
A few years back, my team was on the verge of landing a massive enterprise client. The deal hinged not just on our product's features, but on one critical question from their CISO: 'How will you protect our data during and after this sales process?' That moment crystallized a lesson I carry with me to this day: for big clients, security isn't a feature, it's the foundation of trust.
Sending a proposal as a simple email attachment is easy, but it screams 'small-time.' When you're courting a client whose data is their most valuable asset, demonstrating a commitment to security from the very first interaction is non-negotiable. This isn't just about closing a deal; it's about starting a partnership on the right foot, proving you're a custodian they can rely on.
Table of Contents
Why Security Is the Ultimate Sales Tool
When you engage with a large organization, you're not just selling software or a service; you're selling a promise of reliability and safety. Their legal, compliance, and IT departments are all stakeholders. A weak approach to document handling can raise red flags that kill a deal before it even gets to the negotiation table. Strong client data protection is a powerful differentiator.
Think of it from their perspective. They are about to share sensitive internal data, strategic plans, and financial information. If you handle your own proposal with casual insecurity, they will assume you'll treat their data the same way. Conversely, using a secure, professional method shows you understand their world and respect their processes. This proactive stance is a hallmark of business security success.
The Pre-Contract Phase: Secure Proposal Sharing
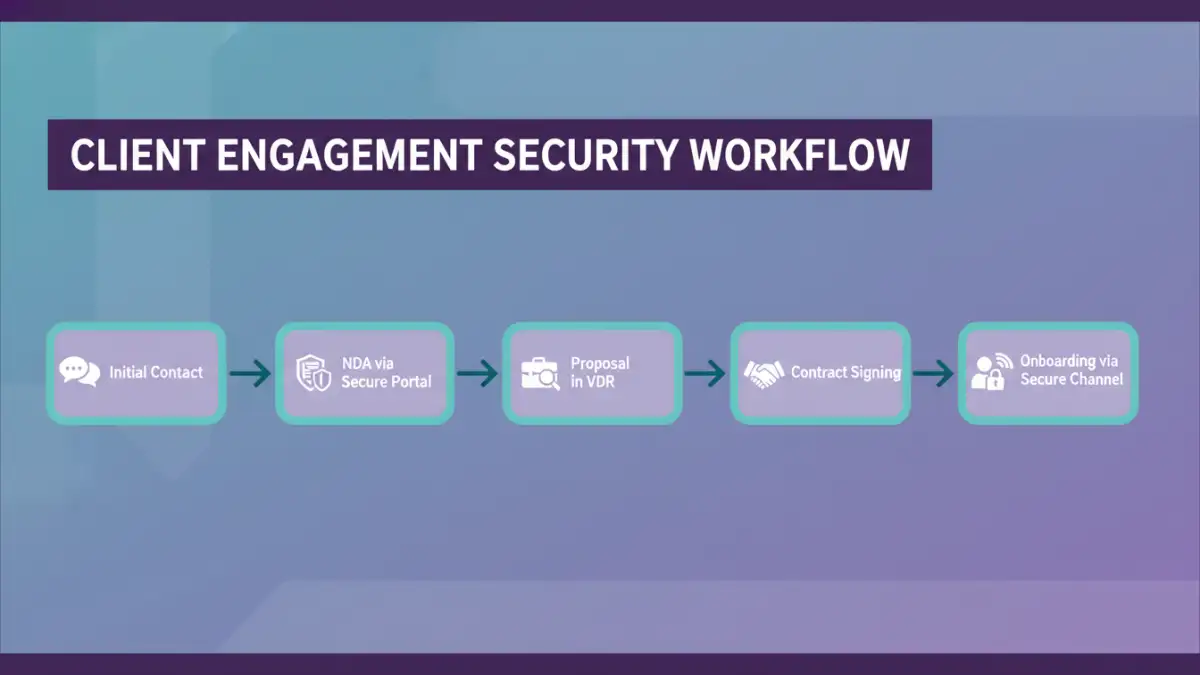
The initial stages of engagement are your first, and perhaps most important, opportunity to demonstrate your security posture. This is where you move beyond simple email and embrace professional tools for secure proposal sharing. Every document, from the Non-Disclosure Agreement (NDA) to the final quote, should be handled with care.
Choosing the Right Platform
Forget emailing PDFs. The best approach is using a dedicated platform. A Virtual Data Room (VDR) or a secure client portal provides a controlled environment. These tools offer features that are impossible with standard email, such as tracking who has viewed a document, when they viewed it, and for how long. This gives you valuable engagement insights while assuring the client their data is contained.
