
The sudden, massive shift to remote work wasn't just a change in location; it was a fundamental break in the corporate security model. For years, we built digital fortresses, assuming that the most sensitive data would remain within the castle walls of the corporate network. When millions of home offices became the new cubicles, that fortress wall crumbled, exposing data to a host of new threats on open networks.
This new reality has created an urgent and rapidly growing need for solutions that can protect data in transit, regardless of where it's coming from or going. It’s no longer enough to secure the destination; we must secure the journey itself. This is the core challenge that remote work has presented to IT and security teams globally.
Table of Contents
The Old Model: A Fortress with Suddenly Open Gates
In a traditional office environment, data security was comparatively straightforward. Most critical operations happened within a controlled local area network (LAN). As an engineer, I often worked with on-premise servers where access was strictly managed through firewalls, VPNs, and physical security. Sharing a large, sensitive file often meant simply dropping it onto a shared network drive.
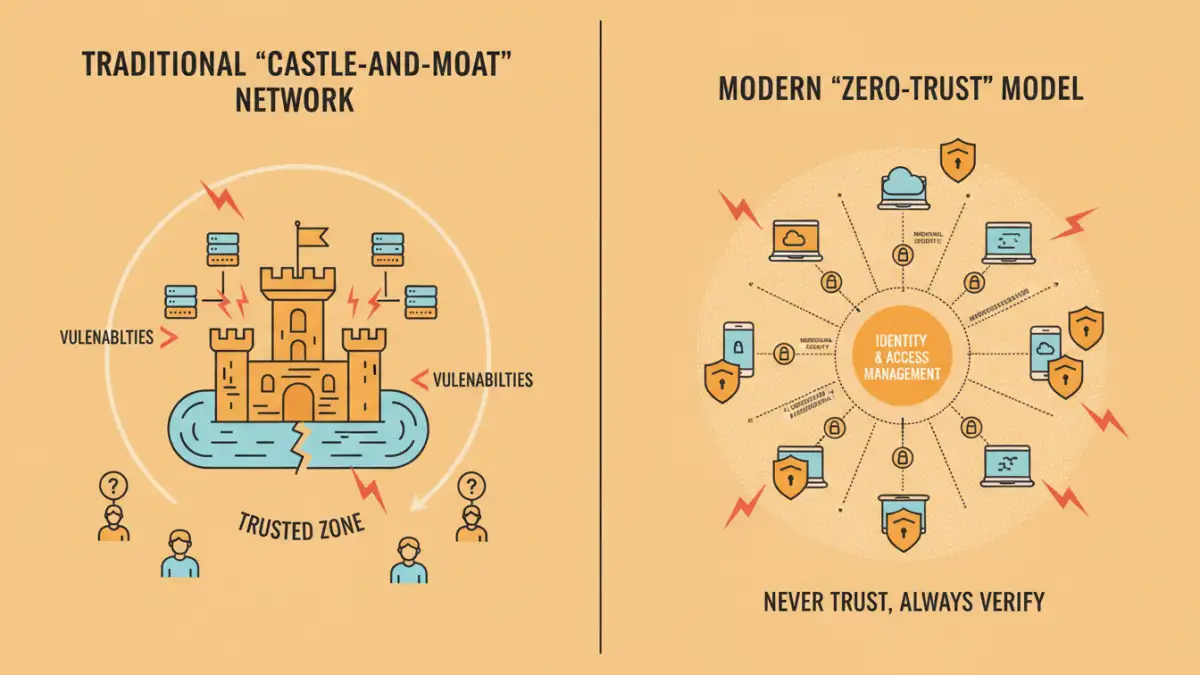
This "castle-and-moat" approach assumes that threats are primarily external. Once an employee was authenticated and inside the network, they were generally trusted. The perimeter was everything. Remote work completely upended this paradigm, effectively giving every employee a key to a side gate without the controlled environment of the main drawbridge.
The Illusion of the Secure Perimeter
The reliance on a secure perimeter created a false sense of security. We focused on hardening the network edge, but the transition to WFH meant the edge was now in millions of homes, on countless unmanaged networks. The corporate VPN, once a tool for traveling executives, became a bottleneck and a single point of failure when stressed by the entire workforce.
Remote Work's Direct Impact on Data Vulnerabilities
The move to distributed teams introduced several immediate security challenges that legacy systems were not equipped to handle. These vulnerabilities are the primary catalysts for the changing landscape of data transfer security.
Unsecured Networks and Personal Devices
One of the biggest shifts was the move from corporate-managed networks to consumer-grade home Wi-Fi. These networks often lack robust security configurations, making them susceptible to man-in-the-middle attacks. Furthermore, many employees began using personal laptops and mobile devices for work, a phenomenon known as Shadow IT. These devices often lack enterprise-grade security software, patches, and configurations, creating a massive new attack surface for malicious actors.
When an employee downloads a sensitive financial report to their personal laptop over an unsecured coffee shop Wi-Fi, the data is exposed at multiple points. This is a common scenario that highlights the urgent need for end-to-end encryption for all file transfers, ensuring the data is unreadable even if intercepted.
Key Drivers Fueling Encrypted File Sharing Demand
The vulnerabilities created by remote work have directly translated into a surge in demand for more sophisticated data protection. Several key factors are pushing organizations to invest heavily in secure file transfer solutions.
