
I recently helped a colleague who was locked out of a critical, encrypted project file. They'd forgotten the password set months ago, and panic was setting in. This experience highlights a common question I hear: just how secure is a password-protected document, and how long would it really take for someone to get in without the password?
The answer isn't a simple number. It can range from milliseconds to longer than the age of the universe. The deciding factors are the password's complexity, the encryption strength of the document format (like PDF or DOCX), and the method used by the attacker. Understanding these variables is key to protecting your sensitive information effectively.
Table of Contents
What Determines Password Cracking Time?
Three core components dictate how long it takes to bypass a document's security. It's a combination of the lock (encryption), the key (password), and the tools used to pick the lock (cracking hardware and software).
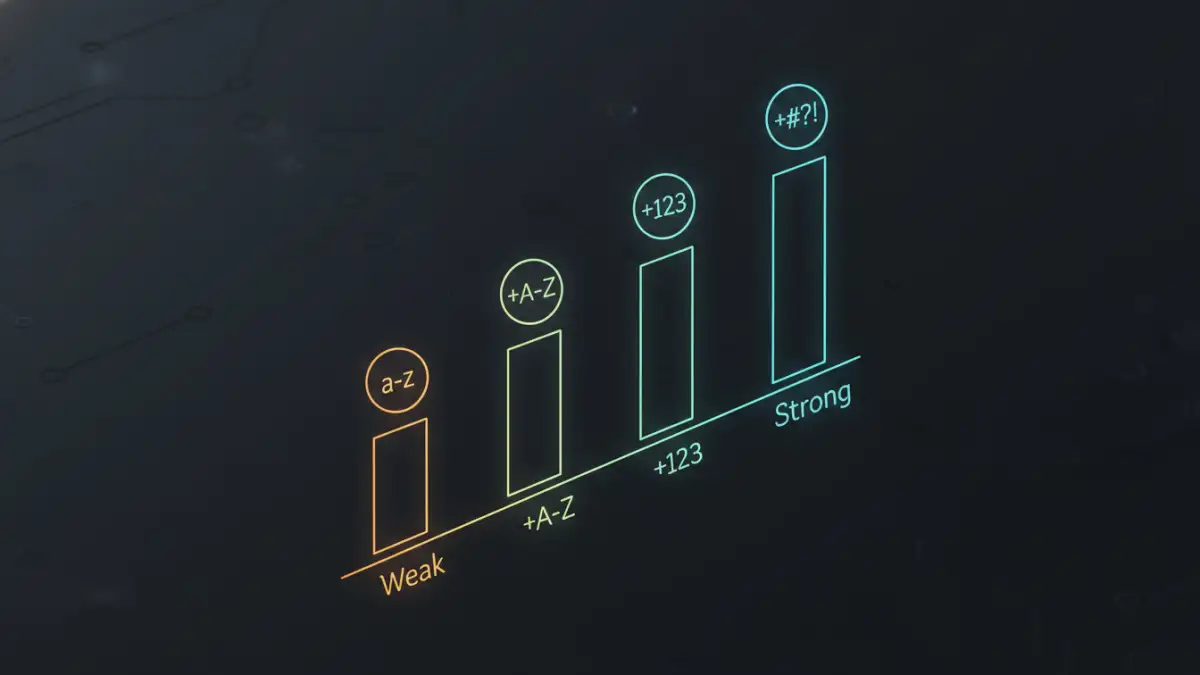
Password Length and Complexity
This is the single most important factor. Each character you add to a password increases the number of possible combinations exponentially. A simple 8-character password using only lowercase letters has about 208 billion possibilities. Add uppercase letters, numbers, and symbols, and that number skyrockets into the quadrillions.
Complexity refers to the variety of character types used. A password that mixes uppercase letters, lowercase letters, numbers, and special characters is exponentially harder to guess than one that uses only one or two character types. Randomness is your best friend here.
Encryption Algorithm Strength
Not all encryption is created equal. Older document formats might use weaker algorithms like 40-bit RC4, which can be broken very quickly with modern computers. Modern formats, like the latest PDF and Microsoft Office versions, use much stronger encryption like AES-256 (Advanced Encryption Standard with a 256-bit key).
AES-256 is the gold standard, used by governments and corporations worldwide. To date, there is no known practical attack that can break it. Any attempt to crack a document password protected with AES-256 must focus on guessing the password itself, not breaking the encryption.
