I recently helped a colleague who was in a tight spot. He'd found an old encrypted archive from a project years ago, containing critical source code. The problem? He remembered the password was a long, complex phrase he'd created to be 'unbreakable'—and he'd succeeded a little too well. He couldn't remember it exactly, and this scenario highlights a common and difficult problem in data security.
When you're faced with a situation like this, the question isn't just about finding the right tool; it's about understanding the mathematical and computational barriers you're up against. The length and complexity of a password don't just add a little difficulty; they increase the recovery time exponentially.
Table of Contents
The Challenge: Encryption and Password Length
Modern encryption standards, like AES-256 (Advanced Encryption Standard with a 256-bit key), are the backbone of secure archives like ZIP, RAR, and 7z. This standard is incredibly robust. There is no known practical attack that can break the encryption itself. The only viable path is to find the correct password.
This is where password length becomes the deciding factor. A short, simple password can be found using a brute-force attack, where a program tries every possible combination. But as you add characters, the number of potential combinations explodes. A 15-character password with uppercase, lowercase, numbers, and symbols has an astronomical number of possibilities, far beyond what a standard computer can test in a human lifetime.
Understanding Computational Limits
A brute-force attack on a long, truly random password is a non-starter. For instance, attempting to crack a 12-character alphanumeric password with a powerful consumer GPU might take decades or centuries. Increase that to 20+ characters, and you're talking about timeframes longer than the age of the universe. This is why a simple brute-force approach is almost never the answer for a long password.
The Role of the Encryption Algorithm
The file type also matters. Some older ZIP encryption methods are notoriously weak and can be broken regardless of the password. However, any modern archive using AES encryption relies entirely on the password's strength. The algorithm itself won't give you a shortcut, which is why your strategy must focus on finding the password intelligently, not breaking the encryption.
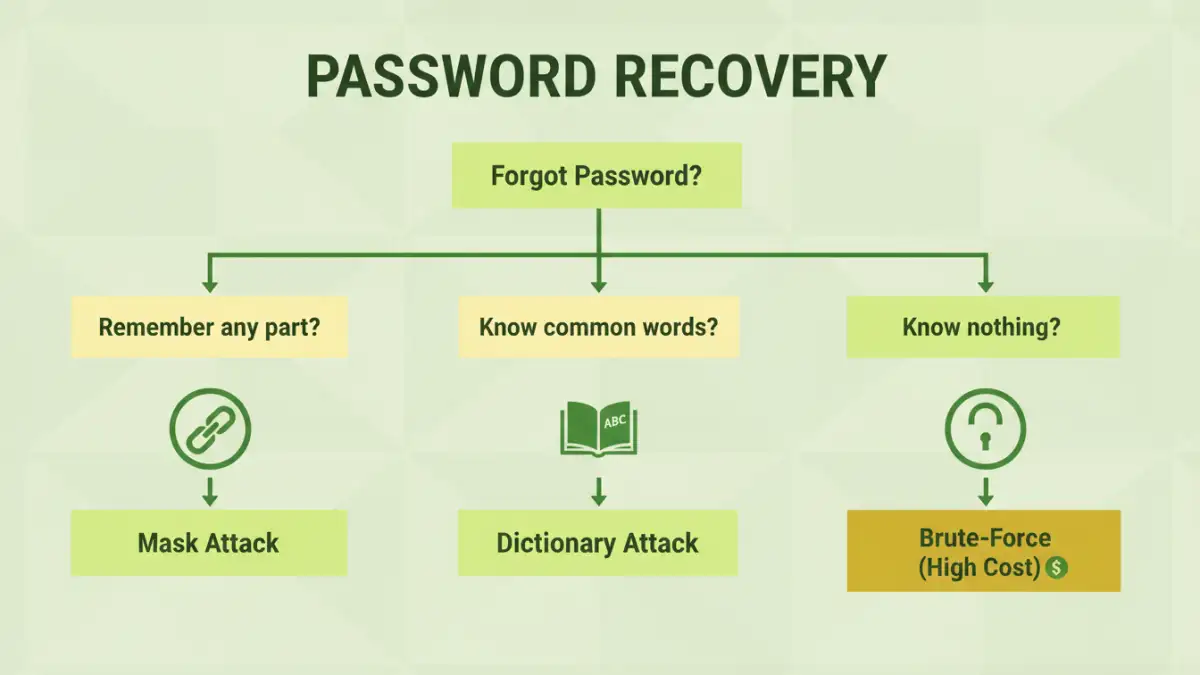
Realistic Password Recovery Strategies
Since brute-forcing every combination is off the table for long passwords, we have to use more intelligent methods. The goal is to reduce the number of possibilities from trillions upon trillions to something manageable. Your ability to recover an encrypted file password often depends on what you remember about it.
Mask Attacks: Your Most Powerful Tool
A mask attack is the most effective technique if you remember parts of the password's structure. You provide the recovery software with a 'mask' or pattern. For example, if you remember the password was a company name, followed by four numbers, and ended with an exclamation mark, you could define a mask like `CompanyName?d?d?d?d!`. Here, `?d` represents any digit. This dramatically shrinks the search space from all possible characters to just 10,000 combinations (0000 to 9999), a task that takes seconds.
