
A lawyer I know once sent a draft settlement agreement to opposing counsel via standard email. A few hours later, he realized he'd accidentally sent it to a journalist with a similar name. The frantic scramble to recall the message was a stark reminder of how easily things can go wrong. While human error was the trigger, the underlying issue was the communication channel itself. Email feels instantaneous and private, but it's fundamentally an open system, like sending a postcard through the mail.
For legal professionals, the stakes are incredibly high. Confidentiality isn't just a best practice; it's an ethical and legal obligation. Relying on a technology that was never designed for secure communication introduces significant vulnerabilities that can compromise cases, damage reputations, and lead to serious regulatory penalties.
Table of Contents
The Inherent Flaws of Email Communication
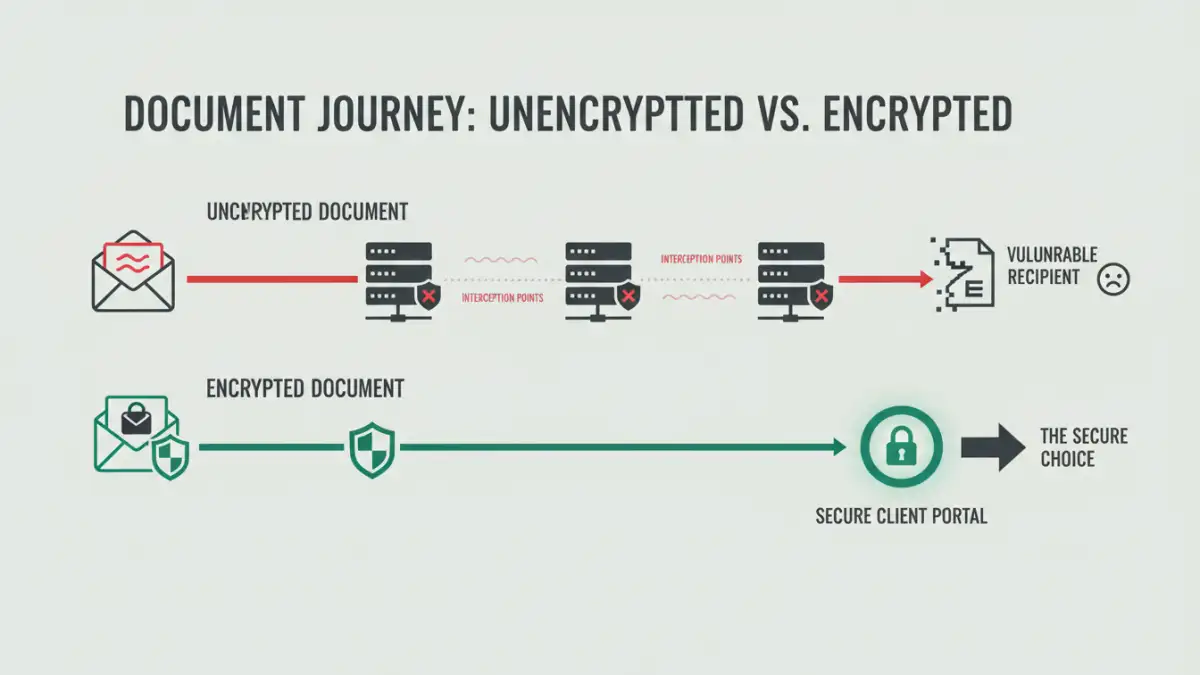
When you send an email, it doesn't go directly from your computer to the recipient's. It travels across the internet, hopping between multiple servers. At each stop, the message can be stored, scanned, or even intercepted if it's not properly encrypted. This is the core of the unencrypted email risk that many people overlook.
Most standard email services only encrypt the connection between your device and their server (called TLS encryption). However, the message itself often sits in plain text on the servers it passes through. Think of it as putting a letter in a secure mailbox, but once the mail carrier picks it up, it's carried in an open basket. Anyone with access to the route can potentially read it.
