
A recent conversation with a CTO in the fintech space really highlighted the shifting landscape of cybersecurity compliance. We were discussing the challenges of keeping security policies ahead of both threats and regulations, and the New York Department of Financial Services (NYDFS) Part 500 came up. The latest amendments are no longer just suggestions; they are prescriptive mandates that demand immediate attention from technical teams.
For those of us building and maintaining systems in the financial sector, these changes are significant. They move beyond the previous risk-based approach to enforcing specific controls, particularly around user access and data protection. Understanding these new rules isn't just about avoiding fines—it's about fundamentally strengthening our security posture against increasingly sophisticated attacks.
Table of Contents
What's Changing with NYDFS Part 500?
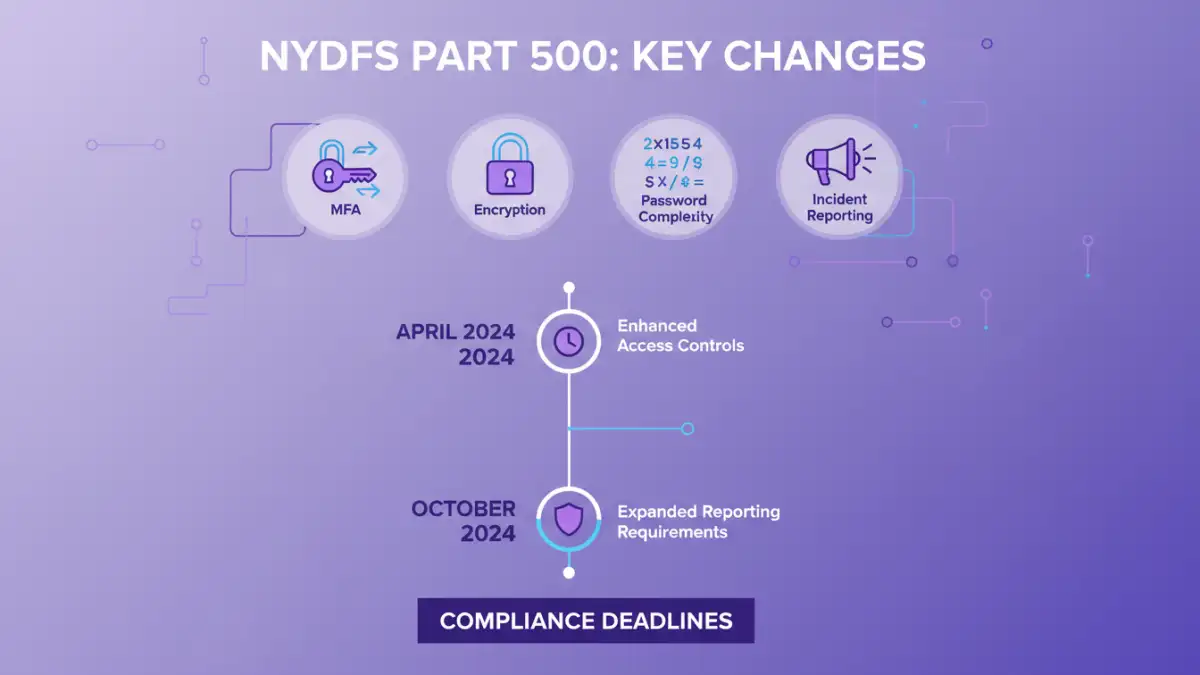
The second amendment to the NYDFS Cybersecurity Regulation, commonly known as Part 500, represents a major evolution in regulatory expectations. Initially, the regulation allowed companies more flexibility to implement security controls based on their individual risk assessments. While that flexibility remains in some areas, the amendments introduce more rigid, specific requirements that leave little room for interpretation.
The primary driver for this change is the escalating threat environment. Ransomware attacks, data breaches, and sophisticated phishing campaigns have shown that a baseline level of security is necessary across the board. The NYDFS has responded by mandating specific technologies and practices it deems essential for protecting consumer data and the stability of the financial system. This shift directly impacts how we as engineers design authentication systems and manage data.
