
A colleague leaves the company, and you inherit a critical Excel automation tool they built. It works, but a small change is needed. The problem? The VBA project is locked, and the password is long gone. My developer brain immediately thinks of the technical solutions, but my professional experience raises a much more important question: just because you *can* get in, *should* you?
This scenario is more common than you'd think. While the internet is full of guides on the 'how,' very few discuss the 'why not.' Bypassing a password isn't just a technical challenge; it's an action with real legal and ethical consequences that can impact your job and your company's intellectual property.
Table of Contents
Distinguishing Recovery from Cracking
The first and most crucial step is to understand the intent behind your actions. The language we use matters because it reflects this intent. Are you performing a 'recovery' or are you 'cracking' a password? They are not the same thing, and the distinction is legally significant.
Legitimate Password Recovery
Password recovery is the process of regaining access to your own data or assets after forgetting or losing the credentials. If you are the original author of the VBA code or have been explicitly granted ownership and permission to modify it, then attempting to recover a forgotten password is a legitimate act. The intellectual property is yours (or your company's), and you are simply trying to access it.
Unauthorized Cracking
Cracking, on the other hand, implies gaining unauthorized access to a system or data that does not belong to you. If you are trying to view or modify VBA code in a file created by someone else, without their permission or the permission of the rightful owner (like your employer), you are entering a dangerous territory. This action can be seen as a breach of trust, a violation of policy, or even illegal, depending on the circumstances.
Intellectual Property and VBA Code

It's easy to forget, but the code tucked away inside an Excel macro is a form of intellectual property (IP), just like the text of a book or the design of a logo. This IP is protected by copyright law from the moment it is created. Bypassing a password to access it can be interpreted as copyright infringement.
Who Owns the Code?
The owner is typically the person who wrote it, unless it was created under a 'work for hire' agreement. If an employee writes VBA code as part of their job, the employer almost always owns the code. This is a key point in a corporate environment. The password was likely put there to protect the company's asset, not just to frustrate future developers. An unauthorized attempt to bypass that protection could be viewed as an attempt to misappropriate company property.
Corporate Governance and Internal Policies
Before you even consider a technical solution, your first stop should be your company's IT and legal departments. Most organizations have a clear corporate vba security policy or an acceptable use policy that governs software, data, and IP.
Review Your Employment Agreement
Your employment contract and employee handbook likely contain clauses about confidentiality, intellectual property, and authorized use of company assets. Violating these clauses by cracking a password on a company file could lead to serious disciplinary action, including termination. The argument that you were 'just trying to get the job done' often doesn't hold up when you've willfully circumvented a security measure.
The Proper Chain of Command
In the scenario of an inherited project, the correct procedure is to go through official channels. Document the business need for the code modification and request access from your manager or the IT department. This creates a paper trail proving you acted with authorization. If they approve, the responsibility shifts from you to the company. This protects you and ensures the company maintains control over its assets.
Justifiable Scenarios for Access
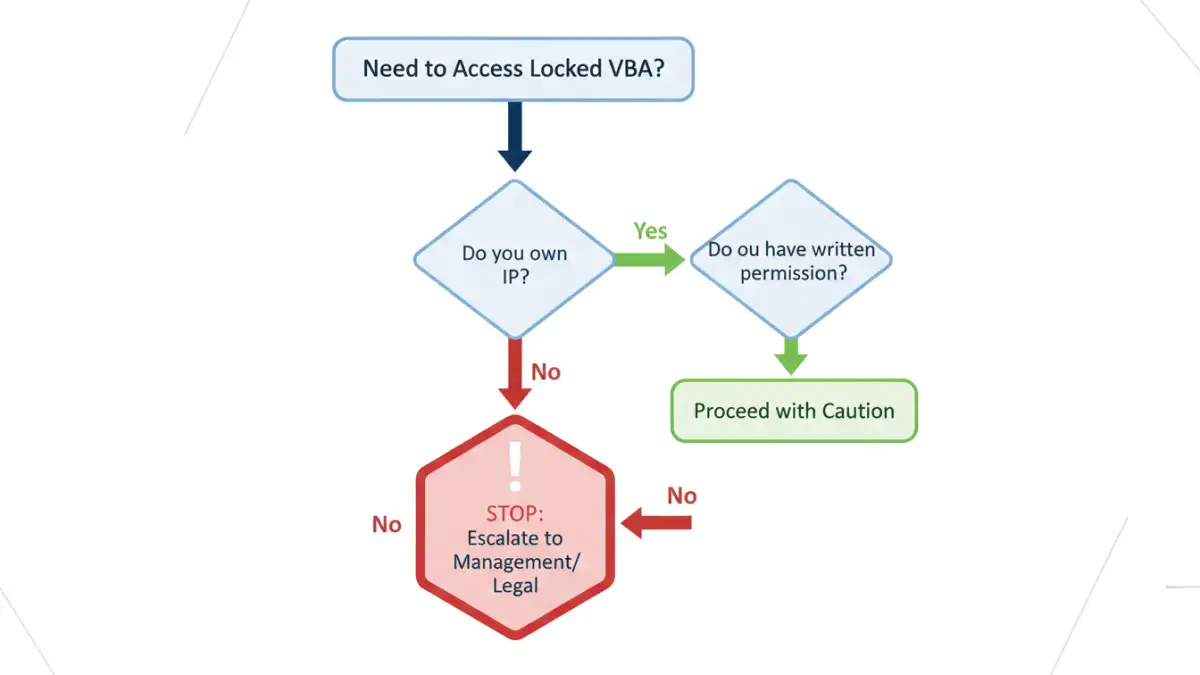
Of course, there are situations where bypassing a password is the right and necessary thing to do. The key factor in all these cases is authorization. You must have the explicit, documented permission of the code's legal owner.
Authorized Project Takeover
When a developer leaves, a company must maintain its business processes. If you are officially assigned to take over a project, and management or IT authorizes you to gain access to a locked VBA project, you are in the clear. Your goal is to act as an agent of the owner (the company) to maintain their property.
Security Audits
A less common but equally valid scenario is a security audit. An IT security professional might be tasked with testing the strength of a vba file password and other security measures. In this case, the 'cracking' is not only authorized but is the entire point of the exercise. This is always done with high-level executive approval and within a strictly defined scope.
Legal & Ethical Framework for VBA Access
| Scenario | Legal Risk | Ethical Stance | Recommended Action |
|---|---|---|---|
| Forgotten password on your own personal project | Low | Acceptable | Proceed with recovery methods. You are accessing your own IP. |
| Inherited a file from a former colleague | High | Questionable | Do not proceed. Escalate to management and IT for official authorization. |
| Curiosity about a third-party tool's code | Very High | Unethical | Do not attempt. This is likely copyright infringement and a breach of the tool's license agreement. |
| Need to fix a bug in a legacy corporate tool | High | Questionable | Document the business need and request official permission from the asset owner (your company). |
| Performing an authorized security audit | Low | Ethical | Proceed within the defined scope of the audit with documented executive approval. |