
Have you ever uploaded a sensitive file to a cloud service and wondered who could actually see it? It's a common concern. We trust these platforms with our data, but standard encryption often leaves a gap: the service provider holds the keys. This means, in theory, they or a malicious actor with access to their servers could decrypt your files.
This is the exact problem that a more robust security model solves. It's an architecture designed to make it mathematically impossible for the service provider to access your unencrypted data. They store your encrypted files, but they have absolutely no knowledge of the keys required to unlock them.
Table of Contents
What Is Zero-Knowledge Architecture?
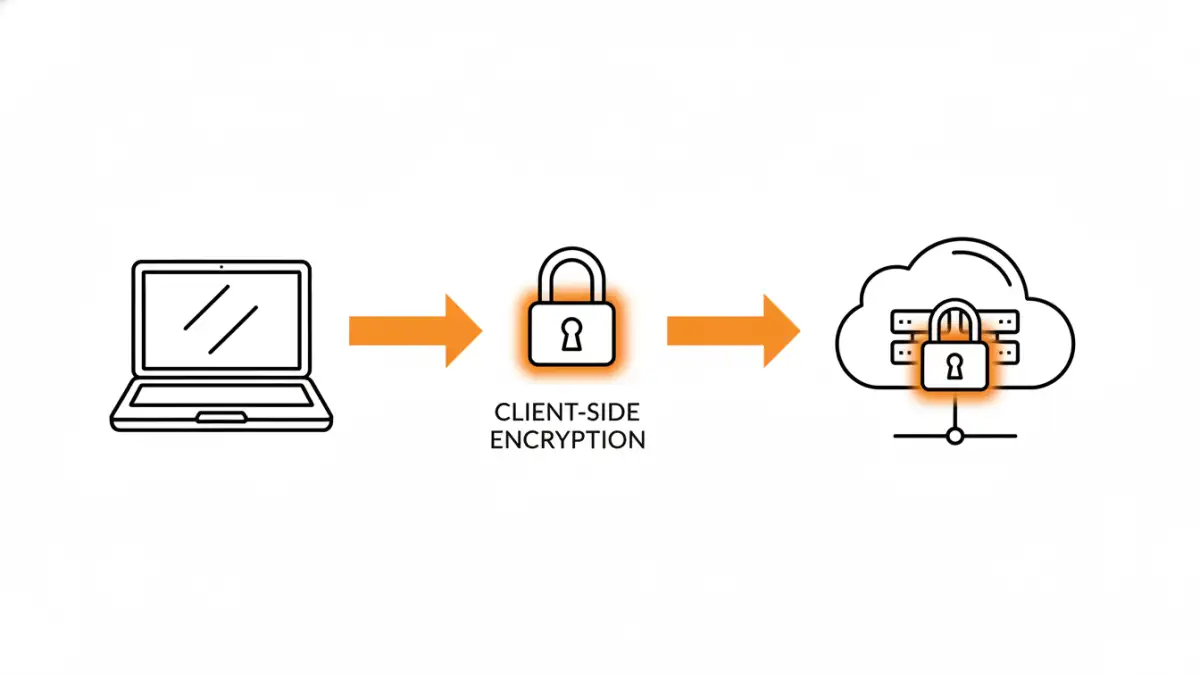
At its core, a zero-knowledge system is built on the principle of client-side encryption. This means all encryption and decryption processes happen directly on your device (the client) before any data is transmitted to the server. The server only ever receives and stores an already-encrypted blob of data.
The term 'zero-knowledge' refers to the provider's perspective. They have zero knowledge of your password, your encryption keys, and the content of your files. Think of it like a bank that gives you a safe deposit box but doesn't keep a copy of your key. They can protect the box, but they can never open it.
The 'Zero-Knowledge' Principle Explained
This principle is often associated with Zero-Knowledge Proofs (ZKP), a cryptographic concept where one party can prove to another that a statement is true without revealing any information beyond the validity of the statement itself. While ZKP for documents is an emerging field, the architectural principle in cloud storage is more direct: prove you have the right key by successfully decrypting the data on your own device, without ever sending the key to the server.
Beyond Standard Encryption
Many services advertise 'at-rest' and 'in-transit' encryption. Encryption in-transit (using TLS/SSL) protects data from being snooped on as it travels across the internet. Encryption at-rest protects the data on the company's servers from physical theft. However, in both cases, the service provider often manages the encryption keys. A zero-knowledge approach adds a crucial third layer, ensuring the provider can't access data even when it's at rest on their servers.
How It Works in Practice for File Sharing

The workflow for a zero-knowledge system is seamless for the user but fundamentally different on the backend. From my work building secure systems, the beauty is in its simplicity from a user's perspective, even though the cryptography is complex.
Client-Side Key Generation
When you create an account, your password is used to generate a powerful encryption key directly within your browser or on your desktop app. This key is never sent to the service's servers. Instead, it's used immediately to encrypt your files before they are uploaded. This is the most critical step in the entire process.
The Server's Limited Role
The server's job is reduced to storing and synchronizing these encrypted files. When you log in from a new device, the encrypted data is downloaded, and your password (which only you know) is used to decrypt it locally. The server is essentially a blind, trusted courier, moving locked boxes without ever knowing what's inside.
Why This Model Matters for Collaboration
The implications for private file sharing are significant. For teams in legal, finance, or healthcare, this isn't just a feature; it's a requirement. It ensures that client confidentiality and regulatory compliance (like HIPAA or GDPR) are structurally enforced.
When you share a file with a colleague, you are not sending them the file directly. Instead, you are securely sharing the decryption key for that specific file with them, typically through a public-key cryptography mechanism. Their device then uses that key to decrypt the file locally. The provider facilitates the secure key exchange but never has access to the keys themselves.
Ultimate User Control
This model puts the user in complete control. Since you are the only one with the key, you are the only one who can grant access, view your files, or permanently delete them. This mitigates risks from rogue employees at the cloud provider, government subpoenas demanding data, or external data breaches targeting the provider's servers.
Clearing Up Common Misconceptions
One common point of confusion is the difference between zero-knowledge and end-to-end encryption. While related, they aren't always the same. End-to-end encryption (E2EE) focuses on securing communication between two endpoints, like in a messaging app. The service in the middle can't read the messages.
A zero knowledge file encryption system is a broader architectural choice for cloud storage that uses E2EE as a component. It ensures that data is encrypted from the moment it leaves your device until it's decrypted on a recipient's device, with the server remaining 'blind' throughout the entire storage and sharing lifecycle. The main takeaway is the responsibility: with zero-knowledge, if you lose your password, your data is irrecoverable because the provider can't reset it for you.
Encryption Model Comparison
| Encryption Model | Key Management | Provider Access | Best For |
|---|---|---|---|
| Standard (At-Rest/In-Transit) | Provider Manages Keys | Yes, provider can decrypt data | General-purpose cloud storage, non-sensitive files |
| End-to-End Encryption (E2EE) | User Manages Keys | No, provider cannot read communications | Secure messaging, real-time communication |
| Zero-Knowledge Architecture | User Manages Keys | No, provider cannot decrypt stored data | Secure collaboration tools, storing highly sensitive documents |