
A few years ago, a client came to us with a challenge. They were building a platform for high-stakes legal agreements, and while they had robust encryption and multi-factor authentication, a critical vulnerability remained. How could they be certain the person accessing a sensitive contract was the legitimate user in real-time, and not just someone using a stolen photo or a pre-recorded video to fool a simple facial recognition scan? This is where the conversation shifted from authentication to verification of presence.
That project was my first deep dive into the world of liveness detection. It’s a technology that fundamentally changes how we think about security by asking a simple but powerful question: Is there a living, breathing person in front of the camera right now? It’s the crucial next step in protecting our most sensitive digital assets from increasingly sophisticated fraud.
Table of Contents
What Is Liveness Detection and Why Does It Matter?
At its core, liveness detection is a form of artificial intelligence that determines if a biometric sample is being captured from a live person who is physically present. It’s designed specifically to combat spoofing attacks, also known as presentation attacks, where a fraudster tries to trick a system with a fake artifact.
Traditional security measures are good at verifying credentials, but they can't confirm the user's liveness. This is a critical distinction in an era of deepfakes and digital impersonation. True anti spoofing document security requires more than just knowing a password; it requires knowing the user is genuinely there.
Beyond Passwords and 2FA
Passwords can be stolen, and authenticator app codes can be phished. These methods verify what a user knows (a password) or what they have (a phone). A simple facial recognition scan verifies what a user *is*, but without a liveness check, it can be easily fooled. A high-resolution photo or video of the legitimate user can often bypass basic systems.
Liveness detection adds that crucial, missing layer. It analyzes subtle cues that are difficult or impossible to fake, ensuring the identity check is happening with a real person and not a digital or physical replica. This moves security from simple authentication to true identity verification.
The Spoofing Threat
Spoofing attacks are a major threat to systems that rely on facial biometrics. These attacks can range from surprisingly simple to highly sophisticated:
- 2D Attacks: Using printed photos, or displaying a photo or video on a digital screen.
- 3D Attacks: Employing realistic masks made of silicone or latex to mimic a person's face.
- Deepfakes & Replay Attacks: Using AI-generated videos or replaying previously recorded authentication sessions.
A robust biometric liveness check is the primary defense against these presentation attacks, making it an essential component for any high-security document management system.
How Liveness Detection Works: The Technology Explained
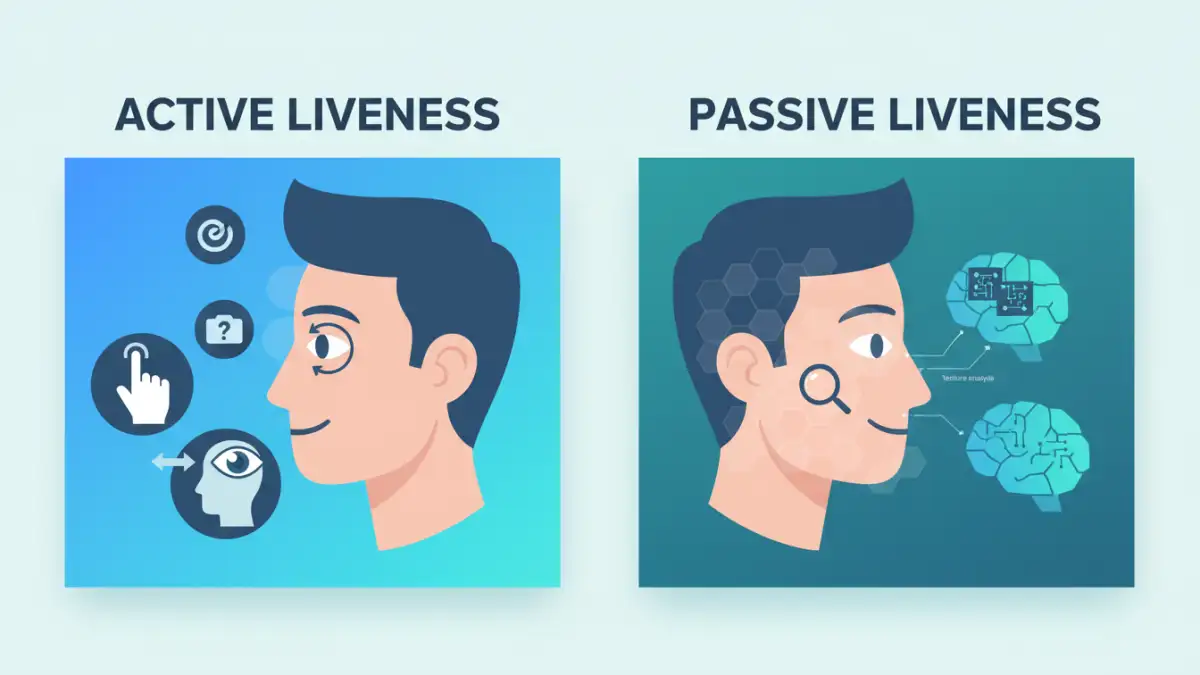
There are two primary approaches to verifying liveness, each with its own methodology, benefits, and drawbacks. The choice between them often depends on the required security level and the desired user experience.
