The decision to expose wrongdoing is monumental, but the technical execution of sharing that information can be just as critical. A single digital misstep can compromise your identity and undermine the very truth you're trying to bring to light. This isn't just about sending an email; it's about managing a complex chain of data security where every link must hold.
As an engineer who has built and audited secure systems, I've seen how easily data can betray its source. The path to responsible disclosure requires a deliberate and informed approach to technology. It's about creating a protective layer between you and the information you're compelled to share, ensuring the focus remains on the disclosure, not the discloser.
Table of Contents
The Whistleblower's Dilemma: Security vs. Impact
The core challenge for any whistleblower is balancing the need for absolute secrecy with the goal of making a real-world impact. Exposing information effectively often means getting it to journalists or organizations who can verify and publicize it. However, every point of contact is a potential point of failure for your anonymity.
This is where understanding the tools of the trade becomes non-negotiable. It's not about being a hacker; it's about practicing meticulous digital hygiene. The goal is to sever the connection between your real-world identity and the digital package of information you are transmitting. This requires thinking several steps ahead about how data travels and what invisible fingerprints it might carry.
Foundational Security Measures Before You Share
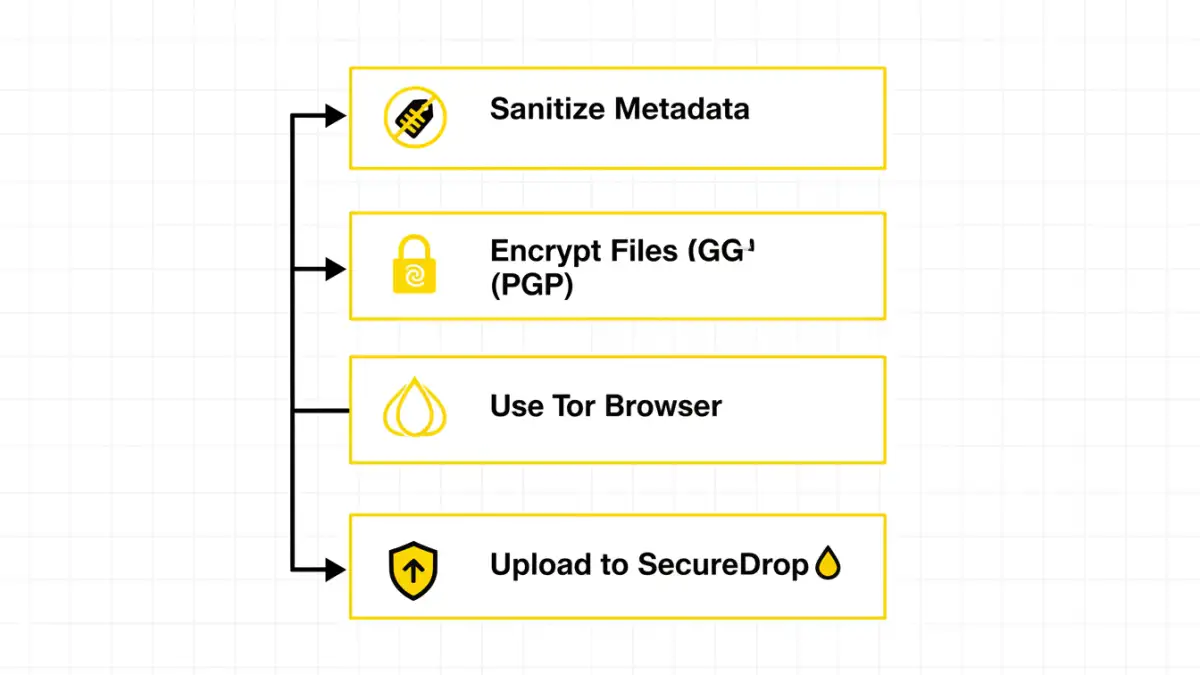
Before you even think about sending a file, you must secure your environment and the data itself. These foundational steps are the most critical part of the entire process. Skipping them renders even the most advanced sharing methods useless.
Anonymizing Your Digital Footprint
Your Internet Protocol (IP) address is a direct link to your physical location and identity. Never use your home or work network for any activity related to whistleblowing. Instead, use a combination of tools to obscure your origin. The Tor Browser is the gold standard, routing your traffic through a series of volunteer-operated servers to anonymize your connection. While a reputable VPN adds a layer of encryption, Tor is specifically designed for anonymity and is essential for this kind of sensitive work.