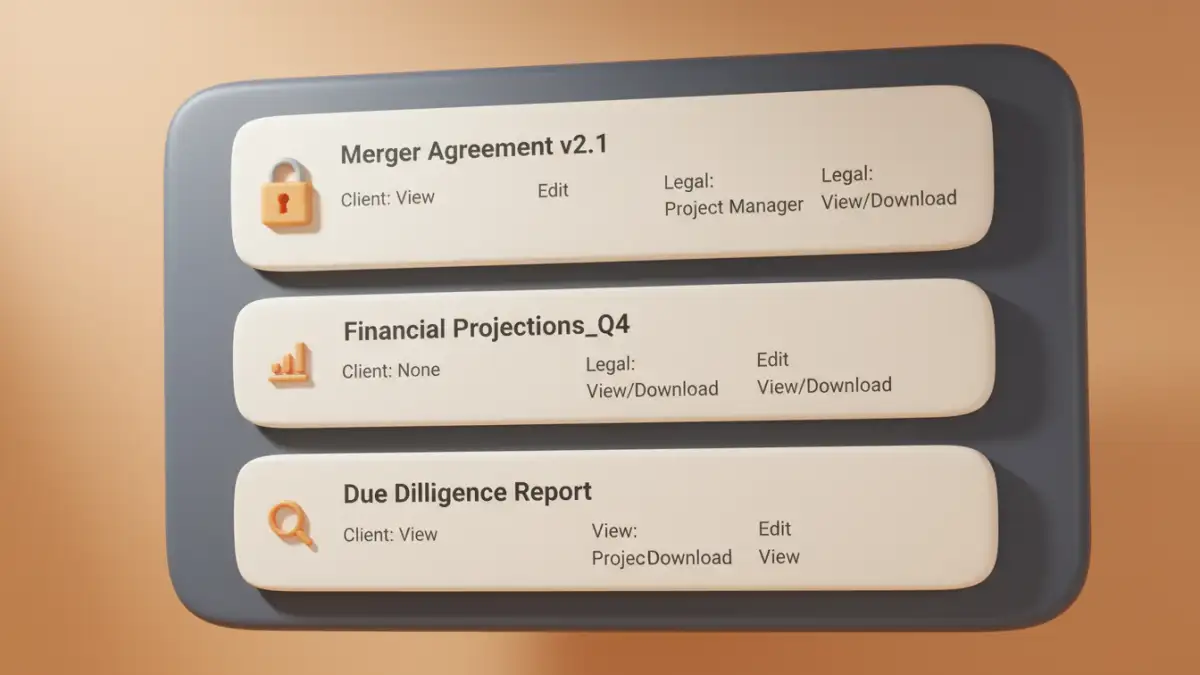
Access Control and Watermarking
Granular control is key. You should be able to set specific permissions for each user. For instance, the client's project manager might have download rights for a technical spec sheet, while their legal team has view-only access to the Master Service Agreement (MSA). Dynamic watermarking, which stamps the viewer's email and the date on the document, is another powerful deterrent against unauthorized sharing.
Building a Secure Onboarding Workflow
Once the contract is signed, the need for security intensifies. The onboarding process often involves exchanging highly sensitive information: API keys, user credentials, internal network diagrams, and proprietary business logic. A haphazard process using shared folders with loose permissions is a recipe for a breach.
We established a dedicated, encrypted onboarding portal for our major clients. All documentation, credentials, and project assets were stored there, accessible only to named individuals with multi-factor authentication (MFA) enabled. We provided a clear audit trail showing every single access event. This not only protected the data but also streamlined the process, preventing the chaos of tracking down information scattered across dozens of email threads.
The Technology Stack for Encrypted File Sharing
Underpinning any good security strategy is a solid technology stack. When discussing our methods with clients, I find it helpful to be transparent about the technologies we use. It demystifies the process and builds confidence.
At its core, any secure document sharing system should use end-to-end encryption. This means the data is encrypted on the sender's device and only decrypted on the recipient's device. For data in transit, TLS 1.2 or 1.3 is the standard. For data at rest (stored on a server), AES-256 is the gold standard of encryption. When a client's technical team asks, being able to confidently state that you use these standards goes a long way.
Furthermore, the platform should be compliant with relevant regulations like GDPR, HIPAA, or CCPA, depending on the client's industry and location. Having these certifications ready provides instant credibility and shows you've done your homework. It transforms the security conversation from a potential weakness into a significant strength.
Document Sharing Method Comparison
| Method | Security Level | Key Features | Best For |
|---|---|---|---|
| Email Attachment | Very Low | Convenient, universal. | Non-sensitive, public information only. |
| Standard Cloud Storage (e.g., Google Drive) | Medium | Password-protected links, basic permissions. | Internal team collaboration, low-risk client files. |
| Secure File Transfer Protocol (SFTP) | High | Encrypted transfer, requires client software. | Technical clients, transferring large batches of data. |
| Virtual Data Room (VDR) | Very High | Granular permissions, audit trails, watermarking, Q&A logs. | High-stakes deals, M&A, secure proposal sharing. |