Regulatory Compliance and Governance
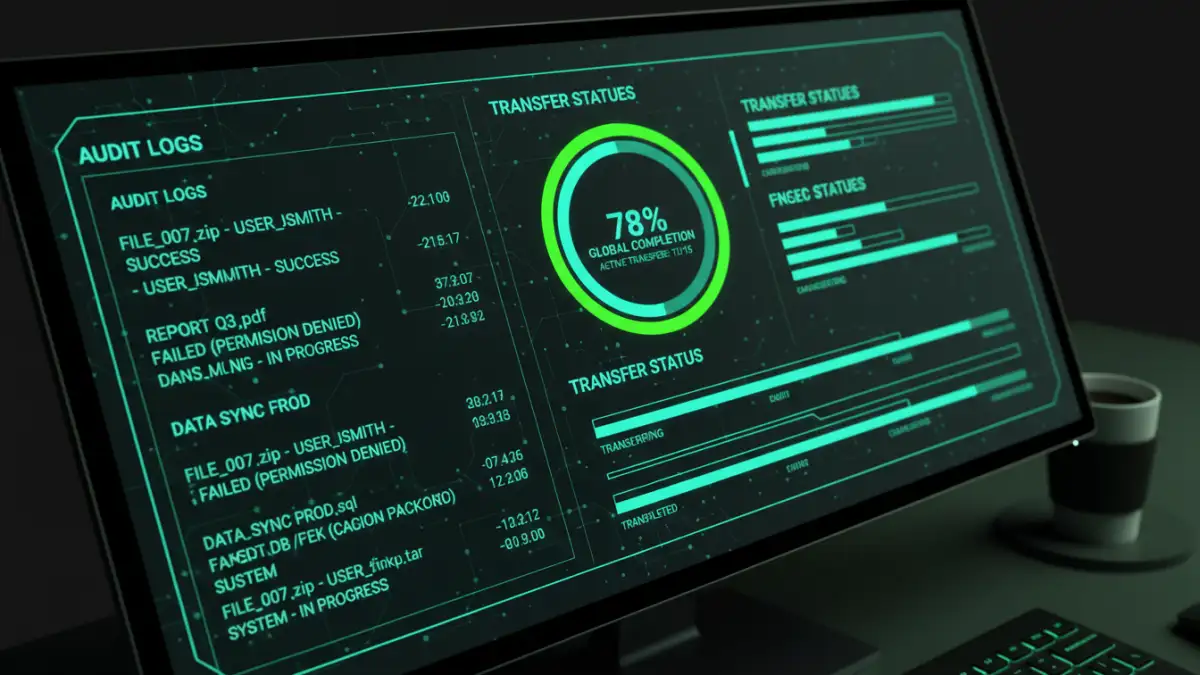
Regulations like GDPR, HIPAA, and CCPA don't offer exceptions for remote work. Organizations are legally obligated to protect sensitive personal and health information, regardless of where their employees are located. Failing to secure data in transit can lead to massive fines and reputational damage. Modern secure transfer solutions provide detailed audit trails, logging who accessed, sent, and received files, which is critical for demonstrating compliance.
The Rising Threat of Ransomware
Ransomware attacks have skyrocketed, often exploiting weak points in data sharing practices. An employee accidentally downloading a malicious file from an insecure source can compromise an entire network. Secure file transfer platforms mitigate this risk by scanning files for malware before they are delivered and by replacing risky email attachments with secure links, preventing malicious payloads from ever reaching an employee's inbox directly.
Evolving Technologies and Market Trends
In response to these challenges, the technology landscape is adapting quickly. The growth in the **secure file transfer market** is not just about quantity; it's about a qualitative shift towards more intelligent, automated, and integrated solutions.
The Rise of Managed File Transfer (MFT)
While protocols like SFTP and FTPS have been around for years, Managed File Transfer (MFT) solutions are gaining prominence. MFT provides a centralized platform for managing, automating, and securing all file transfer activities. It offers features like automated workflows, detailed reporting, end-to-end encryption, and integration with other enterprise systems. For a distributed workforce, MFT provides the visibility and control that was lost when employees left the office.
Adoption of Zero-Trust Architecture
A core principle gaining traction is Zero Trust, which operates on the philosophy of "never trust, always verify." In the context of file sharing, this means that every request to access or transfer a file is authenticated and authorized, regardless of whether the user is inside or outside the old corporate network. This model is perfectly suited for remote work, as it treats every connection and endpoint as potentially insecure, applying rigorous security checks to all data movement.
Comparison of Secure File Transfer Solutions for Remote Teams
| Solution Type | Key Features | Best For | Security Level |
|---|---|---|---|
| Managed File Transfer (MFT) | Automation, detailed audit trails, centralized control, advanced encryption. | Enterprises with high-volume, automated, or compliance-driven transfers. | Very High |
| Secure Email Gateways | Attachment scanning, data loss prevention (DLP), link-based secure delivery. | Organizations looking to secure existing email workflows against malware and data leaks. | High |
| Enterprise File Sync & Share (EFSS) | Cloud-based collaboration, version control, granular permissions. | Teams needing real-time collaboration on documents with built-in security controls. | High |
| Basic SFTP/FTPS | Encrypted point-to-point file transfer protocol. | Simple, ad-hoc technical file transfers where automation and visibility are not required. | Moderate |