
Have you ever questioned the authenticity of a digital document? A PDF contract could be altered, a digital certificate forged, or a critical report tampered with without leaving an obvious trace. For years, we've relied on centralized servers, passwords, and digital signatures, but these systems have inherent vulnerabilities that can be exploited.
This is a problem I've seen across industries—from legal to finance—where the integrity of a document is paramount. A single, unauthorized change can have massive consequences. This challenge is precisely where a new paradigm in data integrity is emerging, fundamentally changing how we approach the entire lifecycle of a document.
Table of Contents
What's Wrong with Traditional Document Security?
Traditional document management systems are typically centralized. This means all your files are stored on a single server or a cluster of servers controlled by one entity. While convenient, this creates a single point of failure. If that server is compromised, every document it holds is at risk of being stolen, altered, or deleted.
Furthermore, tracking the history of a document is often unreliable. Version control can be messy, and metadata showing who accessed or modified a file can be manipulated by a skilled attacker or a malicious insider. Proving that a specific version of a document is the original, untampered final version can be incredibly difficult, often relying on witness testimony or forensic analysis rather than cryptographic certainty.
How Blockchain Fundamentally Secures Documents

Blockchain introduces a completely different model. Instead of storing information in one place, it uses a distributed ledger—a database shared and synchronized across a network of computers. This decentralized nature is the foundation of its security. It's not about locking a document in a single digital vault; it's about creating an unbreakable public record of its existence and state.
The Power of Hashing and Timestamps
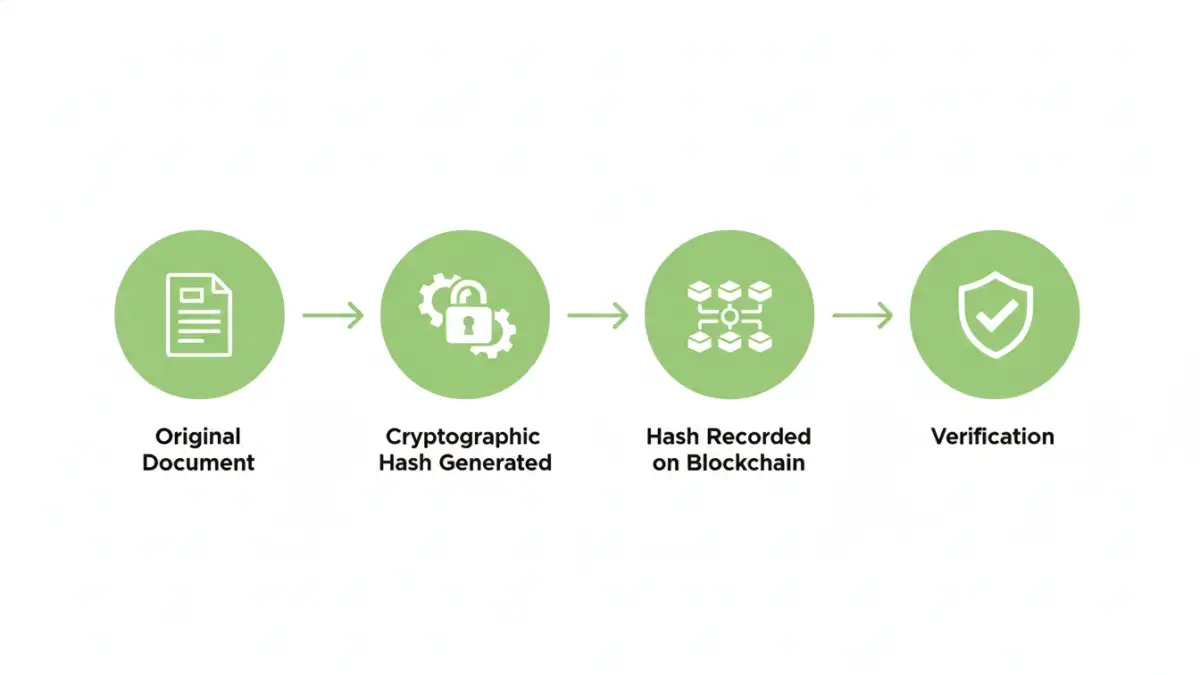
When you want to secure a document using blockchain, you don't upload the file itself. Instead, you run the document through a cryptographic hash function. This algorithm generates a unique, fixed-length string of characters (the 'hash') that acts as a digital fingerprint for that specific file. Even changing a single comma in the document will produce a completely different hash.
This hash is then recorded as a transaction on the blockchain, complete with a timestamp. Because the blockchain is append-only, this record cannot be changed or deleted. Anyone can later take the document, generate a new hash, and check if it matches the one recorded on the blockchain. If they match, the document is authentic and unaltered.
Decentralized File Verification and Immutability
The magic of the system lies in its decentralization. For a hacker to alter the record of your document's hash, they wouldn't just need to compromise one server; they'd have to gain control of over 50% of the computers in the entire network simultaneously—a practically impossible feat. This creates an immutable document ledger.
This process enables powerful decentralized file verification. You no longer need a central authority to vouch for a document's authenticity. The blockchain itself serves as the trusted, neutral third party. Anyone, anywhere, can verify the document's integrity against the public ledger without needing special permissions.
Practical Applications and Use Cases
The implications of this technology are vast and are already being explored in various sectors. The core benefit is preventing document fraud in high-stakes environments.
- Legal Contracts: Lawyers can hash a final contract and record it on the blockchain. This creates indisputable proof of the contract's content at a specific point in time, preventing disputes over altered clauses.
- Academic Credentials: Universities can issue digital diplomas and certificates with their hashes recorded on a blockchain. This allows employers to instantly verify a candidate's credentials without contacting the institution, eliminating diploma fraud.
- Supply Chain and Invoicing: Bills of lading, invoices, and customs documents can be secured on a blockchain. This ensures that all parties in a global supply chain are working with the same, untampered information, reducing delays and fraud.
- Intellectual Property: Creators can timestamp their work by hashing the file and recording it. This provides a clear, provable record of when their creation existed, which can be crucial in IP disputes.
Implementing Blockchain for Document Verification
You don't need to be a blockchain developer to start leveraging this technology. A growing number of platforms and services offer user-friendly interfaces for document notarization and verification. These services handle the technical complexities of creating hashes and interacting with the blockchain on your behalf.
For businesses, integrating smart contracts for PDFs and other documents is the next level. A smart contract is a self-executing contract with the terms of the agreement directly written into code. It could, for example, automatically release a payment once the blockchain verifies that a signed delivery receipt has been received and its hash matches the pre-agreed format. This automates trust and execution, making business processes more efficient and secure.
Comparison: Traditional vs. Blockchain Document Security
| Feature | Traditional Security (Centralized) | Blockchain Document Security (Decentralized) |
|---|---|---|
| Data Storage | On a central server or cloud provider. | A cryptographic hash is stored on a distributed network. |
| Point of Failure | Single point of failure; if the server is breached, data is at risk. | No single point of failure; robust against attacks. |
| Integrity Verification | Relies on access logs and internal controls, which can be altered. | Cryptographic proof via hashing; anyone can verify independently. |
| Immutability | Documents and records can be altered or deleted by administrators. | Records are permanent and cannot be changed or deleted. |
| Trust Model | Requires trust in the central authority managing the server. | Trustless; relies on cryptographic consensus of the network. |
| Best For | Internal collaboration and everyday file sharing. | High-value documents requiring permanent, provable integrity. |