
The days of every sensitive document living safely behind a corporate firewall are long gone. Today, data is fluid. It flows between cloud applications like Google Drive and Microsoft 365, gets accessed on personal devices from home offices, and is shared with external collaborators via Slack or Teams. This new reality has exposed a critical flaw in how we've traditionally approached data security.
For years, we relied on Data Loss Prevention (DLP) systems built on a simple premise: find specific keywords or patterns (like credit card numbers) and block them from leaving the network. I've configured these systems myself, and the constant battle with false positives and the inability to understand context was a huge drain on resources. A marketing team sharing a redacted case study would get blocked just like a malicious actor trying to exfiltrate a customer list. The old model just doesn't scale for the way we work now.
Table of Contents
The Cracks in Traditional Data Loss Prevention
Traditional DLP solutions were designed for a different era—one where the network perimeter was the primary line of defense. They function like a security guard checking IDs at a single entrance. In today's distributed environment, data has countless exit points, and these legacy systems simply can't keep up.
The Problem of Static Rules
The core issue with older DLP is its reliance on rigid, predefined rules. These systems use regular expressions and keyword matching to identify sensitive data. While this can catch obvious violations, it completely lacks an understanding of context. It can't tell the difference between a developer sharing code snippets in a secure repository and an employee pasting proprietary code into a public forum. This leads to an endless stream of alerts, a high rate of false positives, and frustrated users whose legitimate workflows are constantly interrupted.
Blind Spots in the Cloud and Collaboration Tools
Another major failure point is visibility. Traditional DLP is often endpoint or network-focused, leaving massive blind spots in cloud services and collaboration tools. It might not see a file being shared improperly from a corporate OneDrive account to a personal Gmail account, or sensitive data being discussed in a private Slack channel. This is a critical gap in providing effective remote work file safety.
What Defines Intelligent Data Protection?

This is where the concept of **next generation document security** comes into play. It's not just an upgrade; it's a complete paradigm shift. Instead of just looking at the *content* of a file, it analyzes the *context* surrounding it. It moves beyond simple pattern matching to understand the 'who, what, where, when, and why' of data access and movement.
This intelligent data protection approach integrates deeply with cloud platforms and identity systems. It knows who the user is, what their role is, what device they're on, and whether their current action is normal or anomalous. This holistic view is essential for preventing data leaks without crippling productivity.
Key Pillars of Modern Document Security
An intelligent data protection platform is built on several key technologies that work together to provide comprehensive coverage. These pillars move security from a reactive, rule-based function to a proactive, risk-adaptive one.
Automated Data Classification
You can't protect what you don't know you have. Modern systems use machine learning to automatically scan, identify, and classify data at scale. It can recognize Personally Identifiable Information (PII), financial records, intellectual property, and other sensitive categories without requiring manual tagging. Once classified, appropriate policies can be automatically applied.
User and Entity Behavior Analytics (UEBA)
UEBA is the brain of the operation. It establishes a baseline of normal behavior for each user and entity (like a server or application). When it detects a deviation—for example, an accountant suddenly trying to access engineering source code at 3 AM from an unrecognized location—it flags the activity as high-risk. This is crucial for catching insider threats and compromised accounts.
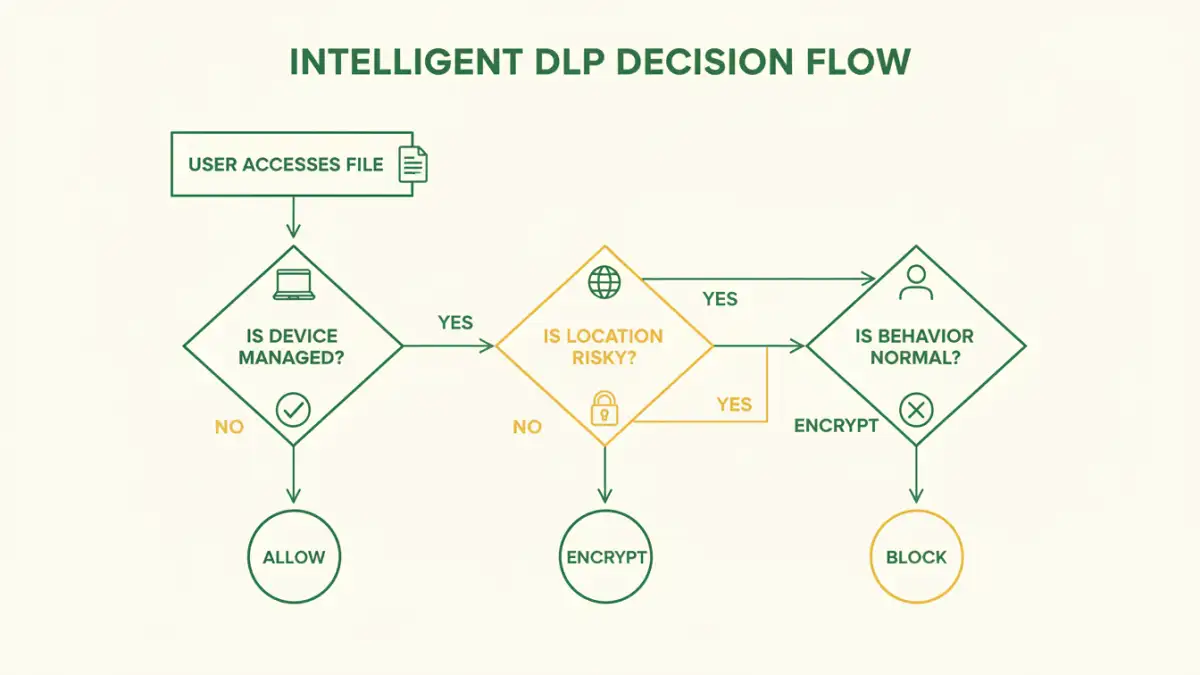
Context-Aware Policy Enforcement
This is where intelligence translates into action. Instead of a simple 'allow' or 'block' rule, policies become dynamic. For instance, a policy might allow a user to view a sensitive file on a corporate laptop but prevent them from downloading it to a personal device. It might allow sharing within the organization but require manager approval for external sharing. This granular control is vital for cloud document security.
Implementing a Modern DLP Strategy
Adopting an intelligent data protection strategy doesn't have to be an overwhelming, all-at-once project. A phased approach is often the most effective way to see immediate value and build momentum for a full-scale rollout.
First, begin with discovery and visibility. Deploy a solution that can map out where your sensitive data resides across all your cloud and on-premises storage. Understanding your risk profile is the essential first step. From there, focus on protecting your most critical data—your 'crown jewels'—and apply context-aware policies to the users and groups who access it most frequently. This targeted approach allows you to address the biggest risks first.
Comparison: Traditional DLP vs. Intelligent Data Protection
| Feature | Traditional DLP | Intelligent Data Protection |
|---|---|---|
| Detection Method | Keyword & pattern matching (RegEx) | Machine learning, behavioral analysis, content inspection |
| Focus | Content-based (what is in the file) | Context-based (who, what, when, where, why) |
| Accuracy | High rate of false positives | Low false positives due to contextual understanding |
| Coverage | Primarily network perimeter and endpoints | Cloud, SaaS apps, email, endpoints, and network |
| Policy Enforcement | Static and rigid (block/allow) | Dynamic and adaptive (e.g., block download, encrypt, notify) |
| Primary Use Case | Compliance and basic data exfiltration blocking | Preventing data leaks, insider threat detection, remote work file safety |