
Just last week, a marketing team I support needed to send a customer dataset to a partner agency in the United States. A few years ago, this would have been a straightforward task. Today, it involves a careful review of legal and technical frameworks to ensure we don't run afoul of international data transfer laws. The era of simply attaching a file to an email and hitting 'send' is long over for businesses operating globally.
The ground is constantly shifting beneath our feet. The invalidation of the Privacy Shield framework created significant uncertainty, and while new agreements are in place, the core principles of data protection have become stricter. As engineers, we're on the front lines, responsible for building the systems that either comply with these rules or expose our companies to massive risk.
Table of Contents
The Shifting Landscape of Data Transfer
The conversation around international data sharing changed dramatically with the introduction of the EU's General Data Protection Regulation (GDPR). It established a high bar for data privacy, and its influence extends far beyond Europe's borders. Any organization handling the data of EU residents must comply, regardless of where the company is located.
A key challenge has been the mechanism for legally transferring data out of the European Economic Area (EEA). The landmark 'Schrems II' court ruling in 2020 invalidated the EU-U.S. Privacy Shield, a popular framework many companies relied on. This decision was based on concerns that U.S. surveillance laws didn't provide adequate protection for EU citizens' data, creating an immediate compliance gap for thousands of businesses.
Understanding GDPR Adequacy
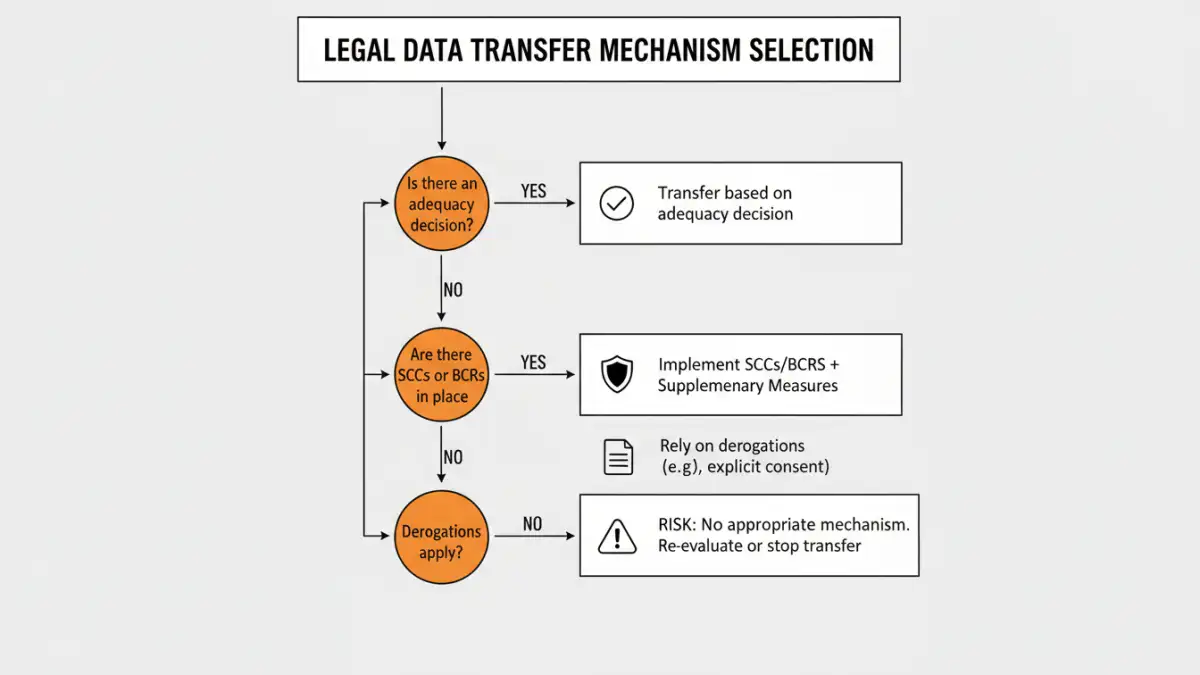
At the heart of these challenges is the concept of 'adequacy.' Under GDPR, personal data can flow freely from the EEA to a third country if the European Commission has decided that the country provides an 'adequate' level of data protection. This means the country's domestic laws are deemed comparable to those within the EU.
