
I was recently helping a company audit their data practices, and they pointed to a dusty binder labeled "Document Retention Policy." Their rule was simple: keep everything for seven years. In the past, that might have been a safe, if inefficient, bet. But with the California Privacy Rights Act (CPRA) now in full effect, that kind of broad, one-size-fits-all approach is a compliance nightmare waiting to happen.
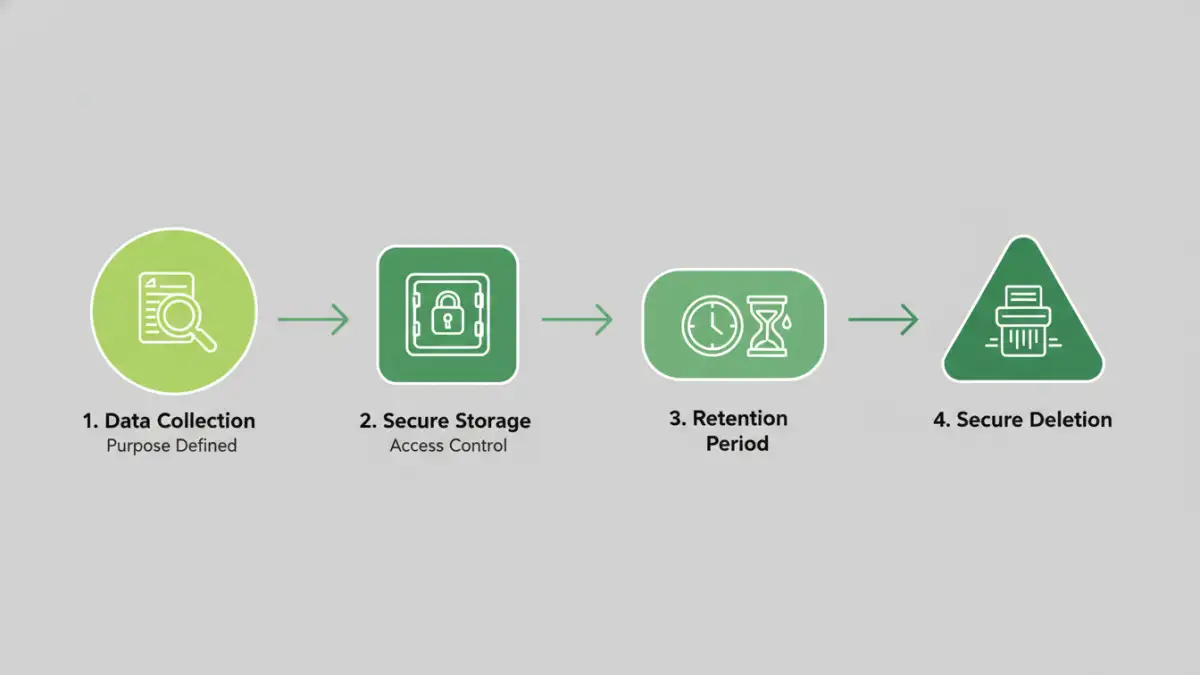
CPRA forces us to be much more deliberate. It’s no longer about how long we *can* keep data, but how long we *should*—and we need to be able to justify it. This shift fundamentally changes how we think about the entire lifecycle of a document, from creation to its final, secure deletion.
Table of Contents
CPRA Fundamentals: Beyond the Basics of CCPA
For those of us who have been working with the California Consumer Privacy Act (CCPA), it’s tempting to see CPRA as a minor update. It’s not. CPRA significantly expands on CCPA's foundation, introducing new concepts that directly impact our data handling protocols. Two of the most important are "purpose limitation" and "data minimization."
Purpose limitation means you can only collect and use consumer data for the specific, disclosed purposes you told the consumer about. Data minimization requires you to collect only the data that is reasonably necessary and proportionate to achieve that purpose. The days of collecting data "just in case" it might be useful later are over. Every piece of data in every document needs a reason to exist.
From Data Hoarding to Data Justification
This represents a major philosophical shift. Previously, storage was cheap, and hoarding data seemed like a good strategy for future analytics or business intelligence. Now, every document containing personal information is a liability with a ticking clock. Its existence must be continuously justified against the purpose for which it was collected. This is a core principle of effective cpra document security.
Rethinking Document Retention Policies

Under CPRA, your retention period for any document containing personal information must be "no longer than is reasonably necessary" for the disclosed purpose. This means your old seven-year blanket policy is obsolete. You now need a nuanced retention schedule that links different data types to their specific business purposes.
For example, consider a customer support ticket. The data is collected to resolve a customer's issue. The retention period might be the time it takes to resolve the ticket, plus a reasonable period for quality assurance or follow-up—say, 90 days. Keeping it for seven years would be difficult to justify. You must document these retention periods and the reasoning behind them, as regulators can ask you to prove their necessity.
Building a Defensible Retention Schedule
Creating this schedule involves a few key steps. First, you need to conduct a data mapping exercise to understand what personal information you have, where it's stored, and why you collected it. Then, for each category of data, you must define a specific retention period based on business needs, legal obligations, and contractual requirements. This isn't just a legal exercise; it requires deep collaboration between legal, IT, and engineering teams to ensure policies are technically feasible to implement.
Essential Upgrades for Your Security Policies
CPRA mandates that businesses implement "reasonable security procedures and practices" to protect personal data. While "reasonable" is a flexible term, it's generally interpreted based on the sensitivity of the data. For engineers, this means we must move beyond basic perimeter security and focus on a defense-in-depth strategy that protects data at every stage.
This includes encrypting data both in transit (using TLS) and at rest (using technologies like AES-256 for databases and file systems). It also means implementing robust file access control. We need to enforce the principle of least privilege, ensuring that employees can only access the specific documents and data necessary to perform their job functions. Regular access reviews and automated logging are no longer optional—they're essential for demonstrating compliance.
The Critical Role of Secure Document Deletion
One of the most significant consumer rights under CPRA is the right to deletion. When a consumer requests that their data be deleted and it's no longer needed for a justified purpose, you must comply. Simply moving a file to the trash bin on a desktop is not sufficient.
Secure document deletion ensures that the data is permanently and irretrievably destroyed. For digital files, this can involve cryptographic erasure (deleting the encryption key, rendering the data unreadable) or using data-wiping algorithms that overwrite the data multiple times. The process needs to be logged and auditable. If a consumer asks for proof of deletion, or if a regulator investigates, you need a clear record showing that the request was fulfilled completely and securely.
Policy Comparison: Pre-CPRA vs. CPRA-Compliant
| Policy Area | Old Approach (Pre-CPRA) | New Approach (CPRA-Compliant) |
|---|---|---|
| Data Retention | Broad, blanket policies (e.g., "keep everything for 7 years"). | Purpose-based, minimized retention periods for each data category. |
| Data Collection | Collect data that might be useful in the future. | Collect only what is reasonably necessary for a disclosed purpose. |
| Security | Focus on perimeter security (firewalls, etc.). | Defense-in-depth, including encryption at rest and strong file access control. |
| Deletion | Deletion was often an afterthought, if done at all. | Mandatory, auditable, and secure document deletion processes are required. |
| Access Control | Often based on department or role without fine-grained control. | Based on the principle of least privilege; access is strictly need-to-know. |
| Documentation | Policies were often high-level and not regularly updated. | Detailed, documented justification for retention and security measures is required. |