
A client once asked me what happens to their encrypted data backups after their contract ends. It's a simple question with a complex ethical answer that goes far beyond just hitting a 'delete' button. Encryption is a powerful tool for protecting data, but it also creates a unique set of responsibilities. Simply locking data away isn't enough; we must also have a clear, ethical plan for its entire lifecycle, especially its end.
This isn't just a technical problem—it's a matter of trust. When we encrypt a user's data, we make a promise to protect it. That promise extends to how we handle it when it's no longer needed. Holding onto encrypted data indefinitely creates a latent risk, while improper deletion can be just as damaging as a data breach.
Table of Contents
The Dual Responsibility: To Protect and To Forget
As engineers and data custodians, we walk a fine line. On one hand, we have a duty to protect information through robust encrypted file storage. This means ensuring confidentiality, integrity, and availability. We build systems with strong ciphers and key management protocols to prevent unauthorized access.
On the other hand, we have an equally important duty to 'forget' data when it's no longer required. This is the core of many privacy regulations like GDPR's 'Right to be Forgotten.' Holding onto encrypted data indefinitely, even if it's 'secure,' is a liability. Keys can be compromised, algorithms can be broken, and the context of the data can change, making its continued existence a risk to privacy.
The Illusion of Deletion
A standard file deletion on most operating systems doesn't actually erase the data. It simply marks the space on the disk as available for overwriting. With encrypted files, this presents a unique problem. The encrypted file might linger for years, and if the encryption key is ever compromised, that 'deleted' data is suddenly vulnerable again. True deletion requires a more deliberate approach.
Key Ethical Principles in Data Lifecycle Management
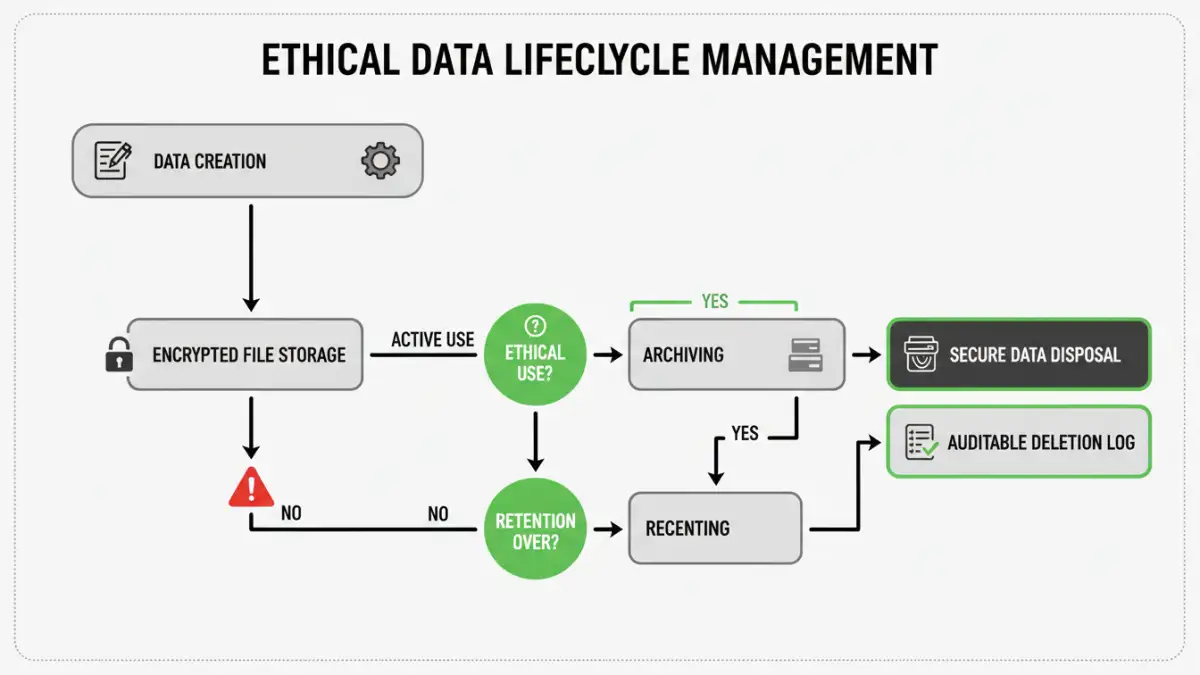
To navigate this landscape, we rely on a few core principles. These aren't just legal checkboxes; they are the foundation of trustworthy technology. A strong policy on document retention ethics is built upon these ideas.
Data Minimization
The principle of data minimization is simple: don't collect or store data you don't absolutely need. For the data you do need, define a clear purpose and a finite retention period. Encrypting a massive trove of unnecessary data doesn't reduce the ethical burden; it just hides it behind a password. Ask yourself: why are we keeping this, and for how long?
Purpose Limitation and Storage Limitation
Data should only be used for the specific purpose for which it was collected. Once that purpose is fulfilled, its retention period should expire. For instance, customer support chat logs might need to be retained for 60 days for quality assurance but should be scheduled for secure deletion after that. This requires automated systems that can enforce these policies reliably, a key part of modern data lifecycle management.
Technical Challenges in Secure Data Disposal
Putting these ethical principles into practice involves overcoming significant technical hurdles. Secure data disposal for encrypted files is more complex than it sounds, especially in distributed cloud environments.
One of the most effective methods is cryptographic-shredding (or crypto-shredding). Instead of trying to overwrite the data itself—which is difficult in complex storage systems—we securely destroy the encryption key. Without the key, the encrypted data is rendered permanently inaccessible and becomes meaningless gibberish. This is often the most practical way to enforce the 'right to be forgotten' in large-scale systems.
Verifying Deletion
How do you prove a negative? Verifying that data has been truly and permanently deleted is a major challenge. This is where detailed audit logs become critical. We need to log the deletion event, the method used (e.g., crypto-shredding), the timestamp, and the authority for the deletion. This creates a chain of custody that demonstrates compliance and responsible data stewardship, which is essential for privacy compliance.
Building an Ethical Retention and Deletion Policy
A robust policy is the bridge between ethical principles and technical implementation. It shouldn't be a document that just sits on a shelf; it must be an active part of your system's architecture.
Your policy should clearly define data categories, specify retention periods for each, and outline the exact procedures for secure deletion. For example, 'User-generated content is retained for the life of the account and crypto-shredded 30 days after account closure.' It should also name the individuals or roles responsible for overseeing the policy.
Ultimately, the ethics of handling encrypted data come down to intent and execution. We must design systems that not only protect data with strong encryption but also respect the user's right to privacy by ensuring that data can be permanently and verifiably forgotten when the time comes. This builds trust and ensures our technology serves people responsibly.
Data Deletion Method Comparison
| Deletion Method | How It Works | Pros | Cons |
|---|---|---|---|
| Standard Deletion | Marks file space as available for overwriting. | Fast; requires no special tools. | Data is easily recoverable until overwritten. |
| Secure Overwriting | Overwrites the data's physical location with random patterns. | Makes recovery very difficult. | Slow; can cause wear on SSDs; difficult in cloud/virtualized systems. |
| Cryptographic Shredding | Destroys the encryption key, rendering the ciphertext useless. | Extremely fast; ideal for cloud storage and large datasets. | Requires a robust key management system from the start. |
| Physical Destruction | Shredding, degaussing, or incinerating the storage media. | The most secure method of disposal. | Impractical for cloud environments; expensive. |