Common Password Cracking Methods Explained
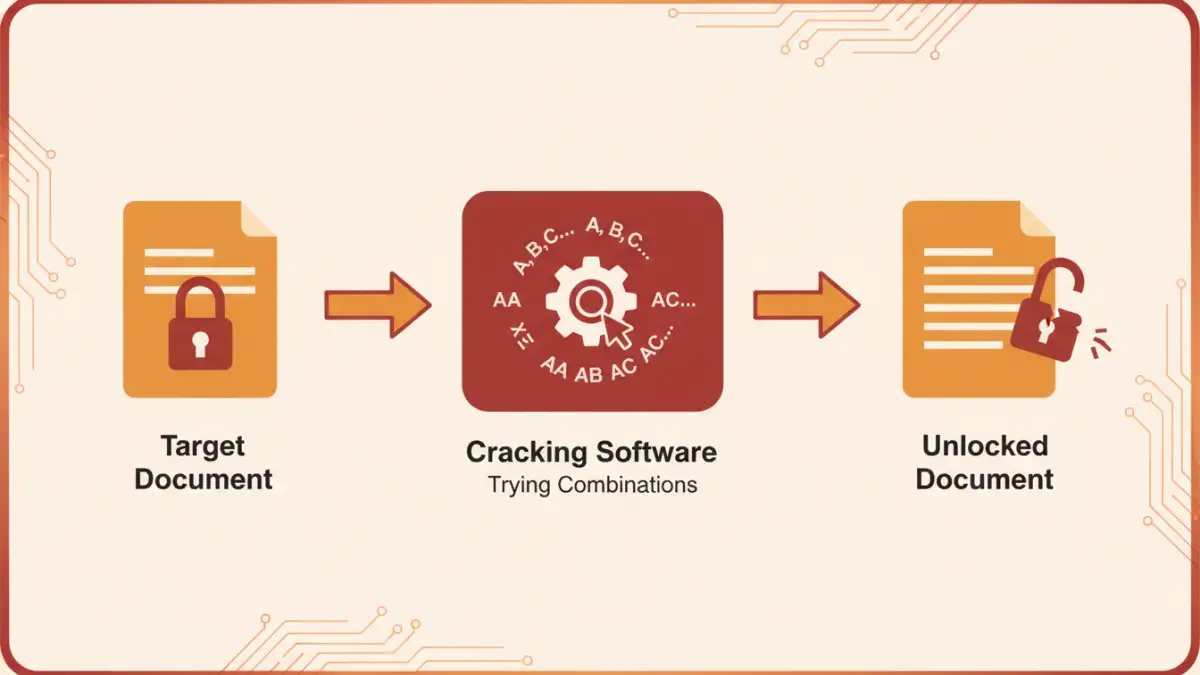
Attackers don't just guess randomly. They use systematic methods and powerful software to test thousands, millions, or even billions of passwords per second. This is where an encryption attack simulation can reveal weaknesses.
Brute-Force Attack
A brute-force attack is exactly what it sounds like: trying every single possible combination of characters until the correct one is found. It's methodical and exhaustive. While it will eventually find any password, its success is entirely dependent on the password's length. For long, complex passwords, a pure brute-force attack is computationally infeasible.
Dictionary Attack
This method is more targeted. It uses a list (a "dictionary") of common words, phrases, names, and previously leaked passwords. An attacker's software will run through this list first, as many people reuse simple passwords like "password123" or "qwerty". This is much faster than a brute-force attack if the password is a common word.
Hybrid and Mask Attacks
A hybrid attack combines dictionary and brute-force methods. For example, it might take a word from a dictionary, like "sunshine," and then add numbers or symbols to it, testing "sunshine2024," "Sunshine!," etc. A mask attack is a more refined brute-force attempt where the attacker has some information about the password's structure, like "it starts with a capital letter and ends with two digits."
Real-World Scenarios and Time Estimates
Let's put this into perspective. Assuming a modern computer that can test billions of passwords per second, the timeframes change dramatically based on password quality. This is where a document security test can show you the real-world risk.
An 8-character password using only lowercase letters could be cracked instantly. Add numbers and mixed case, and it might take a few hours or days. But extend that password to 12 or more characters with a mix of all character types, and the cracking time jumps to thousands or even millions of years. This is why length is so critical.
For example, if you need to brute force pdf password protection that uses strong AES-256 encryption, the focus is entirely on the password. A weak password means the file is vulnerable, regardless of the strong encryption. A strong password makes it practically impenetrable.
How to Create Virtually Uncrackable Passwords
The goal isn't just to make a password hard to guess; it's to make it computationally expensive to crack. You want to force an attacker to spend an impractical amount of time and resources.
Use a Password Manager
As a software engineer, this is my number one recommendation. Don't try to create and remember dozens of unique, complex passwords. Use a reputable password manager to generate and store them for you. It can create truly random 16+ character passwords that are impossible for a human to remember but provide maximum security.
Follow Password Best Practices
If you must create a password manually, follow these rules:
- Length is Key: Aim for a minimum of 16 characters. 12 is the absolute floor, but longer is always better.
- Mix It Up: Use a combination of uppercase letters, lowercase letters, numbers, and symbols.
- Avoid Predictability: Don't use personal information (birthdays, names), common words, or keyboard patterns (like "asdfghjkl"). A good method is to use a passphrase of four or five random words, like "CorrectHorseBatteryStaple".
By implementing these strategies, you can be confident that your protected documents are secure against even the most determined attacks. The time required to crack document password protection you've set up will be measured in centuries, not seconds.
Password Cracking Time Estimates
| Password Length & Complexity | Number of Possibilities | Estimated Time to Crack (Modern PC) |
|---|---|---|
| 8 Characters (lowercase only) | 209 Billion | Instantly |
| 8 Characters (mixed case, numbers) | 6.7 Quadrillion | ~1 Hour |
| 8 Characters (all types) | 7.2 Quadrillion | ~2 Hours |
| 12 Characters (mixed case, numbers) | 3.2 Sextillion | ~200 Years |
| 12 Characters (all types) | 6.0 Sextillion | ~400 Years |
| 16 Characters (all types) | 1.9 Nonillion | ~10+ Quadrillion Years |