When a country lacks an adequacy decision, organizations must use alternative transfer mechanisms. These include Standard Contractual Clauses (SCCs) or Binding Corporate Rules (BCRs), which are legally binding agreements that impose EU-level data protection standards on the data recipient. Implementing these requires careful legal and technical diligence.
Core Principles for Compliant Sharing

Regardless of the specific legal mechanism you use, adhering to core data protection principles is non-negotiable. Building these into your systems from the ground up is the most effective way to manage compliance and reduce risk. These principles are the foundation of most modern data transfer laws.
First is data minimization. Only collect and transfer the data that is absolutely necessary for a specific, legitimate purpose. I've seen projects where entire user databases were synced when only a few fields were needed. This is a recipe for disaster. Second is purpose limitation; data transferred for one reason cannot be repurposed for another without a valid legal basis. Finally, robust security measures are critical. This goes beyond simple passwords.
Implementing Essential Technical Safeguards
From an engineering perspective, 'security' means tangible controls. All international document sharing must employ encryption both in-transit (using protocols like TLS 1.2+) and at-rest (encrypting data on servers and databases). This ensures that even if data is intercepted, it remains unreadable.
Access control is equally important. Use role-based access control (RBAC) to ensure that only authorized individuals can view or modify sensitive data. Implement strong audit logging to track who accessed what data and when. These logs are invaluable for demonstrating compliance and investigating potential breaches.
Navigating the Privacy Shield Replacement
After a period of uncertainty, the EU-U.S. Data Privacy Framework (DPF) was established as a successor to the Privacy Shield. This new framework aims to address the concerns raised by the Schrems II ruling by introducing new safeguards regarding U.S. intelligence agencies' access to data and establishing a new redress mechanism for EU individuals.
U.S. companies can self-certify their commitment to the DPF's principles, which allows them to receive personal data from the EU without needing other transfer mechanisms like SCCs. However, it's not a silver bullet. It's crucial to verify that any U.S.-based service provider you use for international document sharing is certified under the new framework. This requires due diligence, not just taking a vendor's word for it.
Practical Steps for Engineering Teams
So, what does this mean for your day-to-day work? First, map your data flows. You can't protect what you don't know exists. Document where data originates, where it's stored, and where it's transferred, paying special attention to cross-border movements. This is a foundational step in any compliance program.
Second, collaborate closely with your legal and compliance teams. As an engineer, your role is to understand the technical requirements and implement them, but interpreting complex data transfer laws is a specialized skill. This partnership is essential for building systems that are both functional and compliant. Finally, choose your tools wisely. Opt for file-sharing platforms and cloud providers that offer robust security features and are transparent about their compliance with global regulations. Prioritize services that allow you to control data residency and provide detailed audit trails. Adhering to secure file sharing regulations is a team effort, and having the right tools makes it manageable.
Comparison of Data Transfer Mechanisms
| Mechanism | Description | Best For | Key Consideration |
|---|---|---|---|
| Adequacy Decision | Data flows freely to countries the EU deems to have adequate data protection laws. | Transfers to countries like the UK, Japan, or Canada. | Simplest method, but only applies to a limited list of countries. |
| EU-U.S. DPF | A certification framework for U.S. companies to receive EU data. | Transfers to certified U.S.-based organizations. | Requires verifying the recipient's active certification. |
| Standard Contractual Clauses (SCCs) | Legally binding contracts that enforce EU data protection standards. | Transfers to countries without an adequacy decision. | Requires a Transfer Impact Assessment (TIA) to be conducted. |
| Binding Corporate Rules (BCRs) | Internal rules for data transfers within a multinational corporate group. | Large, multinational corporations with frequent intra-company transfers. | Requires approval from a data protection authority; complex to set up. |