
Forged diplomas, fraudulent property titles, tampered legal contracts—these aren't just plot points in a movie. They represent a fundamental weakness in how we trust and verify important documents. For years, we've relied on centralized authorities like notaries and government databases, but these systems can be slow, expensive, and critically, vulnerable to manipulation or a single point of failure.
This is a problem I've seen firsthand when building systems that rely on trusted data. A single compromised server or a malicious internal actor can undermine the integrity of an entire database. This has led many of us in the tech field to look for a more robust solution, and blockchain technology has emerged as a powerful contender.
Table of Contents
The Flaws in Traditional Document Verification
Our current systems for verifying documents are built on a foundation of centralized trust. You trust a university to confirm a degree, a government agency to validate a land title, or a bank to attest to a financial statement. This model works, but it has inherent vulnerabilities.
Centralized databases are prime targets for cyberattacks. A breach can lead to data alteration or theft, rendering the records unreliable. Furthermore, the verification process is often manual and bureaucratic, involving paperwork, phone calls, and long wait times. This friction not only costs time and money but also creates opportunities for human error and fraud.
How Blockchain Offers a New Paradigm

Blockchain technology fundamentally changes the trust model from centralized to decentralized. Instead of relying on a single entity to maintain a ledger of records, it uses a distributed network of computers. This structure introduces unique properties that are ideal for document verification.
Immutable Records and Cryptographic Hashing
At its core, a blockchain is a chain of blocks, where each block contains a batch of transactions. Once a block is added to the chain, it is cryptographically linked to the one before it, creating an unbroken and unalterable chain. These are what we call immutable records. Attempting to change a record in one block would require altering every subsequent block, an effort that is computationally infeasible.
To secure a document, we don't store the document itself on the blockchain. Instead, we generate a unique cryptographic hash—a fixed-length string of characters that acts as a digital fingerprint. Even a tiny change to the document, like adding a single comma, results in a completely different hash. This hash is what gets recorded on the blockchain.
Decentralized Verification and Transparency
Because the ledger is distributed across thousands of nodes, there is no single point of failure. No single person or organization can alter the records without the consensus of the network. This creates a transparent system where anyone with access can verify a document's authenticity.
This approach to decentralized document storage of the *proof* (the hash), not the document itself, ensures privacy while providing public verifiability. The document can remain confidential, while its integrity can be checked against the public ledger at any time.
The Mechanics of Verifying a Document on Blockchain
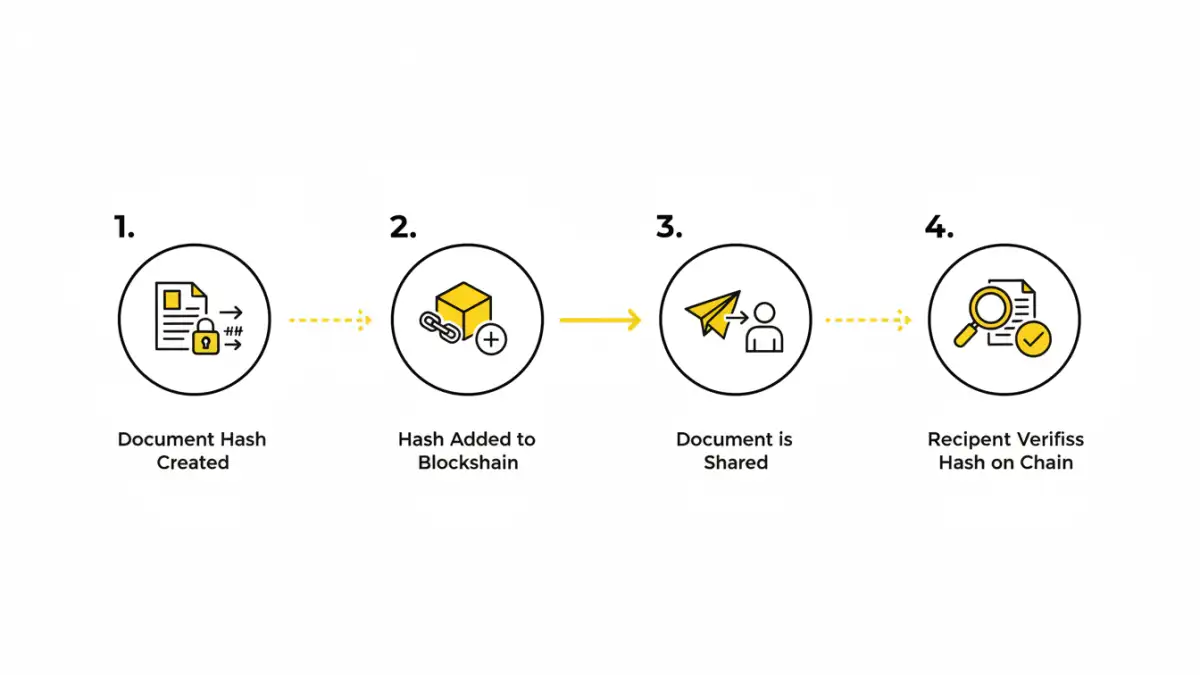
The process of using the blockchain for verification is surprisingly straightforward from a conceptual standpoint. It involves two main stages: anchoring the document and later verifying it.
- Anchoring (Registration): The owner of a document uses an algorithm to generate its cryptographic hash. This hash, along with a timestamp, is included in a transaction that is then added to a block on the blockchain. This process is often referred to as document timestamping, as it creates proof that the document existed in a specific state at a specific time.
- Verification: To verify the document later, a user takes the document in question and generates a new hash using the same algorithm. They then query the blockchain to see if that exact hash exists. If it does, they can be certain the document is authentic and has not been tampered with since it was originally anchored.
This system can form the basis for verifiable credentials, where digital certificates for achievements or qualifications can be issued and verified without needing to contact the issuing institution directly every time.
Real-World Applications and Current Hurdles
The potential for blockchain document security is vast. Universities are exploring it for issuing tamper-proof diplomas. Governments are using it to create secure land registries to prevent property fraud. In supply chain management, it's used to verify the authenticity of shipping manifests and certificates of origin.
However, adoption isn't without its challenges. The cost of transactions on public blockchains like Ethereum can be a barrier. Scalability is another concern; some blockchains can only handle a limited number of transactions per second. Finally, the user experience needs to be simplified for non-technical users to anchor and verify documents easily. Building intuitive interfaces on top of this complex technology is where much of the engineering work is focused today.
Verification Methods: Traditional vs. Blockchain
| Feature | Traditional Verification | Blockchain Verification |
|---|---|---|
| Trust Model | Centralized (relies on a single authority) | Decentralized (relies on network consensus) |
| Security | Vulnerable to single point of failure and data breaches | Highly secure due to immutability and distribution |
| Speed | Slow, often requires manual checks (days or weeks) | Near-instantaneous, automated verification |
| Cost | Can be high due to administrative overhead | Low per-transaction cost after initial setup |
| Transparency | Opaque; records held by a central entity | Transparent; anyone can verify a hash on the ledger |
| Data Integrity | Records can be altered or deleted | Immutable records cannot be changed or removed |