Dictionary and Hybrid Attacks
If you don't remember a specific structure but suspect the password was based on common words or phrases, a dictionary attack is useful. This method uses a list of words, names, and common passwords. A hybrid attack builds on this by adding variations, such as appending numbers or symbols to dictionary words (e.g., `password2024` or `secret!`). For long password recovery, this is only effective if the password was based on a combination of dictionary words.
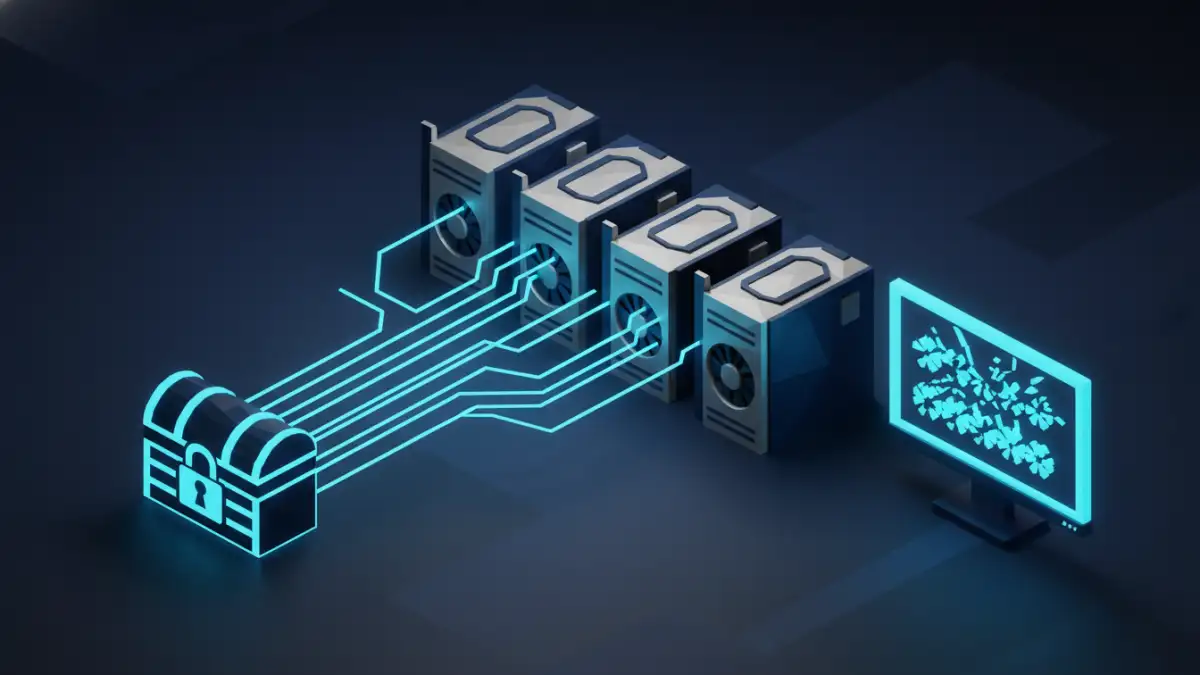
Leveraging Hardware for Complex Password Cracking
Even with smart attacks, the number of guesses can still be massive. This is where specialized hardware, specifically Graphics Processing Units (GPUs), comes into play. A modern GPU contains thousands of small processing cores designed for parallel computation, making them incredibly efficient at the repetitive math involved in checking password hashes.
A high-end consumer GPU can test billions of password combinations per second, compared to millions on a powerful CPU. For any serious attempt at complex password cracking, using GPU-accelerated software like Hashcat or specialized commercial tools is essential. Without it, the time required for even a well-defined mask attack on a moderately long password could be impractical.
When Recovery Is Practically Impossible
It's important to be realistic. If the password is truly long (e.g., 25+ characters), completely random (not based on words or patterns), and was used to encrypt a file with AES-256, recovery is effectively impossible with current technology. This is the reality of modern cryptography—it's designed to be unbreakable.
In these cases, no amount of hardware or clever software can help. The computational power required to brute-force such a password does not exist on a public scale. This is why password managers are so critical for storing these ultra-secure, randomly generated passwords. If you lose the password and have no memory of its structure, the data is likely lost for good.
Password Recovery Attack Comparison
| Attack Type | Description | Effectiveness on Long Passwords | Best For |
|---|---|---|---|
| Brute-Force | Tries every possible character combination. | Extremely Low / Impractical | Very short passwords (under 8 characters) with a known character set. |
| Dictionary Attack | Uses a pre-compiled list of words and common passwords. | Low | Passwords based on single, common words without modifications. |
| Hybrid Attack | Combines dictionary words with patterns (e.g., adding numbers/symbols). | Moderate | Passwords based on dictionary words with common variations (e.g., 'Password123!'). |
| Mask Attack | Targets passwords where parts of the structure are known. | High | The most effective method for long password recovery when you remember patterns, fixed parts, or character types. |