Active Liveness Detection
Active liveness requires the user to perform a specific action or a series of 'challenges' to prove they are real. The system might ask the user to blink, smile, nod, or turn their head from side to side. The system then analyzes whether the facial movements are natural and correspond to the prompts.
From a development standpoint, this method is often easier to implement because the expected responses are well-defined. However, it introduces friction into the user experience. The instructions can sometimes be unclear, leading to user frustration and failed attempts, especially in poor lighting or with non-standard camera angles.
Passive Liveness Detection
Passive liveness is the more advanced and user-friendly approach. It works seamlessly in the background during a normal facial scan without requiring any specific actions from the user. The AI analyzes the video feed for subtle, involuntary cues that indicate a live person.
These cues can include micro-movements of the skin, light reflections off the eyes and skin texture, pulse detection from minute color changes in the face, and other subtle distortions that are present in a live video but absent in a static photo or replay. This form of facial recognition security provides a frictionless experience while offering a very high degree of protection against spoofing.
Implementing Liveness Detection in Document Workflows
Integrating liveness detection isn't just a theoretical concept; it has powerful, practical applications for securing document access. As engineers, we can integrate these checks at critical points in a document's lifecycle.
For example, when a user needs to access a highly confidential M&A document or sign a multi-million dollar contract, a liveness check can be triggered. The user simply looks into their device's camera, the system verifies their liveness and matches their face to their stored biometric profile, and access is granted. This entire process can take just a couple of seconds with a passive system.
Many cloud providers like AWS (Amazon Rekognition) and Microsoft (Azure AI Face) offer powerful APIs that handle the complex AI modeling. This allows development teams to integrate sophisticated liveness detection capabilities into their applications without having to build the underlying technology from scratch. We can simply send a video stream to the API and receive a liveness score in return.
Challenges and the Future of Document Security
Despite its benefits, liveness detection is not without challenges. User consent and data privacy are paramount. Biometric data is highly sensitive, and systems must be designed with robust security and clear policies on how data is stored, processed, and deleted. Algorithmic bias is another concern; models must be trained on diverse datasets to ensure they work accurately for people of all ethnicities, ages, and genders.
The future of secure document liveness detection lies in making it even more seamless and robust. We're seeing advancements in multi-modal biometrics, which might combine a passive facial liveness check with voice recognition for an even higher level of assurance. Furthermore, on-device processing is becoming more common, where the liveness check happens directly on the user's phone or computer. This enhances privacy, as the raw biometric data never has to leave the device.
Liveness Detection Method Comparison
| Feature | Active Liveness Detection | Passive Liveness Detection | Best For |
|---|---|---|---|
| User Interaction | Requires user to perform specific actions (e.g., blink, smile, turn head). | No specific user actions required; works in the background. | Passive is better for user experience. |
| User Experience | Can cause friction and frustration if prompts are unclear or fail. | Seamless and fast, leading to higher completion rates. | High-volume or customer-facing applications. |
| Spoof Detection | Detects spoofs by analyzing response to challenges. | Analyzes subtle physiological cues like texture, reflection, and micro-movements. | Both are effective, but passive is often considered more advanced. |
| Technology | Relies on 3D mapping and movement analysis based on prompts. | Utilizes advanced AI to analyze texture, depth, and light patterns. | Applications requiring state-of-the-art security. |
| Implementation | Generally simpler to integrate as the logic is more straightforward. | More complex AI, often reliant on specialized third-party APIs. | Projects where development speed is a priority. |