
The sheer volume of digital documents we create daily is staggering. From sensitive client contracts to internal financial reports, manually classifying and securing every single file is no longer a feasible strategy. It's an open invitation for human error and security breaches, a problem I've seen play out in various engineering environments.
Traditional security measures like folder-level permissions and password protection are static. They are gatekeepers, but not intelligent ones. They can't adapt to evolving threats or understand the context of who is accessing what, when, and why. This is where the next evolution in data protection is taking place.
Table of Contents
The Limitations of Traditional Document Security
For years, we've relied on a fairly standard toolkit for document security: access control lists (ACLs), password protection, and manual classification. An administrator would set permissions for a folder, and that was that. If an employee changed roles, someone had to remember to manually update dozens of permissions. It's a system that simply doesn't scale and is prone to oversight.
Passwords, while a necessary first line of defense, are notoriously weak. Users reuse them, share them, or choose simple ones that are easily cracked. Furthermore, once a user is authenticated, traditional systems have little insight into their behavior. They can't distinguish between a legitimate employee accessing a file for their job and a compromised account exfiltrating gigabytes of data.
How AI Is Revolutionizing Document Protection

Instead of relying on rigid, predefined rules, AI brings context and learning to the table. It transforms document security from a static checklist into a dynamic, intelligent system that actively protects your data. This is where concepts like machine learning file protection really shine.
Automated Document Classification
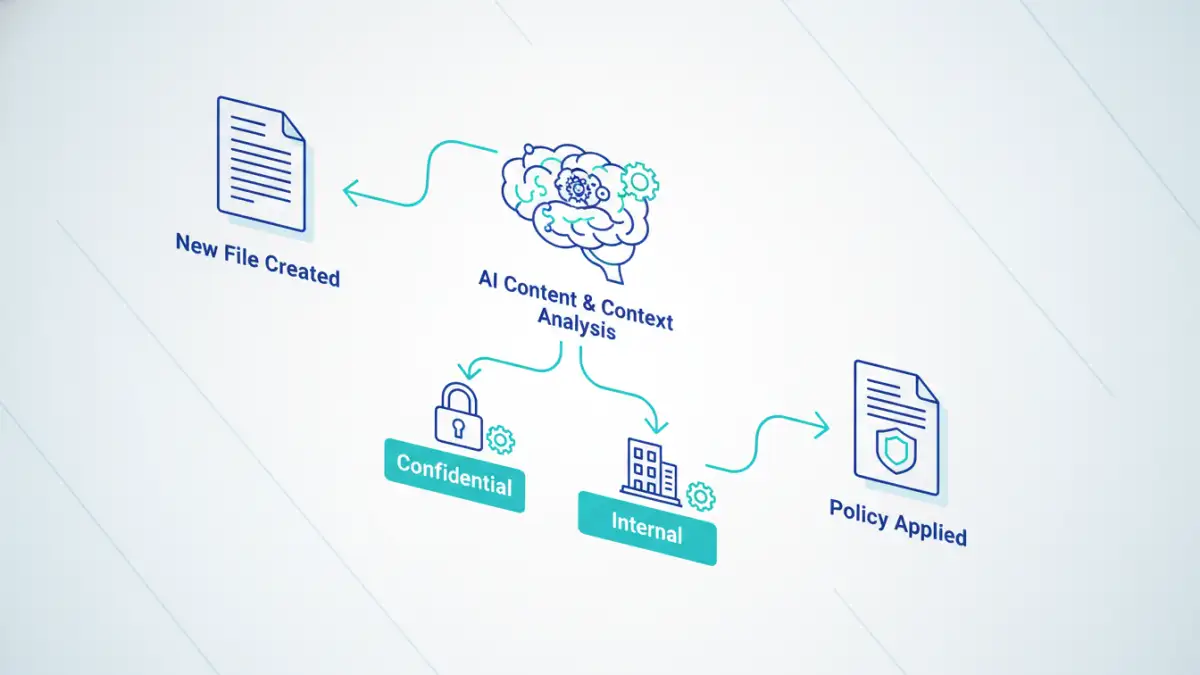
One of the most significant challenges is knowing what data you have and how sensitive it is. AI, specifically Natural Language Processing (NLP), can read and understand the content of documents. It can identify personally identifiable information (PII), financial data, intellectual property, or legal contracts without human intervention. Once identified, it can automatically apply the correct security tag and policy, a process known as automated document classification. For example, an AI can be trained to recognize the format of an invoice and automatically restrict its access to the finance and accounting teams.
Intelligent and Context-Aware Access Control
AI moves beyond static roles. It builds a profile of normal user behavior. Who does this user typically share files with? What time of day are they active? Which devices and locations do they use? An AI-powered system can use this context to make smarter access decisions. If a project manager suddenly tries to download the entire source code repository at 3 AM from an unfamiliar IP address, the system can flag it as anomalous and block the action, even if the user has the 'correct' permissions. This is a form of predictive security that anticipates threats based on behavior.
Proactive Defense with AI Threat Detection
The biggest shift AI brings is the move from reactive to proactive defense. Instead of cleaning up after a breach, the goal is to prevent it from ever happening. The core of this capability is the system's ability to learn what's normal and spot what isn't.
Behavioral Analytics and Anomaly Detection
AI algorithms create a baseline of normal data access patterns across the organization. This allows for powerful ai threat detection capabilities. When behavior deviates significantly from this baseline—like a user accessing an unusually high number of files, or modifying a critical document they haven't touched in years—the system can generate an alert. This helps security teams focus on genuine threats instead of getting lost in a sea of false positives.
Ransomware and Malware Mitigation
Some advanced AI systems can analyze file activity in real-time to detect the tell-tale signs of a ransomware attack. Rapid, sequential encryption of multiple files is not normal user behavior. An AI can detect this pattern within seconds, isolate the affected user account or device, and halt the process before significant damage is done, providing a last line of defense against malicious attacks.
Implementing AI Security and Future Trends
Implementing an AI document security solution is not a flip-of-the-switch process. It involves integrating with your existing data repositories (like SharePoint, Google Drive, or network drives) and an initial training period where the AI learns your organization's unique data landscape and user behaviors. While many platforms are designed to be user-friendly, setting up policies and fine-tuning the models requires careful planning.
Looking ahead, the integration of AI will only become deeper. We can expect AI to dynamically redact sensitive information from a document based on the clearance level of the person viewing it. Imagine a single contract document that shows full financial details to a CFO but automatically hides those same details when opened by a sales representative. The future is not just about locking documents; it's about making data intelligently and securely accessible.
Comparison: Traditional vs. AI-Powered Security
| Feature | Traditional Approach | AI-Powered Approach |
|---|---|---|
| Classification | Manual, user-driven, and often inconsistent. | Automated, content-aware, and consistent policy application. |
| Access Control | Static, role-based permissions that require manual updates. | Dynamic, context-aware access based on user behavior and risk. |
| Threat Detection | Reactive, based on known signatures and post-breach analysis. | Proactive, based on anomaly detection and predictive analytics. |
| Scalability | Poor; becomes unmanageable as data volume grows. | Excellent; learns and adapts as data and user bases expand. |
| Insider Threats | Limited visibility once a user is authenticated. | Effectively identifies compromised accounts and malicious insiders. |