. We needed a unified strategy that could be consistently applied and, more importantly, proven effective.
Our Encryption Strategy: A Multi-Layered Approach

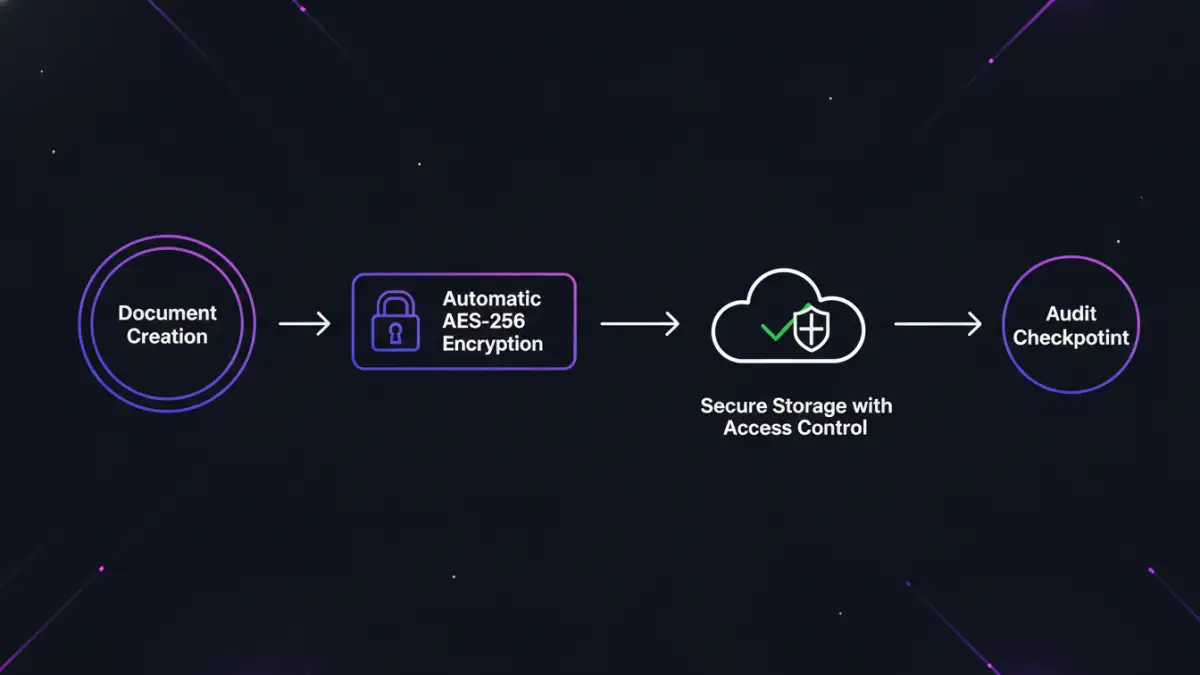
Our goal was to implement end-to-end encryption. This meant ensuring data was protected from the moment it was created until it was securely archived or deleted. We broke our strategy down into two core components: encryption standards and access management.
First, we standardized on AES-256 for all data at rest. This is a widely recognized and trusted symmetric encryption algorithm that provides an excellent balance of security and performance. For data in transit, we enforced TLS 1.2 and above for all internal and external communications, ensuring that data couldn't be intercepted as it moved across networks.
Implementing Robust Key Management
Encryption is only as strong as the security of its keys. A major part of our project involved deploying a dedicated Key Management Service (KMS). This allowed us to centralize the creation, rotation, and revocation of encryption keys. By using a KMS, we could enforce policies that automatically rotated keys on a set schedule and maintain a detailed audit trail of every key's usage. This was a critical piece for demonstrating control to the auditors.
Navigating the Data Encryption Audit
When the auditors arrived, we were prepared. Instead of just presenting policy documents, we were able to walk them through live demonstrations. We showed them how a new document was automatically encrypted upon being saved to our servers. We pulled logs from our KMS to show key rotation schedules and access requests. This transparency built a huge amount of trust.
The auditors were particularly interested in our access control lists (ACLs) and how they integrated with the encryption system. We demonstrated that even an administrator with server access could not view the contents of an encrypted file without being explicitly granted decryption permissions via their role. This separation of duties was a key factor in passing the audit, as it proved our system was resilient against insider threats.
Key Takeaways for Your Own Audit
Reflecting on the process, a few core principles stand out as being essential for success. First, be proactive. Don't wait for an audit notification to start thinking about security. Embed encryption into your development lifecycle and data handling processes from day one. This makes compliance a natural outcome of good engineering, not a frantic last-minute scramble.
Second, document everything. Maintain clear, concise documentation on your encryption architecture, key management policies, and access controls. This makes the auditor's job easier and shows that your approach is deliberate and well-managed. These steps were fundamental to our document encryption success and can serve as a blueprint for any organization facing a similar challenge. Finally, focus on provability. It's not enough to say you do something; you must be able to prove it with logs, demonstrations, and clear evidence.
Encryption Standards Comparison
| Standard | Key Size | Security Level | Common Use Case |
|---|---|---|---|
| AES-256 | 256-bit | Very High | Securing top-secret government data, financial document security |
| AES-128 | 128-bit | High | General purpose encryption, performance-sensitive applications |
| RSA | 2048-bit or higher | Very High (Asymmetric) | Digital signatures, secure key exchange (e.g., TLS/SSL) |
| Triple DES (3DES) | 168-bit | Medium (Legacy) | Older financial payment systems, being phased out |