
The pressure on healthcare organizations to modernize is immense. Patients now expect instant access to their records, and providers need efficient ways to collaborate. However, this digital shift runs parallel to a growing threat landscape, making the protection of electronic protected health information (ePHI) more critical than ever. Recent updates to HIPAA regulations directly address this tension, creating new requirements for how we handle digital data.
For developers and IT professionals in the healthcare space, these aren't just policy updates; they are technical mandates. Understanding the nuances of these changes is the first step toward building systems that are not only innovative but also robustly compliant and secure.
Table of Contents
Key HIPAA Updates Impacting File Sharing
The latest amendments to the HIPAA Privacy Rule focus heavily on strengthening patient rights and improving care coordination. While not exclusively about file sharing, the implications for how we transmit data are significant. The goal is to remove unnecessary barriers to information flow while simultaneously reinforcing security protocols.
Enhanced Patient Access
A major thrust of the new rules is empowering patients with easier, faster access to their ePHI. This means healthcare providers must have systems in place that allow for the secure delivery of digital records directly to patients. Sending an unencrypted PDF as an email attachment is no longer a defensible practice. We must architect solutions that verify identity and secure the data payload from end to end.
Clarification on Care Coordination
The rules now provide more clarity on sharing ePHI between providers for care coordination. This facilitates better patient outcomes but also widens the circle of data access. As a result, the need for auditable, secure transfer methods is paramount. We need to know who accessed what, when, and why, which requires robust logging and access controls built into our file sharing workflows.
Essential Technical Safeguards for ePHI Protection

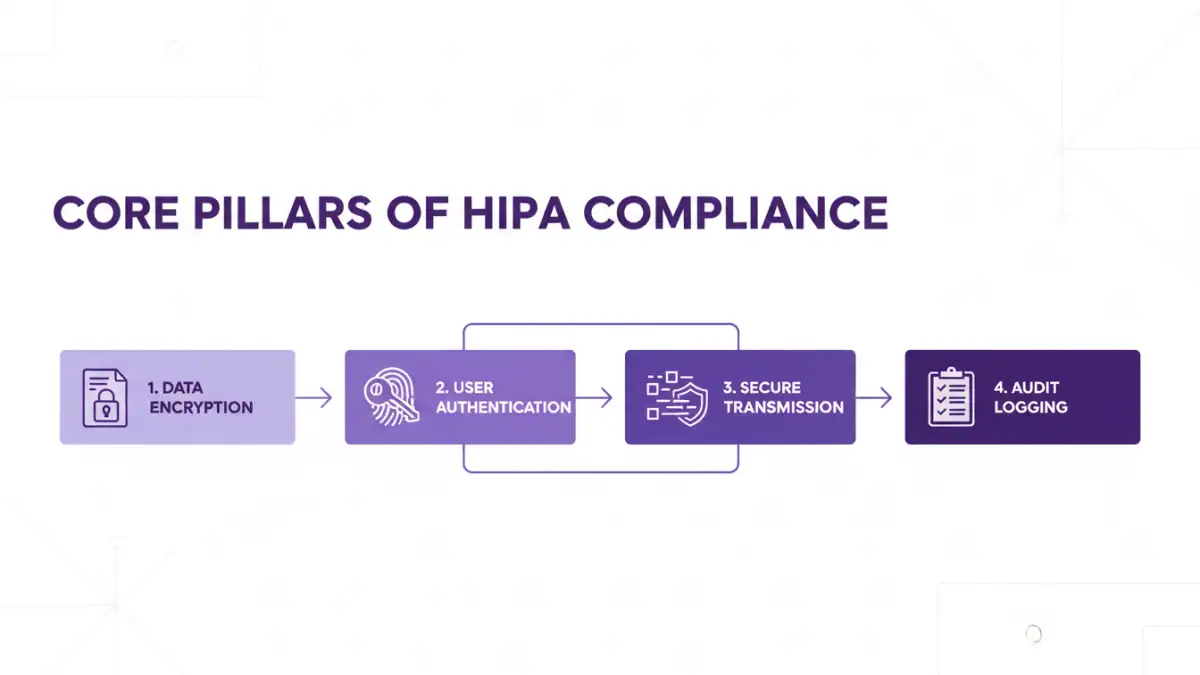
From a technical standpoint, compliance boils down to implementing specific safeguards. These aren't suggestions; they are foundational requirements for any system handling sensitive patient data. In my work building healthcare applications, these three pillars are non-negotiable.
End-to-End Encryption (E2EE)
Encryption is the cornerstone of patient document security. Data must be encrypted both 'at rest' (when stored on a server or device) and 'in transit' (while being sent over a network). Simply using TLS/SSL for transit is not enough. True E2EE ensures that only the sender and the intended recipient can decrypt and read the information, preventing even the service provider from accessing the ePHI.
Access Control and Identity Management
You must be able to prove that only authorized individuals can access ePHI. This involves more than just a username and password. Implementing Role-Based Access Control (RBAC) ensures users only see the data necessary for their job. Furthermore, Multi-Factor Authentication (MFA) should be considered a baseline requirement to prevent unauthorized access from compromised credentials.
Audit Trails and Logging
If a breach occurs, you need to be able to trace what happened. Comprehensive logging is a requirement. Your system must record every instance of ePHI access, including who accessed it, what they accessed, and when. These audit trails are crucial for forensic analysis and for demonstrating compliance to regulators.
Evaluating Compliant Sharing Solutions
Choosing the right platform is a critical decision. Not all file sharing services are created equal, and using a non-compliant tool can lead to severe penalties. When evaluating options, look for providers who will sign a Business Associate Agreement (BAA). A BAA is a legally binding contract that requires the vendor to uphold the same HIPAA security standards as the healthcare provider.
Beyond the BAA, scrutinize the platform's security features. Does it offer the essential safeguards mentioned above? Ask for their security documentation, third-party audit reports (like SOC 2), and details on their data center security. A vendor who is serious about healthcare compliance will have this information readily available. This is a crucial step for achieving compliant hipaa secure file sharing.
Common Compliance Mistakes to Avoid
In practice, I've seen several recurring mistakes that put organizations at risk. One of the most common is the use of consumer-grade file sharing apps (like personal Dropbox or Google Drive accounts) by staff for convenience. These services typically do not meet HIPAA standards and won't offer a BAA, creating a massive compliance gap.
Another pitfall is improper configuration. Even a compliant tool can be rendered insecure if not set up correctly. This includes failing to enforce strong password policies, not enabling MFA, or granting overly permissive access rights to users. Regular security audits and employee training are vital to ensure that both the tools and the people using them are aligned with your compliance strategy.
Comparison of ePHI Sharing Methods
| Sharing Method | Compliance Risk | Key Features | Best For |
|---|---|---|---|
| Standard Email | Very High | None for ePHI protection. Lacks encryption and audit trails. | General, non-sensitive communication only. |
| Consumer Cloud Storage | High | Basic file sharing, but typically no BAA or required controls. | Not recommended for any ePHI. |
| Secure FTP (SFTP) | Medium | Encrypted transit, but lacks user-friendly access controls and robust auditing. | Technical bulk data transfers between systems, not for ad-hoc user sharing. |
| HIPAA-Compliant Platform | Low | BAA, E2EE, MFA, access controls, full audit logs. | All forms of sharing involving ePHI, both internal and external. |