
I recently helped a client untangle a permissions nightmare. They had a shared cloud folder for a sensitive project with dozens of collaborators, and keeping track of who could access which document was becoming impossible. When a contractor's term ended, revoking their access meant manually combing through folders and files, hoping nothing was missed. This messy, error-prone process is a common symptom of a bigger problem: our digital identity and access controls are fundamentally broken.
We rely on centralized systems—a company server, a Google account, a government database—to vouch for who we are and what we can see. This creates single points of failure and puts our data in the hands of others. But a new paradigm is emerging, one that puts control back where it belongs: with the individual.
Table of Contents
The Problem with Centralized Document Access
For years, we've secured documents with passwords, access control lists (ACLs) on servers, or permissions managed by cloud providers like Microsoft 365 and Google Workspace. While functional, these systems are brittle. Passwords can be shared, phished, or forgotten. When an employee leaves a company, an administrator has to manually revoke their access from every system, a process often called 'de-provisioning'.
This centralized model means that the platform provider holds all the keys. If their system is breached, every user's access is at risk. It also creates a frustrating user experience, forcing us to juggle countless usernames and passwords. From a development standpoint, building and maintaining these permission systems is complex and costly, and getting it wrong has serious security implications.
What Is Decentralized Identity?

Decentralized identity flips the traditional model on its head. Instead of relying on a central authority, it uses a framework where individuals own and control their own digital identities. This concept is often referred to as self-sovereign identity (SSI). It’s built on a few core technological pillars that work together.
Core Concepts: DIDs and Verifiable Credentials
At the heart of this system are two key components: Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs). Think of a DID as your permanent, self-owned address on the internet—like a phone number you own forever, regardless of your carrier. It doesn't contain any personal information itself; it's just a unique identifier that you control.
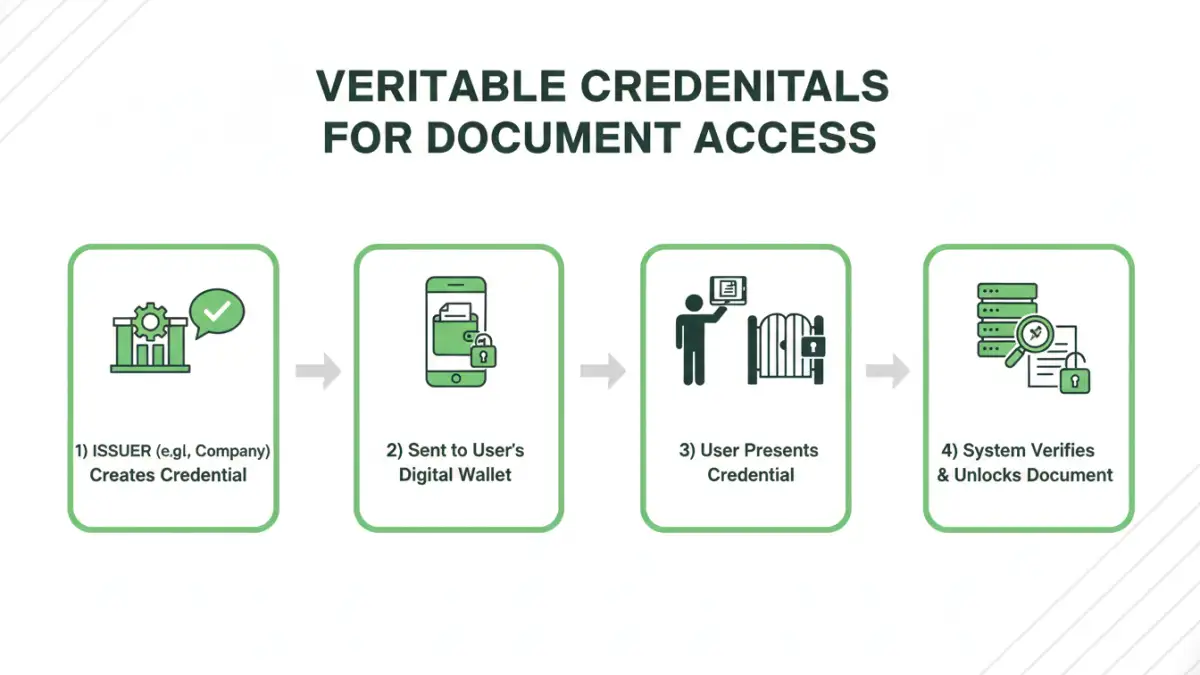
Verifiable Credentials are the digital equivalent of a driver's license or a university degree. They are tamper-proof, cryptographically signed statements issued by one entity to another. For example, a university could issue a VC to your DID confirming you graduated. You can then present this VC to a potential employer without the employer needing to contact the university directly. The credential's cryptographic signature proves its authenticity.