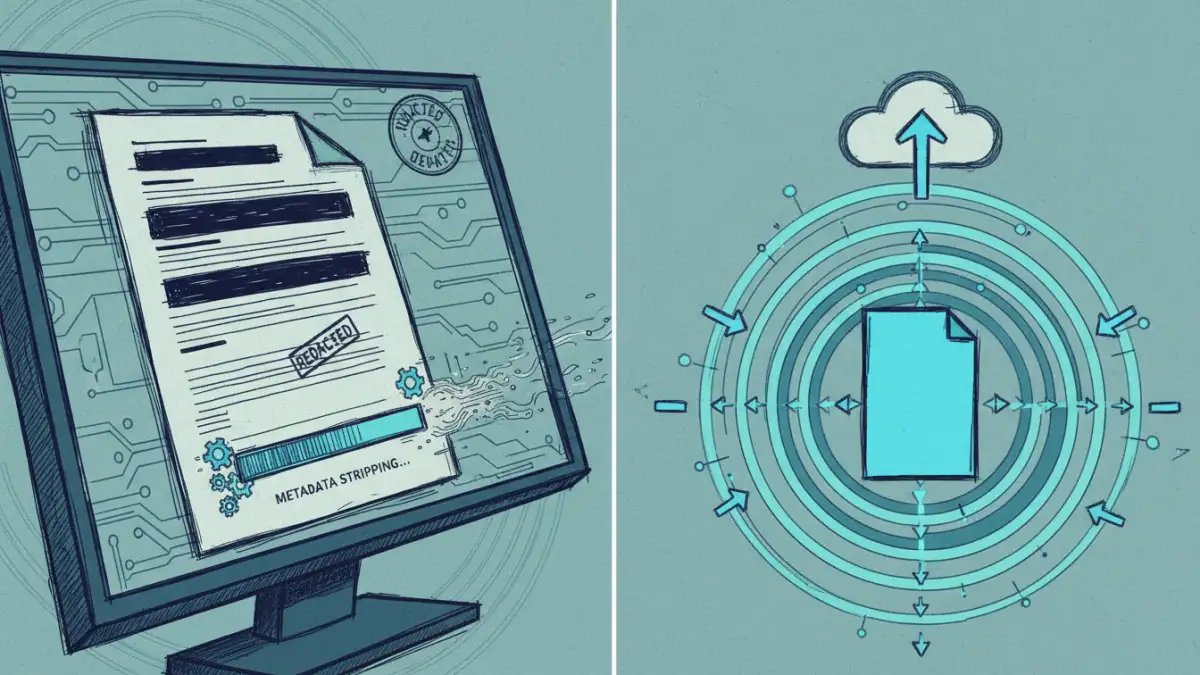
Sanitizing Your Documents
Documents are rarely just the text and images you see. They contain a wealth of hidden metadata: author's name, company details, creation dates, edit history, and even GPS coordinates from the device that created the file. This information is a direct trail back to you. Before sharing, you must scrub this data. Tools exist for metadata removal, but a simple, effective method is to convert the document to a plain text file or print it and rescan it on a public machine, creating a 'clean' image with no digital history.
Core Methods for Anonymous File Sharing
Once your environment is secure and your files are clean, you need a channel to transmit them. Sending a file as an attachment from a standard email account is out of the question. You need platforms built specifically for encrypted communication and anonymous submissions.
Using Secure Submission Systems
Many major journalistic organizations have adopted SecureDrop, an open-source whistleblower submission system. It uses the Tor network to create a highly anonymous channel between a source and a media outlet. When you connect to a SecureDrop instance, you are given a unique, randomized codename. This is your only identifier, allowing you to submit documents and communicate with journalists without ever revealing your identity. This is a powerful tool for ethical data leaks.
The process is entirely managed through the Tor Browser, ensuring your location is masked. The documents are encrypted on the organization's servers, accessible only by a limited number of journalists with special security keys. This creates a robust buffer, protecting both the source and the recipient.
Encrypted Communication Channels
For initial, cautious contact or for sharing smaller pieces of information, end-to-end encrypted messaging apps like Signal can be useful. The key is to use them on a device that is not associated with your personal identity—a 'burner' phone purchased with cash and used only on public Wi-Fi. While Signal encrypts the content of your messages, it still requires a phone number, which can be a link to your identity if not managed carefully.
Similarly, encrypted email providers like ProtonMail offer end-to-end encryption if both the sender and receiver are using the service. However, email headers can still contain revealing information. These tools are part of a broader strategy but are generally less anonymous than a dedicated system like SecureDrop for the actual act of secure document sharing.
Ethical Frameworks and Legal Realities
Technology is only one part of the equation. Whistleblower protection laws vary dramatically by country, industry, and the type of information being disclosed. Before taking any action, it is highly advisable to seek guidance from organizations that specialize in this area, such as the Electronic Frontier Foundation (EFF), the Government Accountability Project, or the National Whistleblower Center.
These groups can provide context on the legal risks and help you understand the line between protected public interest disclosure and unlawful data theft. The goal is to ensure your actions are ethically sound and legally defensible, which is a complex task. Your technical security measures are designed to give you the space and safety to navigate these legal and ethical waters carefully.
Whistleblower Communication Method Comparison
| Method | Anonymity Level | Primary Use Case | Key Limitation |
|---|---|---|---|
| SecureDrop | Very High | Submitting documents to journalists | Requires the recipient organization to have it installed. |
| Signal (on a burner phone) | High | Encrypted text/voice communication | Phone number can be a point of compromise if not managed. |
| ProtonMail (P2P) | Moderate to High | End-to-end encrypted email | Email metadata can still leak some information. |
| Public USB Drop | High (if executed perfectly) | Physical transfer of data | High personal risk during the physical drop-off. |
| Standard Email/Cloud | None | Not recommended for any sensitive task | Easily traceable, not encrypted by default, logs everything. |