Deconstructing the New Password Requirements

Password policies have been a cornerstone of security for decades, but the Part 500 amendments modernize the approach significantly. The regulation now explicitly requires covered entities to implement stronger controls that reflect current best practices, moving away from simple complexity and rotation rules that have proven insufficient.
Mandatory Multi-Factor Authentication (MFA)
One of the most significant changes is the mandate for multi-factor authentication (MFA). Previously, MFA was recommended based on risk. Now, it is required for any individual accessing an entity's information systems. This isn't just for remote access anymore; it applies to internal access as well, especially for privileged accounts. From a technical standpoint, this means integrating MFA solutions across a wide range of applications, from internal dashboards to cloud services. I've worked on projects where retrofitting MFA into legacy systems was a major challenge, requiring careful planning and often custom development work to ensure a seamless user experience.
Stricter Controls for Privileged Accounts
The amendments place a special focus on privileged accounts—those with elevated access to sensitive systems and data. The regulation now requires entities to limit the number of privileged accounts and restrict access functions to only what is necessary. Furthermore, password-based authentication for these accounts is being phased out in favor of more secure methods, pushing organizations towards solutions like Privileged Access Management (PAM) systems that don't rely on static credentials.
The Expanded Scope of Data Encryption
While the original Part 500 required encryption of nonpublic information (NPI), the amendments clarify and expand upon these data encryption requirements. The goal is to ensure that sensitive data is protected regardless of where it resides or how it's being transmitted.
Encryption for Data In Transit and At Rest
The rule has always covered encryption for data in transit over external networks and for data at rest. However, the new language reinforces the need for strong, industry-standard cryptographic protocols (like TLS 1.2 or higher). It also implicitly pushes companies to have a comprehensive data discovery and classification program. You can't encrypt what you don't know you have. In one compliance audit I was involved in, we discovered several legacy data stores containing NPI that were completely unencrypted because they were overlooked in the initial assessment.
Asset Management and Data Governance
A key part of meeting the NYDFS password encryption mandates is having a robust asset inventory. The amendments require entities to maintain a complete and accurate inventory of their information systems, including details on data flows and classifications. This inventory is the foundation for applying the correct encryption controls. Without it, ensuring compliance becomes a guessing game, and gaps are almost inevitable. This requirement forces a level of discipline around IT governance that many organizations have historically lacked.
A Practical Plan for Implementation and Compliance
Achieving compliance with these new rules requires a structured approach. It's not something that can be handled with a few quick fixes. For any technical leader or engineer tasked with this, I'd recommend a phased approach.
First, conduct a thorough gap analysis. Compare your current security controls against the specific requirements of the amended Part 500. This involves reviewing everything from your password policy documents to your network architecture diagrams. Second, prioritize remediation efforts. The MFA mandate is a high-priority item with a clear deadline. Tackle the most critical and time-sensitive requirements first. Third, update your policies and procedures. It's not enough to implement the technology; you must also document the new controls and train your employees on them. Finally, establish a continuous monitoring program. Compliance is not a one-time project. You need systems in place to monitor for policy deviations and ensure your controls remain effective over time.
NYDFS Part 500 Amendment Comparison
| Control Area | Previous Requirement (Risk-Based) | New Mandate (Prescriptive) | Key Technical Implication |
|---|---|---|---|
| Multi-Factor Authentication (MFA) | Required based on risk assessment. | Mandatory for all access to information systems. | Universal integration of MFA solutions. |
| Password Policies | Periodic changes and complexity rules. | Must meet NIST standards or be part of a comprehensive program. | Adoption of passwordless methods or stronger complexity. |
| Privileged Access | General controls based on risk. | Strict limitations, phasing out passwords for privileged accounts. | Implementation of Privileged Access Management (PAM) tools. |
| Asset Inventory | Required but less specific. | Must be comprehensive and inform governance policies. | Requires automated discovery and classification tools. |
| Incident Response | Plan required. | Specific requirements for preparation, testing, and communication. | Mandatory annual testing and drills. |