
I once inherited a complex Excel workbook from a developer who had left the company. The workbook was critical for a reporting process, but the VBA project was locked, and nobody knew the password. This situation immediately raised a thorny question: we owned the file, but was it right—or even legal—to break into the code he wrote? This isn't just a technical challenge; it's a legal and ethical minefield.
While technically possible to bypass a password, doing so without proper authorization can lead to significant consequences. It touches upon copyright law, intellectual property rights, and professional ethics. Before you even search for a tool to do the job, it's crucial to understand the framework you're operating within.
Table of Contents
Why Are VBA Projects Password Protected?
Understanding the 'why' behind VBA protection is the first step. Developers and organizations lock VBA projects for several valid reasons, and respecting these intentions is key. It's rarely about being difficult; it's about control and stability.
The primary reason is to protect intellectual property. The VBA code within a workbook can represent hundreds of hours of development work, containing proprietary algorithms and business logic. A password acts as a digital lock, safeguarding this valuable asset from unauthorized copying, distribution, or reverse engineering.
Another common reason is to prevent accidental or unauthorized modifications. In a collaborative environment, an inexperienced user could inadvertently alter a critical function, causing data corruption or breaking the entire application. Locking the project ensures that only qualified developers can make changes, maintaining the integrity and reliability of the tool.
Navigating the Legal Landscape of VBA Code
The moment you attempt to circumvent a digital lock, you enter a complex legal area. The code written by a developer is generally protected by copyright law from the moment it is created. This means the author has exclusive rights to reproduce, distribute, and modify their work.
Copyright and Intellectual Property VBA Code
If you are not the author of the code, and you don't have explicit permission from the copyright holder (the author or their employer), accessing it could be considered copyright infringement. In a corporate setting, the code an employee writes as part of their job typically belongs to the company under a 'work for hire' doctrine. However, this doesn't give every employee free rein to access it; authorization is still required.
The Digital Millennium Copyright Act (DMCA)
In the United States, the DMCA makes it illegal to circumvent technological measures that control access to copyrighted works. Bypassing a VBA password could be interpreted as a violation of the DMCA. While the law is complex and has exceptions, its existence underscores the seriousness of bypassing digital locks. The answer to 'is it legal to crack vba' depends heavily on ownership, authorization, and intent.
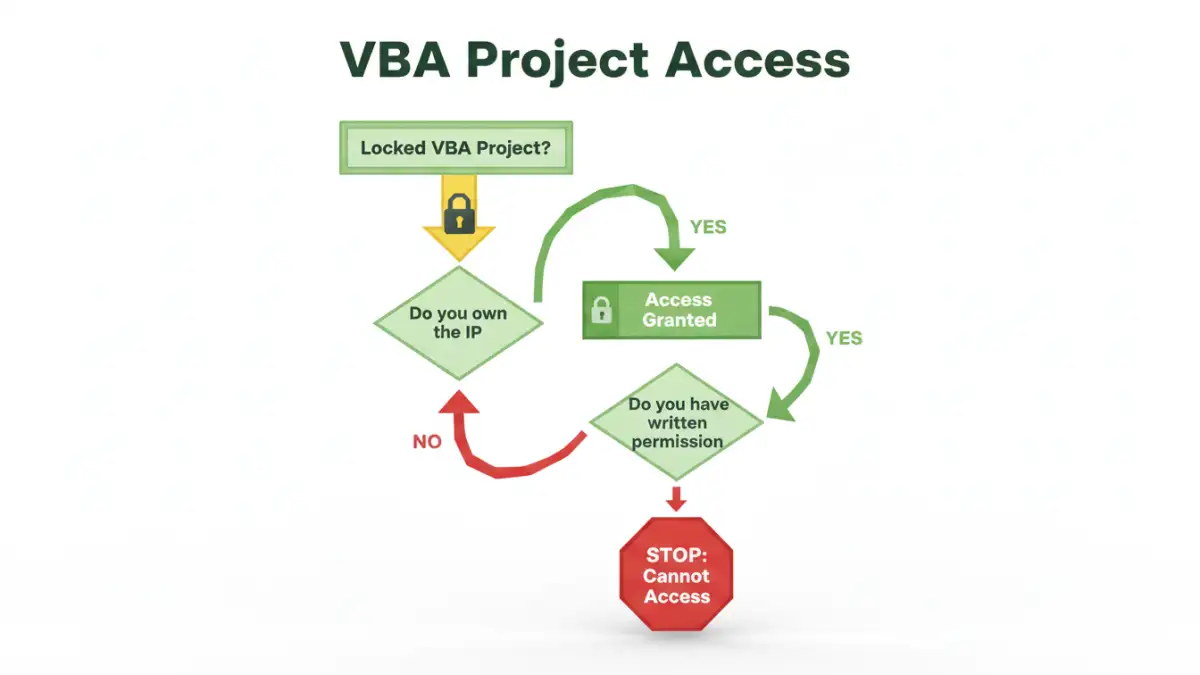
When Is Bypassing a Password Legitimate?
Of course, there are situations where accessing a locked project is necessary and perfectly legal. The key differentiator in all these cases is authorization and ownership. You must have the legal right to access the code.
The most common legitimate scenario is when you are the original author and have simply forgotten the password. In this case, you are the copyright holder and are merely trying to access your own work. Another frequent case is employee turnover. If an employee leaves, the company (as the owner of the intellectual property) has the right to access and maintain its assets. In this situation, a manager or IT department can authorize the action.
Finally, if you are a consultant or developer hired to modify or debug an existing application, the client should provide you with the password. If they've lost it, they can provide written authorization for you to recover access on their behalf. Documenting this permission is crucial to protect yourself.
Ethical Considerations Beyond the Law
Legality isn't the only factor. As professionals, we are also bound by a code of ethics. The `vba password ethics` question is about professional conduct and respect for the work of others. Attempting to access a colleague's locked code without their knowledge, even if for a seemingly good reason, can be a breach of trust.
It's always best to approach the original author first if they are available. They may have valid reasons for protecting the code that you're not aware of. Bypassing their protection can lead to a toxic work environment and damage professional relationships. It also carries the risk of introducing new bugs if you misunderstand the original logic.
Corporate Policies and Best Practices
Most mature organizations have a `corporate vba security policy` or broader IT guidelines that govern access to digital assets. These policies should be your primary guide. They will outline the proper channels for requesting access to locked files and the documentation required.
Establishing Clear Guidelines
If your organization doesn't have a clear policy, this is an opportunity to advocate for one. A good policy should include a password escrow system, where critical passwords are stored securely with a trusted party like the IT department. This ensures business continuity without creating a free-for-all.
The policy should also clearly state who owns the code created by employees and the protocol for transferring ownership when an employee leaves. Having these rules in place prevents ambiguity and protects both the company and its developers. A well-defined policy on handling a locked vba file password can save countless headaches and legal risks down the line.
Scenario Legality and Ethics Comparison
| Scenario | Legality | Ethics | Recommended Action |
|---|---|---|---|
| You forgot the password to your own code. | Legal | Ethical | Proceed with recovery methods. You own the IP. |
| A former employee left, and the company owns the file. | Legal (with authorization) | Ethical | Get documented approval from management or IT before proceeding. |
| You need to access a colleague's locked code. | Potentially Illegal | Unethical without permission | Ask your colleague for the password and explain why you need access. |
| Accessing third-party software you purchased. | Illegal (DMCA violation) | Unethical | Do not attempt. This is a clear violation of the software license. |
| A client lost the password to their own file. | Legal (with authorization) | Ethical | Obtain written permission from the client before attempting recovery. |