Data-in-Transit vs. Data-at-Rest
Security professionals talk about two states of data: in-transit and at-rest. Data-in-transit is your email traveling across the network. Data-at-rest is the email sitting on a server or a hard drive. Standard email protocols offer some protection for data-in-transit but very little for data-at-rest on intermediary servers. A sophisticated attacker could target these servers to access sensitive communications without ever breaching the sender's or receiver's direct accounts.
Critical Risks for the Legal Profession

The dangers of emailing legal files go beyond simple privacy concerns. For law firms and corporate legal departments, the consequences can be catastrophic, directly impacting case outcomes and professional standing.
Breach of Attorney-Client Privilege
The foundation of the legal profession rests on privileged communication. If an email containing confidential legal advice is intercepted or accessed by a third party, it could be argued that the privilege has been waived. An insecure communication method demonstrates a lack of reasonable care in protecting that confidentiality, which can be exploited by opposing counsel. The integrity of your attorney client privilege email communications is paramount.
A breach doesn't have to be a malicious hack. Forwarding an email chain to the wrong person, a misconfigured server, or even a data request to a cloud email provider could expose privileged information. Once that confidentiality is broken, it's nearly impossible to restore.
Safer Channels: Secure Alternatives to Email
Recognizing the flaws in standard email is the first step. The next is adopting tools specifically designed for secure communication. Fortunately, there are several robust and user-friendly options available that offer far greater protection for sensitive legal work.
The goal is to move from a model of 'hope it's secure' to one of 'verified security.' These platforms are built with end-to-end encryption, access controls, and audit trails as core features, not afterthoughts. Integrating these tools into your workflow is a critical aspect of modernizing the security of emailing legal documents.
Key alternatives include:
- Secure Client Portals: Many legal practice management software suites include a client portal. This creates a single, secure, and centralized space where you can share documents, send messages, and collaborate with clients. All data is encrypted both in-transit and at-rest, and access is controlled by unique logins and passwords.
- Encrypted File-Sharing Services: Platforms like Tresorit, Sync.com, or Citrix ShareFile are designed for secure document exchange. They use end-to-end encryption, meaning only the sender and intended recipient can decrypt and view the files. Many offer features like expiring links, download limits, and detailed access logs.
- End-to-End Encrypted Email: Services like ProtonMail or Tutanota encrypt the message content on the sender's device and only decrypt it on the recipient's device. If someone intercepts the email along the way, they'll only see garbled, unreadable text. This is a direct solution to the unencrypted email risk.
Implementing a Secure Communication Strategy
Technology alone isn't a complete solution. It must be paired with clear policies and consistent training. A firm-wide commitment to security is essential to protect your clients and your practice effectively.
Start by creating a formal information security policy that explicitly states which types of documents can and cannot be sent via standard email. The policy should designate approved secure platforms and provide clear instructions for their use. This removes ambiguity and sets a clear standard for everyone in the firm.
Client education is also crucial. Explain to your clients why you are using a secure portal or file-sharing service. Frame it as a measure to protect their confidential information. Most clients will appreciate the extra step, as it demonstrates your commitment to their privacy and security. Regular training sessions for all staff will reinforce these policies and ensure everyone understands the risks and the proper procedures.
Comparison of Secure Communication Methods
| Method | Security Level | Ease of Use | Best For |
|---|---|---|---|
| Standard Email | Low | Very High | Non-confidential scheduling and general inquiries. |
| Password-Protected PDF via Email | Low-Medium | High | Adding a minimal layer of protection, but the password is often sent separately via insecure email. |
| End-to-End Encrypted Email | High | Medium | Direct, secure messaging when both parties use a compatible service. |
| Secure File-Sharing Service | Very High | Medium | Sharing large or highly sensitive documents with external parties on a case-by-case basis. |
| Integrated Client Portal | Very High | High (for clients) | Ongoing, secure communication and document exchange throughout a legal matter. |