The Role of Blockchain Technology
So where does the trust come from? Often, it's anchored in a distributed ledger or blockchain. The public keys associated with DIDs are registered on the blockchain, creating a decentralized and uncensorable directory. This allows anyone to look up a DID and verify signatures without relying on a single company's database. This use of blockchain identity management ensures that the system is resilient and trustworthy.
How Decentralized Identity Secures Documents: A Scenario
Let's move from theory to a practical application. Imagine a healthcare provider needs to share a patient's medical records (as a PDF) with a specialist at another hospital. The traditional method involves faxes, secure email portals, or direct system integrations—all of which are cumbersome.
With a decentralized document security model, the process is much cleaner:
- Issuing the Credential: The patient's primary care provider issues a Verifiable Credential to the specialist's DID. This VC acts as a temporary, single-use key, stating, "Dr. Smith is authorized to view Patient Jane Doe's records for the next 48 hours."
- Encrypting the Document: The medical record PDF is encrypted. The rules for decryption are bound to the VC; only the holder of the DID to which the VC was issued can decrypt it. This is a powerful use case for verifiable credentials for pdfs.
- Accessing the Document: The specialist presents their VC from their digital wallet. The system cryptographically verifies the credential's authenticity and that it was issued to the specialist's DID. If everything checks out, the document is decrypted and displayed.
- Revoking Access: After 48 hours, the VC automatically expires. Alternatively, if the patient revokes consent, the primary care provider can instantly revoke the VC on the blockchain, making it impossible for the specialist to access the document again.
In this model, no passwords were exchanged. Access was granted for a specific purpose and duration, and the entire interaction is auditable and secure.
Key Benefits Over Traditional Methods
Adopting this approach brings significant advantages over the systems we use today. It's not just a marginal improvement; it's a fundamental shift in how we manage trust and access in the digital world.
- Granular Control: You can grant access to a specific document, for a specific person, for a specific amount of time, without giving them broad access to a folder or system.
- Enhanced Privacy: Users only share the specific credential needed for a transaction (e.g., "I am over 18") without revealing their entire identity. This minimizes data exposure.
- Instant, Ironclad Revocation: Access can be revoked instantly and verifiably. There's no ambiguity about whether a former employee can still open that old file.
- Interoperability: Because DIDs and VCs are based on open standards, they can work across different systems and platforms, breaking down data silos.
- Secure Document Signing: The same cryptographic principles can be used for secure document signing. A VC can serve as proof that a specific identity reviewed and approved a document, creating a legally binding and tamper-proof signature.
Comparison: Traditional vs. Decentralized Access Control
| Feature | Traditional Access Control (Passwords, ACLs) | Decentralized Access Control (DIDs & VCs) |
|---|---|---|
| Identity Control | Controlled by a central provider (e.g., Google, your company). | Controlled by the individual (Self-Sovereign). |
| Access Granting | Broad permissions are assigned to user accounts (e.g., folder access). | Specific, time-bound credentials are issued for specific resources. |
| Access Revocation | Manual, slow, and prone to error. Lingering access is a common risk. | Instant, cryptographic, and verifiable on a distributed ledger. |
| Privacy | Users often over-share personal data to prove identity. | Selective disclosure; users only present the necessary credential. |
| Audit Trail | Logged in a central database, which can be altered or compromised. | Often logged on an immutable blockchain for a tamper-proof record. |
| Interoperability | Locked into specific platforms (siloed). | Based on open standards, designed to work across any system. |