
A common assumption I see in the tech world is that if data is encrypted, you're automatically in the clear if a breach occurs. The logic seems sound: if thieves steal a locked safe but can't open it, have they really stolen the contents? While encryption is a foundational pillar of modern cybersecurity, relying on it as a get-out-of-jail-free card for reporting obligations is a dangerous oversimplification.
The legal landscape is far more nuanced. Many regulations offer a "safe harbor" for encrypted data, but this protection comes with significant caveats. Simply having encrypted files is not enough; the context of the breach, the strength of the encryption, and, most importantly, the security of the encryption keys themselves are what truly matter.
Table of Contents
The Encryption 'Safe Harbor' Explained
Most data breach laws across the United States and globally include a provision often called a "safe harbor." The core idea is that if personal information is rendered unreadable or unusable through methods like encryption, an organization may be exempt from notifying affected individuals and regulators after a security incident. The reasoning is that if the compromised data is gibberish to the attacker, no real harm has occurred.
This provision encourages companies to adopt strong security practices. From a development standpoint, it's why we build encryption into applications and databases from the ground up. The safe harbor is designed to protect both consumers from unnecessary panic and companies from the reputational and financial damage of a breach notification when the actual risk is negligible.
What Qualifies as 'Secure' Data?
For data to fall under this safe harbor, it generally must be encrypted using a standard, industry-accepted algorithm. Regulations are often intentionally vague on specific algorithms to avoid becoming outdated, but they typically look for technologies that have not been compromised and are considered robust by cryptographic experts. Simply putting a password on a ZIP file using a weak, outdated method probably won't cut it.
When Encryption Fails as a Defense

The safe harbor exemption is not absolute. I've seen situations where teams felt secure because their data-at-rest was encrypted, only to find out their notification obligations remained firmly in place after an incident. Several critical factors can nullify this protection.
The Compromised Key Problem
This is the single most common reason the encrypted files breach notification exemption is voided. Encryption is only as strong as the security of its keys. If an attacker gains access to both the encrypted data and the corresponding decryption key, the data is effectively unencrypted. From a legal perspective, the information is considered compromised, and the safe harbor disappears.
Think of it like an attacker stealing your house safe along with the key you left hanging on a hook right next to it. The safe itself is strong, but the poor key management rendered it useless. This is why robust key management systems (KMS) and Hardware Security Modules (HSM) are so critical in enterprise environments. Storing keys separately and securely from the data they protect is non-negotiable.
Navigating the Patchwork of State Privacy Laws
There is no single federal data breach law in the U.S., which creates a complex compliance web. Each state has its own rules, and they differ on what constitutes a breach and the specific requirements for encryption to qualify for a safe harbor. For example, the California Consumer Privacy Act (CCPA) and its successor, the CPRA, have specific definitions of what it means for data to be encrypted.
Some state privacy laws are more prescriptive than others. New York's SHIELD Act, for instance, broadened the definition of private information and requires companies to implement "reasonable" security safeguards. A password protected file breach might trigger notification requirements in one state but not another, depending on the specifics of the law and the nature of the data involved. This legal fragmentation means that what works for compliance in Texas might not be sufficient in Massachusetts.
Practical Steps for Incident Response
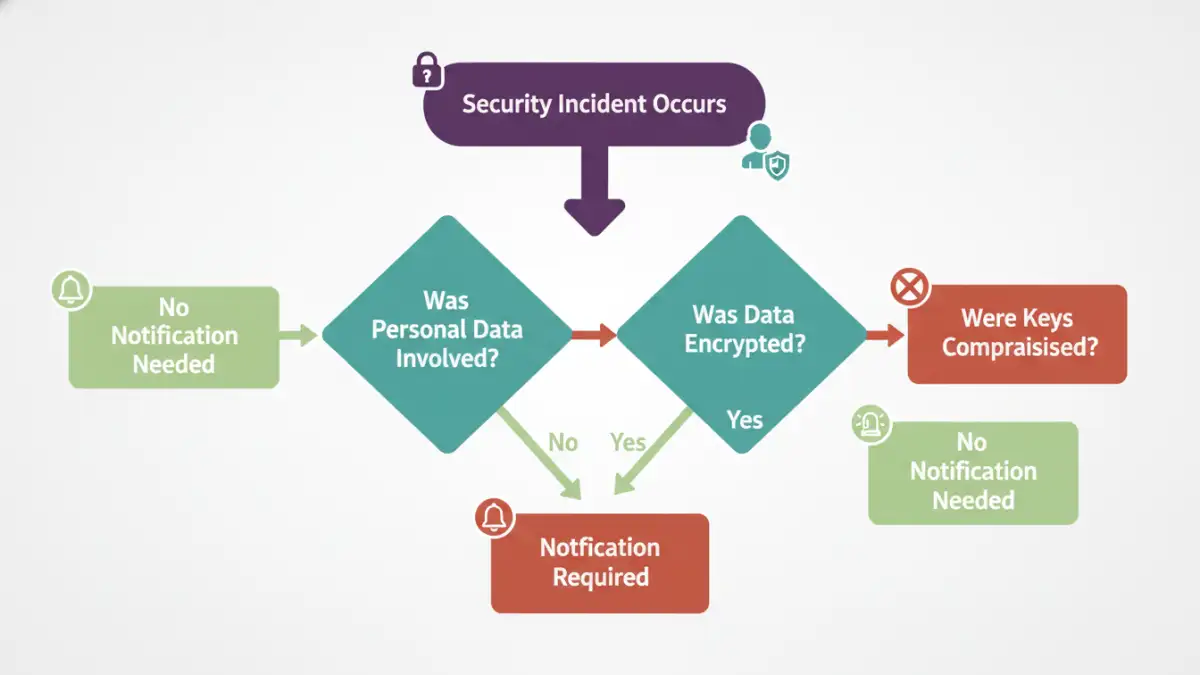
When a security incident involves encrypted data, your response should be methodical. Panic can lead to mistakes that worsen the situation. The goal is to quickly and accurately determine if your safe harbor provision holds up.
First, your incident response team must determine the scope of the breach. What data was accessed? Was it encrypted? Most importantly, is there any evidence that the encryption keys were also compromised? This forensic investigation is the foundation of your response. You need to analyze logs, network traffic, and access patterns to trace the attacker's steps.
Second, consult with legal counsel specializing in cybersecurity incident reporting. They can help interpret the specific data breach laws relevant to the affected individuals' locations. An engineer's definition of "secure" might not align with a legal one. Finally, document everything. A detailed record of your encryption standards, key management policies, and the incident investigation itself will be crucial if you have to defend your decision not to notify.
Breach Notification Requirement Scenarios
| Scenario | Encryption Status | Key Status | Notification Likely Required? |
|---|---|---|---|
| Database files stolen from server | Strong (AES-256) | Keys stored separately and secure | No (Safe Harbor likely applies) |
| Encrypted laptop stolen from an employee's car | Full-disk encryption enabled | Keys also compromised (e.g., password on a sticky note) | Yes (Safe Harbor is voided) |
| Password protected file breach via phishing | Weak ZIP password protection | Key (password) easily brute-forced | Yes (Encryption not considered robust) |
| Cloud storage bucket misconfigured and accessed | Server-side encryption enabled | Keys managed by cloud provider, not compromised | No (If keys were not exposed) |
| Ransomware attack encrypts your encrypted data | Data was already encrypted | Original keys remain secure | Depends on whether data was exfiltrated before being re-encrypted |